Google safety researchers just lately uncovered a complicated legal operation referred to as “Lighthouse” that has victimized over a million individuals throughout greater than 120 international locations.
This phishing-as-a-service platform represents one of the vital damaging SMS-based rip-off networks lately, prompting Google to file litigation aimed toward dismantling all the operation.
The assault’s scale reveals how well-organized cybercriminals have turn out to be, deploying coordinated assaults that exploit trusted model names to trick victims into surrendering delicate data.
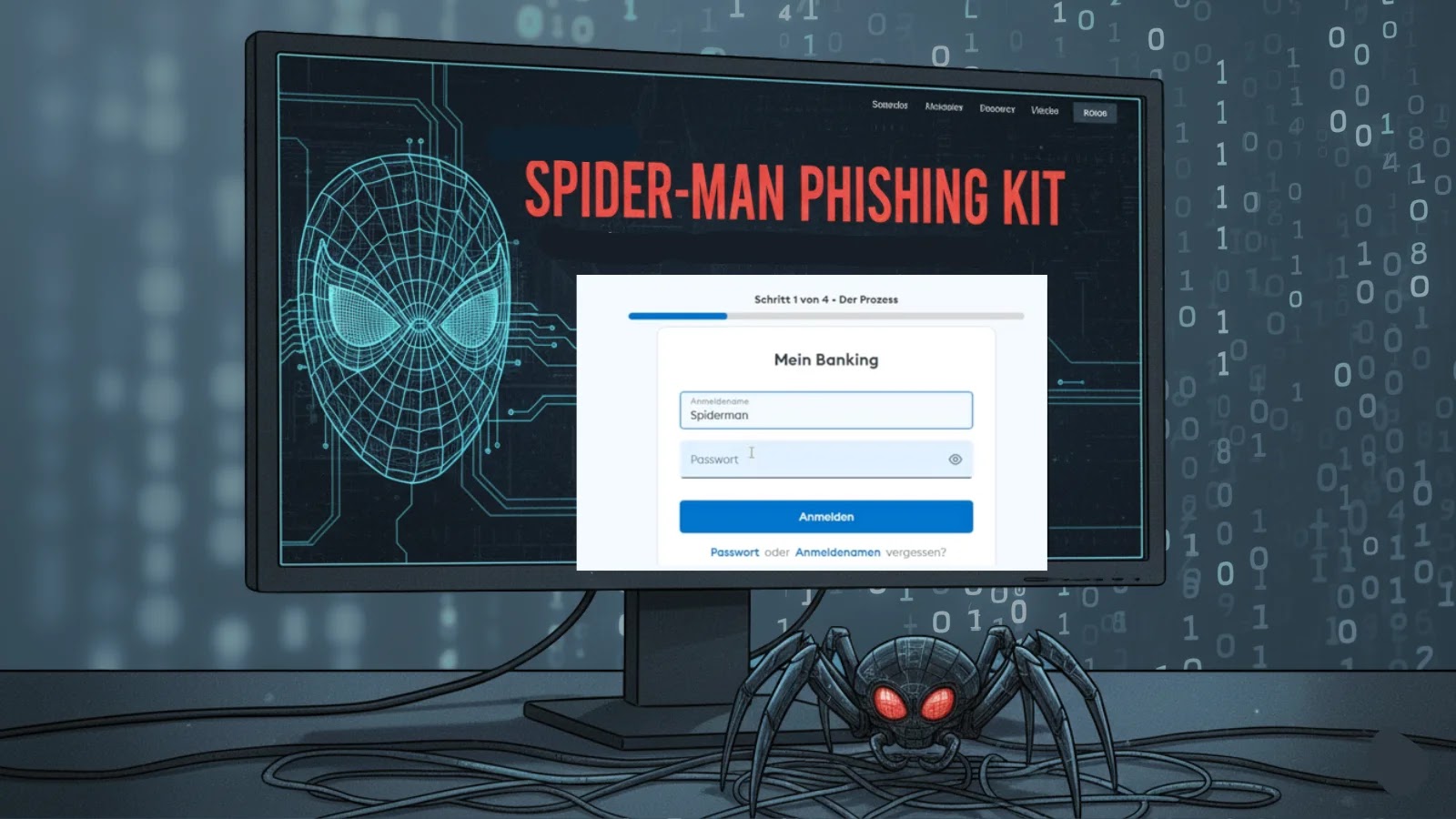
The Lighthouse platform allows attackers to launch large “smishing” campaigns, that are phishing assaults delivered by means of textual content messages relatively than e-mail.
Criminals utilizing this equipment ship misleading SMS messages pretending to come back from reputable firms like E-Z Move, USPS, and toll assortment providers.
These messages sometimes immediate recipients to click on hyperlinks that result in fraudulent web sites designed to steal credentials and monetary knowledge.
Google safety analysts recognized at the very least 107 web site templates that includes Google’s branding on sign-in screens particularly crafted to seem reputable.
These fraudulent web sites requested unsuspecting customers to enter e-mail addresses, passwords, banking credentials, and different delicate data.
The operation has stolen between 12.7 million and 115 million bank cards in the USA alone, representing a big monetary affect to victims.
Technical Infrastructure and Assault Mechanism
The Lighthouse platform operates as a whole legal service providing, offering unhealthy actors with readily-made phishing kits and infrastructure to execute assaults at scale.
The service simplifies the assault course of by permitting operators with minimal technical experience to launch convincing campaigns.
Criminals can customise templates for various goal manufacturers, handle sufferer databases, and harvest stolen credentials by means of a centralized command-and-control infrastructure.
Google’s authorized motion targets the operation beneath a number of legal guidelines, together with the Racketeer Influenced and Corrupt Organizations Act, the Lanham Act for trademark violations, and the Laptop Fraud and Abuse Act.
The corporate can be implementing defensive measures, together with AI-powered detection techniques to flag suspicious messages and expanded account restoration choices to assist compromised customers regain entry to their accounts extra safely.
Comply with us on Google Information, LinkedIn, and X to Get Extra Instantaneous Updates, Set CSN as a Most popular Supply in Google.