Jan 07, 2026Ravie LakshmananNetwork Safety / Vulnerability
A newly found vital safety flaw in legacy D-Hyperlink DSL gateway routers has come beneath lively exploitation within the wild.
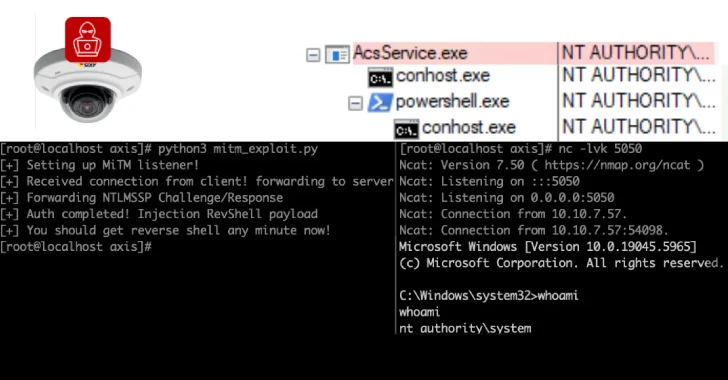
The vulnerability, tracked as CVE-2026-0625 (CVSS rating: 9.3), issues a case of command injection within the “dnscfg.cgi” endpoint that arises on account of improper sanitization of user-supplied DNS configuration parameters.
“An unauthenticated distant attacker can inject and execute arbitrary shell instructions, leading to distant code execution,” VulnCheck famous in an advisory.
“The affected endpoint can also be related to unauthenticated DNS modification (‘DNSChanger’) conduct documented by D-Hyperlink, which reported lively exploitation campaigns concentrating on firmware variants of the DSL-2740R, DSL-2640B, DSL-2780B, and DSL-526B fashions from 2016 by 2019.”
The cybersecurity firm additionally famous that exploitation makes an attempt concentrating on CVE-2026-0625 had been recorded by the Shadowserver Basis on November 27, 2025. A few of the impacted gadgets have reached end-of-life (EoL) standing as of early 2020 –
DSL-2640B <= 1.07
DSL-2740R < 1.17
DSL-2780B <= 1.01.14
DSL-526B <= 2.01
In an alert of its personal, D-Hyperlink initiated an inside investigation following a report from VulnCheck on December 16, 2025, about lively exploitation of “dnscfg.cgi,” and that it is working to establish historic and present use of the CGI library throughout all its product choices.
It additionally cited complexities in precisely figuring out affected fashions as a consequence of variations in firmware implementations and product generations. An up to date listing of particular fashions is anticipated to be printed later this week as soon as a firmware-level assessment is full.
“Present evaluation reveals no dependable mannequin quantity detection methodology past direct firmware inspection,” D-Hyperlink mentioned. “Because of this, D-Hyperlink is validating firmware builds throughout legacy and supported platforms as a part of the investigation.”
At this stage, the identification of the risk actors exploiting the flaw and the size of such efforts should not recognized. Provided that the vulnerability impacts DSL gateway merchandise which were phased out, it is essential for system house owners to retire them and improve to actively supported gadgets that obtain common firmware and safety updates.
“CVE-2026-0625 exposes the identical DNS configuration mechanism leveraged in previous large-scale DNS hijacking campaigns,” Subject Impact mentioned. “The vulnerability permits unauthenticated distant code execution by way of the dnscfg.cgi endpoint, giving attackers direct management over DNS settings with out credentials or consumer interplay.”
“As soon as altered, DNS entries can silently redirect, intercept, or block downstream site visitors, leading to a persistent compromise affecting each system behind the router. As a result of the impacted D-Hyperlink DSL fashions are finish of life and unpatchable, organizations that proceed to function them face elevated operational danger.”