A newly disclosed vulnerability, named the WireTap assault, permits attackers with bodily entry to interrupt the safety of Intel’s Software program Guard eXtensions (SGX) on trendy server processors and steal delicate data.
A analysis paper launched in October 2025 particulars how this technique can extract cryptographic keys from supposedly safe SGX enclaves utilizing a low-cost setup, difficult the foundational belief positioned in these hardware-based safety environments.
The assault undermines the confidentiality and integrity ensures of SGX, a know-how extensively used to guard delicate information and computation, even from privileged software program.
The researchers demonstrated that bodily assaults, as soon as believed to require costly and specialised gear, can now be executed by hobbyists on a funds of lower than $1,000.
WireTap Assault
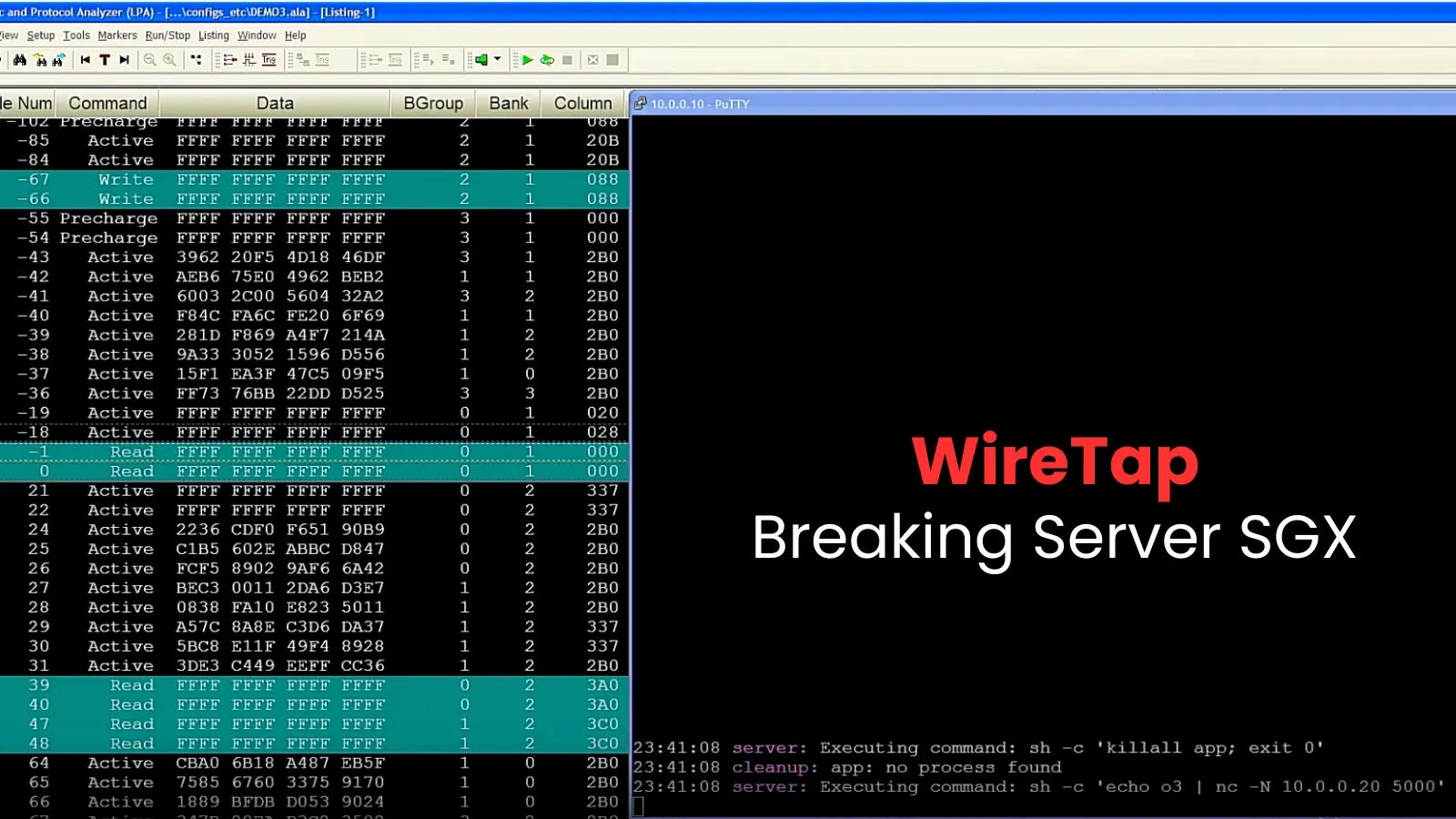
The core of the WireTap assault is a custom-built reminiscence interposition probe that bodily faucets into the DRAM bus, permitting the attacker to watch the info shifting between the CPU and the system’s reminiscence.
The researchers constructed this software utilizing available parts from second-hand digital marketplaces, together with a easy DIMM riser board, tweezers, and a soldering iron.
A key innovation was slowing down the system’s high-speed DDR4 reminiscence bus. By modifying the DIMM’s metadata, the researchers compelled the system to function at a a lot decrease frequency.
This important step made it doable to seize the info visitors utilizing outdated and cheap logic analyzers not initially designed for contemporary {hardware}.
This method shatters the long-held assumption that bodily reminiscence assaults on server-grade techniques have been out of attain for all however probably the most well-funded adversaries.
The assault particularly targets Scalable SGX, the model utilized in Intel’s Xeon server processors, which depends on a deterministic reminiscence encryption scheme referred to as AES-XTS.
In contrast to older SGX implementations, this scheme produces the identical ciphertext every time the identical information is written to the identical bodily reminiscence deal with.
The WireTap setup permits attackers to watch these encrypted reminiscence transactions in real-time. By fastidiously controlling an SGX enclave and forcing it to carry out cryptographic operations, the researchers have been in a position to mount a ciphertext side-channel assault.
They noticed the encrypted reminiscence visitors throughout the technology of an ECDSA signature, a course of used for SGX attestation. This allowed them to construct a dictionary of ciphertexts and recuperate the key nonce used within the signing operation.
With the nonce and the general public signature, they efficiently extracted the machine’s personal DCAP attestation key from a completely trusted server in underneath 45 minutes.
The implications of extracting an SGX attestation key are extreme, notably for the blockchain and Web3 ecosystems that depend on SGX for safety.
Many decentralized networks, with market caps totaling a whole bunch of thousands and thousands of {dollars}, use SGX to make sure confidential transactions and the integrity of computation.
The researchers demonstrated end-to-end assaults on a number of real-world SGX deployments. For privacy-preserving sensible contract networks like Phala and Secret, a compromised key would permit an attacker to forge quotes, run malicious enclaves, and extract grasp keys, enabling network-wide decryption of confidential transactions.
On decentralized storage networks like Crust, an attacker might faux proofs of storage, permitting them to assert monetary rewards with out truly storing any information, thereby breaking the system’s integrity ensures. The researchers have disclosed their findings to Intel and the affected blockchain tasks.
Observe us on Google Information, LinkedIn, and X for day by day cybersecurity updates. Contact us to characteristic your tales.