A brand new risk concentrating on Chinese language customers has appeared with a harmful potential to close down safety instruments.
RONINGLOADER, a multi-stage loader spreading a modified model of the gh0st RAT, makes use of intelligent tips to bypass antivirus safety.
The malware arrives by way of pretend software program installers that faux to be reliable applications like Google Chrome and Microsoft Groups.
As soon as inside a system, it really works by way of a number of layers of an infection to disable Home windows Defender and in style Chinese language safety merchandise like Qihoo 360 Complete Safety and Huorong.
This marketing campaign exhibits how attackers are getting higher at breaking by way of safety defenses. The malware brings its personal signed driver that appears reliable to Home windows however really helps it kill safety processes.
What makes it harmful is what number of backup plans it has. If one technique to disable safety fails, it tries a number of different approaches.
This exhibits the Dragon Breath APT group behind it has realized from earlier campaigns and improved their strategies.
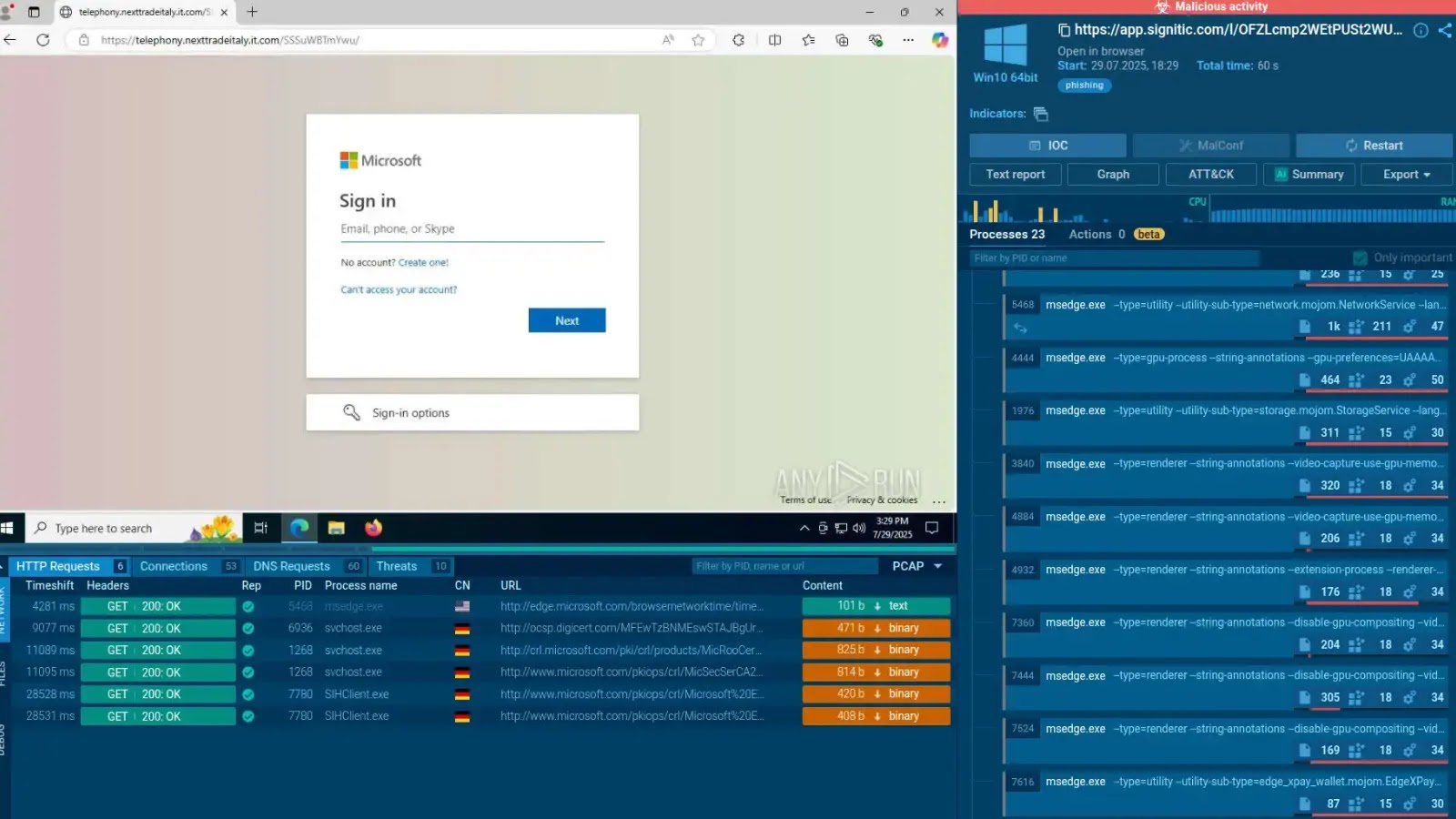
After monitoring detection methods, Elastic safety analysts recognized this marketing campaign utilizing a behavioral rule designed to identify Protected Course of Gentle abuse.
The analysis workforce discovered RONINGLOADER utilizing a way that was publicly documented simply months earlier. The malware takes benefit of a Home windows function meant to guard vital system processes however turns it in opposition to Defender itself.
Assault Methodology and An infection Chain
The an infection begins with a trojanized NSIS installer that drops a number of elements onto the sufferer system. When somebody runs what they suppose is a traditional software program installer, they really activate two separate installers.
RONINGLOADER Execution circulation (Supply – Elastic)
One installs the actual software program to keep away from elevating suspicion, whereas the second quietly deploys the assault chain.
The malware creates a listing at C:Program FilesSnieoatwtregoable and drops two recordsdata: Snieoatwtregoable.dll and an encrypted file referred to as tp.png.
The DLL file decrypts tp.png utilizing a easy however efficient algorithm that mixes XOR encryption with a rotate operation:-
*encrypted_file_content = _ROR1_(*encrypted_file_content ^ xor_key[indx), 4);
After decryption, the malware hundreds recent system libraries to take away any safety hooks which may catch its conduct. It then elevates its privileges utilizing the runas command and scans for working safety software program.
The malware seems to be explicitly for Microsoft Defender, Kingsoft Web Safety, Tencent PC Supervisor, and Qihoo 360 Complete Safety by checking their course of names.
To kill these processes, RONINGLOADER makes use of a signed driver referred to as ollama.sys that was digitally signed by Kunming Wuqi E-commerce Co., Ltd.
The motive force registers a single perform that accepts a course of ID and terminates it utilizing kernel-level APIs that standard safety instruments can’t block.
The malware writes this driver to disk, creates a short lived service to load it, sends the termination command, and instantly deletes the service.
For Qihoo 360, the malware takes further steps by blocking all community connections by way of firewall guidelines earlier than injecting code into the Quantity Shadow Copy service course of.
This injection makes use of Home windows thread swimming pools with file write triggers, a way that helps it keep away from detection.
Observe us on Google Information, LinkedIn, and X to Get Extra Prompt Updates, Set CSN as a Most well-liked Supply in Google.