Cybersecurity researchers have found two malicious Google Chrome extensions with the identical identify and printed by the identical developer that include capabilities to intercept site visitors and seize consumer credentials.
The extensions are marketed as a “multi-location community velocity check plug-in” for builders and overseas commerce personnel. Each the browser add-ons can be found for obtain as of writing. The small print of the extensions are as follows –
Phantom Shuttle (ID: fbfldogmkadejddihifklefknmikncaj) – 2,000 customers (Printed on November 26, 2017)
Phantom Shuttle (ID: ocpcmfmiidofonkbodpdhgddhlcmcofd) – 180 customers (Printed on April 27, 2023)
“Customers pay subscriptions starting from ¥9.9 to ¥95.9 CNY ($1.40 to $13.50 USD), believing they’re buying a reputable VPN service, however each variants carry out equivalent malicious operations,” Socket safety researcher Kush Pandya stated.
“Behind the subscription facade, the extensions execute full site visitors interception by means of authentication credential injection, function as man-in-the-middle proxies, and repeatedly exfiltrate consumer knowledge to the menace actor’s C2 [command-and-control] server.”
As soon as unsuspecting customers make the cost, they obtain VIP standing and the extensions auto-enable “smarty” proxy mode, which routes site visitors from over 170 focused domains by means of the C2 infrastructure.
The extensions work as marketed to strengthen the phantasm of a useful product. They carry out precise latency assessments on proxy servers and show connection standing, whereas preserving customers at nighttime about their primary purpose, which is to intercept community site visitors and steal credentials.
This includes malicious modifications prepended to 2 JavaScript libraries, particularly, jquery-1.12.2.min.js and scripts.js, that come bundled with the extensions. The code is designed to mechanically inject hard-coded proxy credentials (topfany / 963852wei) into each HTTP authentication problem throughout all web sites by registering a listener on chrome.webRequest.onAuthRequired.
“When any web site or service requests HTTP authentication (Primary Auth, Digest Auth, or proxy authentication), this listener fires earlier than the browser shows a credential immediate,” Pandya defined. “It instantly responds with the hardcoded proxy credentials, utterly clear to the consumer. The asyncBlocking mode ensures synchronous credential injection, stopping any consumer interplay.”
As soon as customers authenticate to a proxy server, the extension configures Chrome’s proxy settings utilizing a Proxy Auto-Configuration (PAC) script to implement three modes –
shut, which disables the proxy function
at all times, which routes all net site visitors by means of the proxy
smarty, which routes a hard-coded listing of greater than 170 high-value domains by means of the proxy
The listing of domains contains developer platforms (GitHub, Stack Overflow, Docker), cloud providers (Amazon Net Companies, Digital Ocean, Microsoft Azure), enterprise options (Cisco, IBM, VMware), social media (Fb, Instagram, Twitter), and grownup content material websites. The inclusion of pornographic websites is probably going an try and blackmail victims, Socket theorized.
The web results of this conduct is that consumer net site visitors is routed by means of menace actor-controlled proxies whereas the extension maintains a 60-second heartbeat to its C2 server at phantomshuttle[.]area, a website that is still operational. It additionally grants the attacker a “man-in-the-middle” (MitM) place to seize site visitors, manipulate responses, and inject arbitrary payloads.
Extra importantly, the heartbeat message transmits a VIP consumer’s e-mail, password in plaintext, and model quantity to an exterior server through an HTTP GET request each 5 minutes for steady credential exfiltration and session monitoring.
“The mixture of heartbeat exfiltration (credentials and metadata) plus proxy MitM (real-time site visitors seize) supplies complete knowledge theft capabilities working repeatedly whereas the extension stays energetic,” Socket stated.
Put in another way, the extension captures passwords, bank card numbers, authentication cookies, searching historical past, kind knowledge, API keys, and entry tokens from customers accessing the focused domains whereas VIP mode is energetic. What’s extra, the theft of developer secrets and techniques may pave the way in which for provide chain assaults.
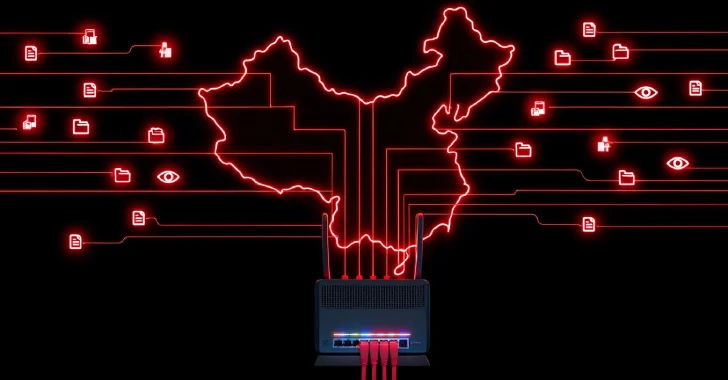
It is at the moment not recognized who’s behind the eight-year-old operation, however the usage of Chinese language language within the extension description, the presence of Alipay/WeChat Pay integration to make funds, and the usage of Alibaba Cloud to host the C2 area factors to a China-based operation.
“The subscription mannequin creates sufferer retention whereas producing income, and the skilled infrastructure with cost integration presents a facade of legitimacy,” Socket stated. “Customers imagine they’re buying a VPN service whereas unknowingly enabling full site visitors compromise.”
The findings spotlight how browser-based extensions have gotten an unmanaged threat layer for enterprises. Customers who’ve put in the extensions are suggested to take away them as quickly as attainable. For safety groups, it is important to deploy extension allowlisting, monitor for extensions with subscription cost programs mixed with proxy permissions, and implement community monitoring for suspicious proxy authentication makes an attempt.