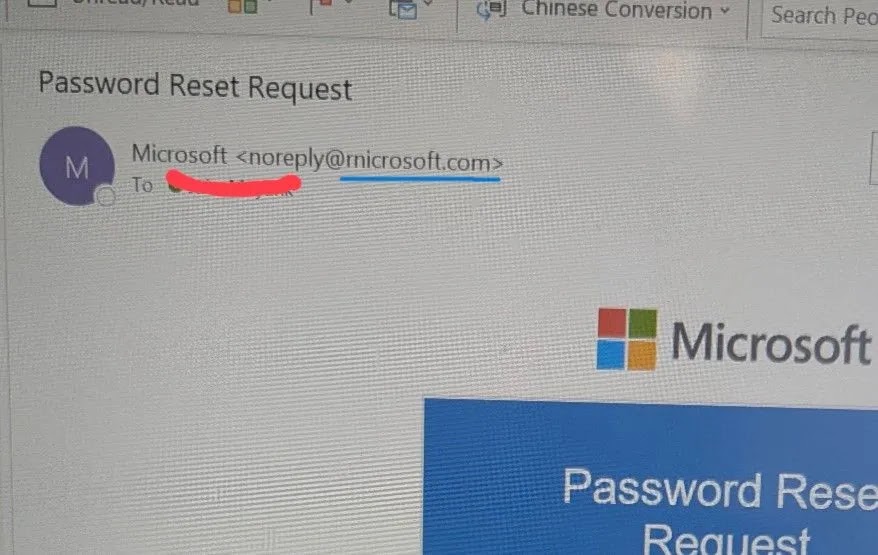
A complicated phishing marketing campaign is at the moment leveraging a delicate typographical trick to bypass consumer vigilance, deceiving victims into handing over delicate login credentials. Attackers make the most of the area “rnicrosoft.com” to impersonate the tech large.
By changing the letter ‘m’ with the mixture of ‘r’ and ‘n’, fraudsters create a visible doppleganger that’s almost indistinguishable from the authentic area at an informal look.
This method, generally known as typosquatting, depends closely on the font rendering utilized in trendy e mail purchasers and net browsers.
When positioned intently collectively, the kerning between ‘r’ and ‘n’ typically mimics the construction of the letter ‘m’, fooling the mind into autocorrecting the error.
Harley Sugarman, CEO of Anagram, lately highlighted this particular vector, noting that the emails typically mirror the official emblem, structure, and tone of authentic Microsoft correspondence.
Visible Deception to Steal Logins
The effectiveness of this assault vector lies in its subtlety. On high-resolution desktop displays, the discrepancy could be seen to a eager observer, however the mind’s tendency to foretell textual content typically masks the anomaly.
The menace turns into much more acute on cellular units, the place display screen actual property is proscribed, and the tackle bar typically truncates the total URL. Attackers exploit this by registering these look-alike domains to facilitate credential phishing, vendor bill scams, and inner HR impersonation campaigns.
As soon as the consumer is satisfied the e-mail is from a trusted entity, they’re extra prone to click on on malicious hyperlinks or obtain weaponized attachments.
The “rn” swap is only one of a number of variations attackers use. Different widespread ways embrace swapping the letter ‘o’ for a zero or including hyphens to authentic model names to create a way of authenticity.
Defending towards these homoglyph and typosquatting assaults requires a shift in consumer habits slightly than relying solely on automated filters. Safety consultants advise that customers should develop the total sender tackle earlier than interacting with any unsolicited e mail.
Hovering over hyperlinks to disclose the precise vacation spot URL or long-pressing the hyperlink on cellular units can expose the deception earlier than a connection is made.
Moreover, analyzing e mail headers, particularly the “Reply-To” discipline, can reveal if a scammer is routing responses to an exterior, uncontrolled inbox.
In eventualities involving sudden password reset requests, the most secure plan of action is to disregard the e-mail hyperlink fully and navigate on to the official service by way of a brand new browser tab.
Organizations are inspired to rehearse these identification eventualities to cease groups from reflexively clicking on familiar-looking notifications.
Frequent Typosquatting Variations
TechniqueVisual ExampleDeception MethodLetter Combinationrnicrosoft(.)comUses ‘r’ and ‘n’ to imitate ‘m’.Quantity Swappingmicros0ft(.)comReplaces the letter ‘o’ with the quantity ‘0’.Hyphenationmicrosoft-support(.)comAdds legitimate-sounding subdomains or suffixes.TLD Switchingmicrosoft(.)coUses a special Prime Degree Area (dropping the ‘m’).
Comply with us on Google Information, LinkedIn, and X for every day cybersecurity updates. Contact us to function your tales.