The software program provide chain is underneath siege from “Shai Hulud v2,” a complicated malware marketing campaign that has compromised 834 packages throughout the npm and Maven ecosystems.
This new wave particularly targets GitHub Actions workflows, exploiting pull_request_target triggers to inject malicious code into broadly used libraries.
The assault has impacted main tasks like PostHog, Zapier, and AsyncAPI, leveraging compromised automation tokens to contaminate downstream dependencies systematically.
The an infection course of depends on a stealthy two-stage loader initiated by a pre-install script named setupbun.js.
This script installs the Bun runtime to execute an obfuscated payload, bunenvironment.js, whereas suppressing commonplace output to keep away from detection throughout construct logs.
By pivoting by compromised CI pipelines, the malware positive aspects privileged entry to repository secrets and techniques, enabling it to switch supply code, increment patch variations, and republish contaminated packages to public registries.
Socket.dev safety analysts recognized the malware’s distinctive persistence mechanism, noting its use of a beacon phrase, “Sha1-Hulud The Second Coming,” successfully looking out GitHub to re-trigger infections.
This ensures that even when particular person repositories are cleaned, the attackers can find and re-compromise weak endpoints.
Marketing campaign’s impression
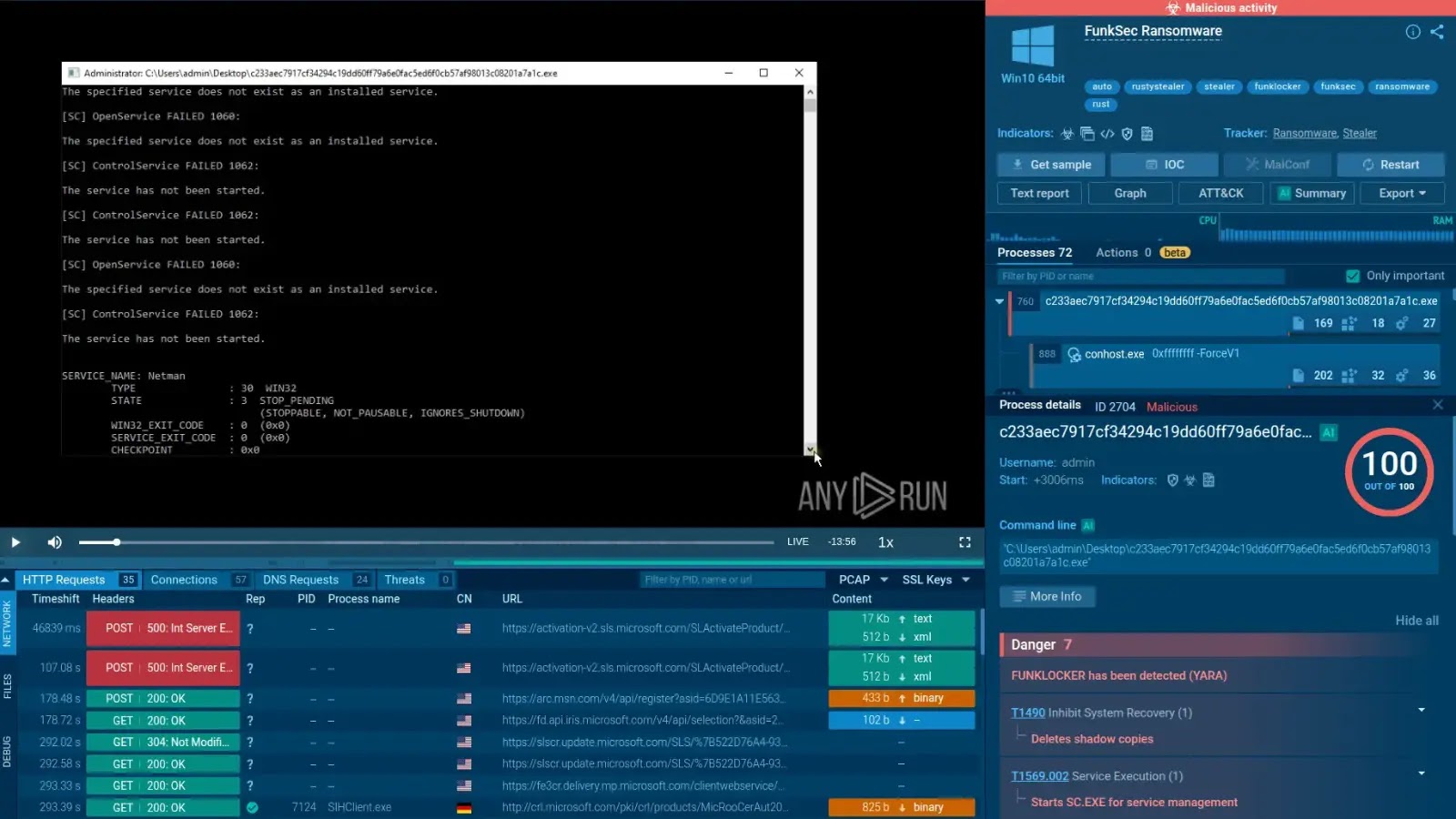
The marketing campaign’s impression is intensive, exposing delicate credentials from tens of hundreds of repositories and marking a harmful evolution in automated provide chain assaults.
As soon as entrenched in a CI atmosphere, the malware executes a complete credential harvesting routine. It captures all out there atmosphere variables, particularly focusing on GITHUB_TOKEN, NPM_TOKEN, and AWS_ACCESS_KEY_ID, whereas concurrently deploying a TruffleHog binary to scan the native filesystem for embedded secrets and techniques.
Sha1-Hulud – The Second Coming (Supply – Socket.dev)
Not like typical scrapers, this payload aggressively enumerates cloud infrastructure, biking by each area in AWS, Google Cloud, and Azure to extract secrets and techniques from managed vaults.
All stolen knowledge is obscured utilizing three layers of Base64 encoding earlier than being exfiltrated to a randomly generated GitHub repository created inside the sufferer’s account.
Moreover, the malware makes an attempt privilege escalation on Linux runners by manipulating sudoers or executing Docker run –privileged instructions to achieve root entry.
If no legitimate credentials are discovered to propagate the worm, the malware executes a harmful wiper operate that deletes the information.
Comply with us on Google Information, LinkedIn, and X to Get Extra Prompt Updates, Set CSN as a Most well-liked Supply in Google.