Month: May 2025

How to Track or Erase a Lost or Stolen Phone
Have you ever experienced the panic of losing your phone? It’s a sinking feeling, isn’t it? Your entire world is often contained within that little device. Luckily, there are ways to track or even erase your lost or stolen phone. This article provides essential steps to locate or wipe your lost or stolen phone, ensuring…
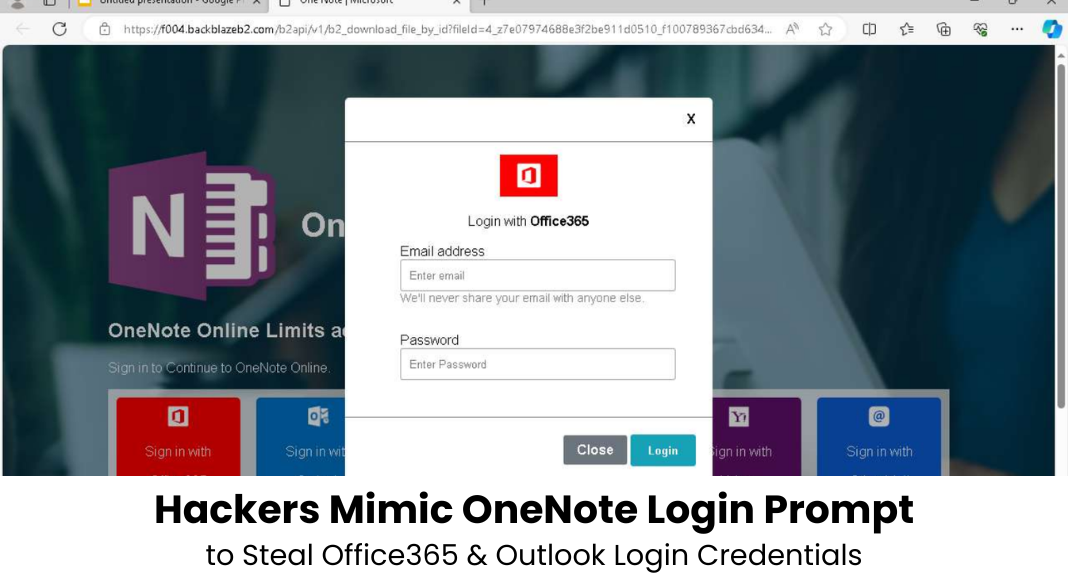
How to Stop Clickjacking Attacks
Clickjacking attacks are a serious threat to web security. These attacks can trick users into clicking on invisible elements, leading to unauthorized actions. Imagine you’re trying to click a button to download a file, but instead, you’re unknowingly clicking something completely different. Scary, right? This is why understanding how to stop clickjacking is crucial for…