Ransomware operators have shifted from opportunistic malware distribution to extremely focused campaigns that exploit official software program for stealth and persistence.
Rising in early 2025, a number of ransomware households started abusing in style distant entry instruments—resembling AnyDesk and Splashtop—to ascertain footholds inside enterprise networks.
By hijacking or silently putting in these utilities, adversaries bypass safety controls that historically belief signed installers, enabling preliminary entry with out tripping typical detection mechanisms.
Organizations quickly found anomalous distant classes connecting from surprising geolocations.
Seqrite analysts recognized that attackers leveraged credential stuffing and phishing to acquire privileged accounts, then deployed distant entry instruments to maneuver laterally.
Quite than relying solely on customized malware binaries, menace actors used present administration frameworks to mix malicious exercise into on a regular basis IT operations, rendering their actions virtually invisible to legacy endpoint protections.
The influence of those campaigns has been profound. Victims report encrypted file shares, disabled backups, and altered Distant Entry Software credentials to lock out directors.
In high-profile intrusions attributed to LockBit and Black Basta variants, attackers mixed RAT abuse with file-shredding instructions to eradicate forensic traces, lengthen dwell time, and maximize ransom calls for.
Organizations suffered expensive downtime and information loss, underscoring the urgency of reevaluating belief in routine IT utilities.
A important enabler of those ransomware operations is the attackers’ capacity to keep up persistent management by means of run-of-the-mill distant administration software program.
Two main strategies emerged: hijacking preinstalled instruments to keep away from file creation and deploying light-weight installers through command-line flags.
Within the hijacking state of affairs, adversaries enumerate put in purposes by means of Home windows Administration Instrumentation or PowerShell, then inject malicious credentials or modify JSON configuration information to grant unattended entry beneath the attacker’s account.
This method leaves no new executables on disk and evades antivirus scanning by abusing trusted executables already whitelisted in enterprise insurance policies.
When opportunistic targets lack preexisting distant entry utilities, attackers fall again on silent set up.
Utilizing recognized installer parameters, they deploy signed binaries with minimal noise:-
Begin-Course of -FilePath ‘.AnyDesk.exe’ -ArgumentList ‘INSTALL=C’,’STARTWITHWINDOWS=1′,’SILENT=1′ -NoNewWindow
This command installs AnyDesk as a service that launches at boot, granting the adversary persistent entry factors for follow-on operations.
Related flags—resembling VERYSILENT and NORESTART—are documented in vendor manuals but hardly ever monitored by defenders.
As soon as embedded, the distant software runs with elevated privileges if attackers escalate through utilities like TrustedInstaller or PowerRun.
Mixed with registry run-key manipulation and hidden scheduled duties, this chain ensures that even when an incident responder removes one backdoor, a secondary entry path stays.
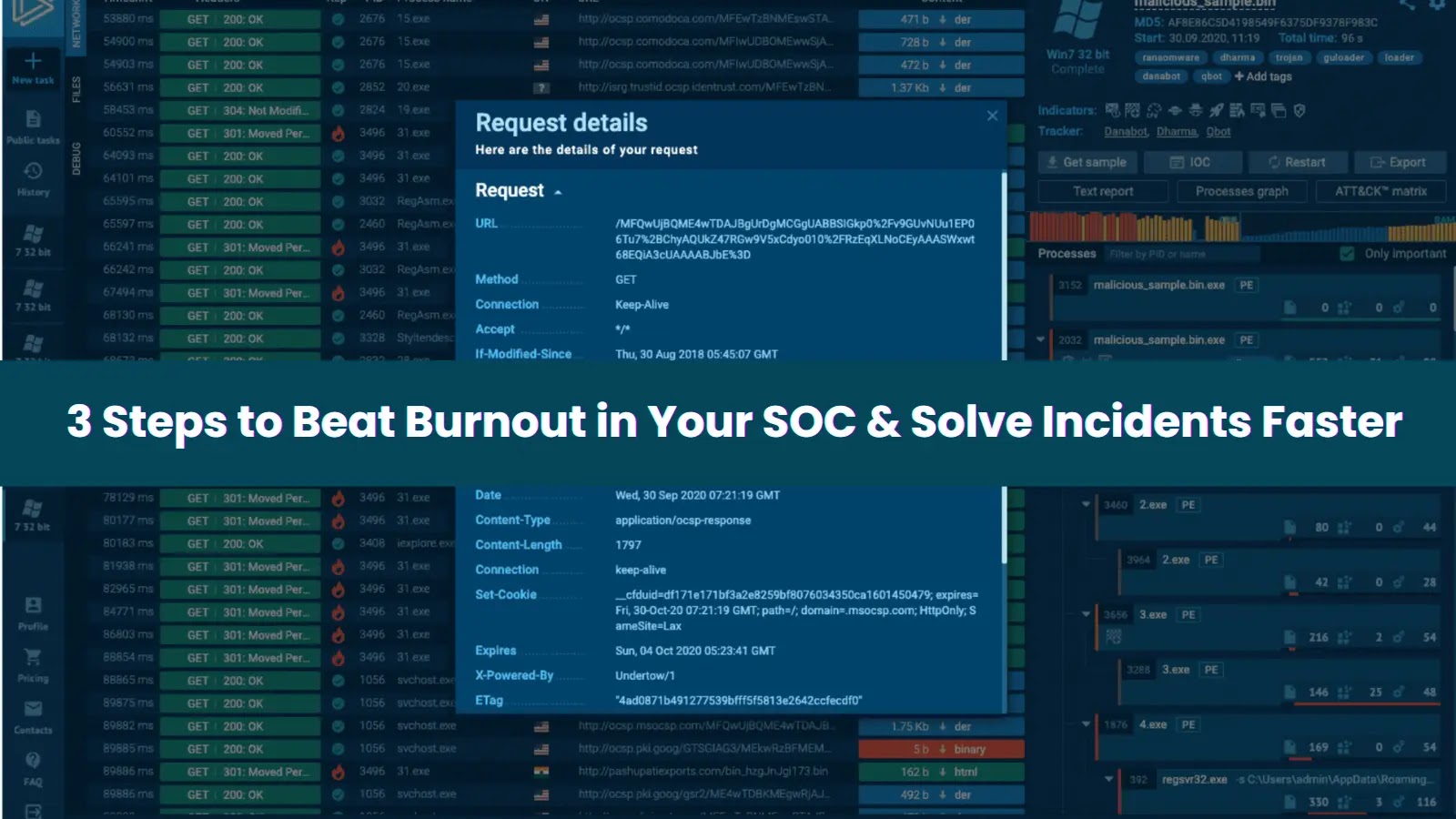
This layered persistence mannequin frustrates remediation efforts and calls for a shift towards behavior-based monitoring that flags anomalous software utilization quite than file signatures.
By abusing trusted distant administration software program, ransomware gangs have turned IT comfort into their most potent weapon.
Defenders should implement strict utility whitelisting, implement multi-factor authentication, and monitor command-line arguments related to frequent distant entry instruments to detect and disrupt these stealthy persistence ways earlier than encryption can happen.
Comply with us on Google Information, LinkedIn, and X to Get Extra On the spot Updates, Set CSN as a Most well-liked Supply in Google.