A newly recognized botnet takes a ‘shotgun’ method to compromising gadgets, packing over 50 exploits focusing on routers, servers, cameras, and different community merchandise, Development Micro stories.
Dubbed RondoDox, the botnet started actions in mid-2025 and was related to the exploitation of CVE-2023-1389, a command injection flaw within the WAN interface of TP-Hyperlink Archer AX21 routers that was disclosed on the Pwn2Own Toronto hacking contest in 2022.
In June, RondoDox was seen focusing on CVE-2024-3721 and CVE-2024-12856, two high-severity weaknesses in TBK DVRs and 4-Religion routers, after which considerably increasing its goal listing.
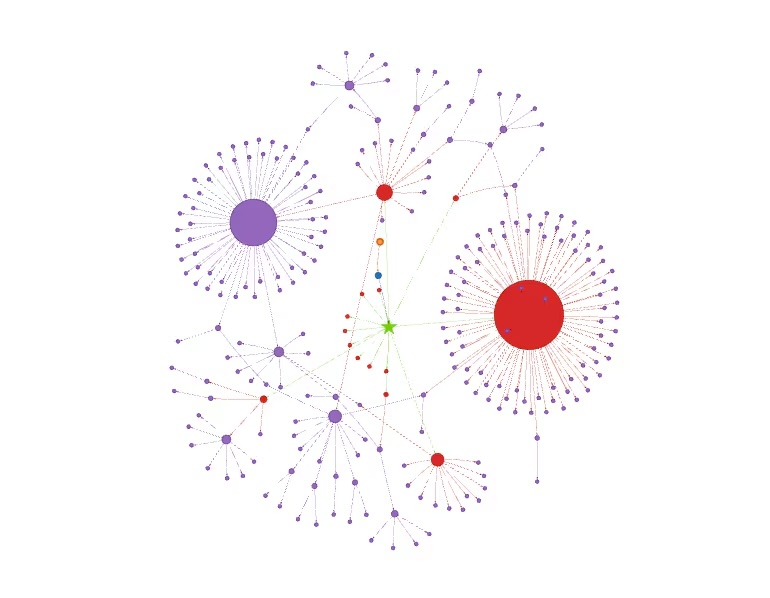
In accordance with Development Micro, the botnet is now focusing on routers, DVRs, NVRs, CCTV techniques, internet servers, and different networking tools from greater than 30 distributors.
RondoDox targets a complete of 56 vulnerabilities, together with 18 that wouldn’t have a CVE identifier assigned. Most of those are command injection bugs and a subset of them was added to the US cybersecurity company CISA’s KEV listing, which underlines the quick want for patching.
In late September, CloudSek warned of a 230% surge within the botnet’s assaults since mid-2025, fueled by the exploitation of weak credentials, unsanitized enter, and previous CVEs.
The contaminated gadgets, the cybersecurity agency identified, are abused for cryptocurrency mining, distributed denial-of-service (DDoS) assaults, and for hacking into enterprise networks.
RondoDox’s operators had been seen quickly rotating infrastructure to evade detection, and RondoDox binaries had been seen being distributed alongside Mirai and Morte payloads.Commercial. Scroll to proceed studying.
“Extra just lately, RondoDox broadened its distribution by utilizing a ‘loader-as-a-service’ infrastructure that co-packages RondoDox with Mirai/Morte payloads — making detection and remediation extra pressing,” Development Micro says.
RondoDox targets ARM, MIPS, and varied Linux architectures. It may launch DDoS assaults utilizing HTTP, UDP, and TCP packets and emulates recognized gaming platforms or impersonates VPN companies to cover the malicious visitors and evade detection.
“The marketing campaign’s shotgun method of focusing on greater than 50 vulnerabilities throughout over 30 distributors underscores the persistent dangers going through organizations that preserve internet-exposed community infrastructure with out enough safety controls,” Development Micro notes.
Associated: Uncovered Docker APIs Possible Exploited to Construct Botnet
Associated: RapperBot Botnet Disrupted, American Administrator Indicted
Associated: Cisco Patches Zero-Day Flaw Affecting Routers and Switches
Associated: GPT-5 Has a Vulnerability: Its Router Can Ship You to Older, Much less Secure Fashions