Ravie LakshmananJan 20, 2026Vulnerability / Synthetic Intelligence
A set of three safety vulnerabilities has been disclosed in mcp-server-git, the official Git Mannequin Context Protocol (MCP) server maintained by Anthropic, that may very well be exploited to learn or delete arbitrary information and execute code below sure circumstances.
“These flaws could be exploited by immediate injection, that means an attacker who can affect what an AI assistant reads (a malicious README, a poisoned difficulty description, a compromised webpage) can weaponize these vulnerabilities with none direct entry to the sufferer’s system,” Cyata researcher Yarden Porat mentioned in a report shared with The Hacker Information.
Mcp-server-git is a Python bundle and an MCP server that gives a set of built-in instruments to learn, search, and manipulate Git repositories programmatically through giant language fashions (LLMs).
The safety points, which have been addressed in variations 2025.9.25 and 2025.12.18 following accountable disclosure in June 2025, are listed under –
CVE-2025-68143 (CVSS rating: 8.8 [v3] / 6.5 [v4]) – A path traversal vulnerability arising on account of the git_init instrument accepting arbitrary file system paths throughout repository creation with out validation (Mounted in model 2025.9.25)
CVE-2025-68144 (CVSS rating: 8.1 [v3] / 6.4 [v4]) – An argument injection vulnerability arising on account of git_diff and git_checkout features passing user-controlled arguments on to git CLI instructions with out sanitization (Mounted in model 2025.12.18)
CVE-2025-68145 (CVSS rating: 7.1 [v3] / 6.3 [v4]) – A path traversal vulnerability arising on account of a lacking path validation when utilizing the –repository flag to restrict operations to a selected repository path (Mounted in model 2025.12.18)
Profitable exploitation of the above vulnerabilities might permit an attacker to show any listing on the system right into a Git repository, overwrite any file with an empty diff, and entry any repository on the server.
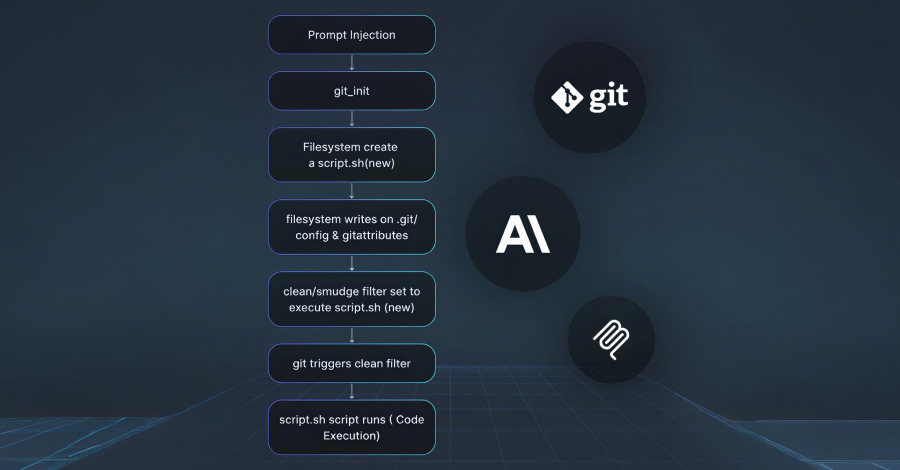
In an assault state of affairs documented by Cyata, the three vulnerabilities may very well be chained with the Filesystem MCP server to put in writing to a “.git/config” file (usually situated throughout the hidden .git listing) and obtain distant code execution by triggering a name to git_init by way of a immediate injection.
Use git_init to create a repo in a writable listing
Use the Filesystem MCP server to put in writing a malicious .git/config with a clear filter
Write a .gitattributes file to use the filter to sure information
Write a shell script with the payload
Write a file that triggers the filter
Name git_add, which executes the clear filter, operating the payload
In response to the findings, the git_init instrument has been faraway from the bundle and provides further validation to stop path traversal primitives. Customers of the Python bundle are advisable to replace to the most recent model for optimum safety.
“That is the canonical Git MCP server, the one builders are anticipated to repeat,” Shahar Tal, CEO and co-founder of Agentic AI safety firm Cyata, mentioned. “If safety boundaries break down even within the reference implementation, it is a sign that the whole MCP ecosystem wants deeper scrutiny. These aren’t edge circumstances or unique configurations, they work out of the field.”