Jun 30, 2025Ravie LakshmananCybercrime / Vulnerability
The menace actor often called Blind Eagle has been attributed with excessive confidence to using the Russian bulletproof internet hosting service Proton66.
Trustwave SpiderLabs, in a report revealed final week, stated it was in a position to make this connection by pivoting from Proton66-linked digital property, resulting in the invention of an lively menace cluster that leverages Visible Fundamental Script (VBS) information as its preliminary assault vector and installs off-the-shelf distant entry trojans (RATS).Many menace actors depend on bulletproWhile Visible Fundamental Script (VBS) might sound outdated, it is nonetheless aof internet hosting suppliers like Proton66 as a result of these companies deliberately ignore abuse studies and authorized takedown requests. This makes it simpler for attackers to run phishing websites, command-and-control servers, and malware supply methods with out interruption.
The cybersecurity firm stated it recognized a set of domains with the same naming sample (e.g., gfast.duckdns[.]org, njfast.duckdns[.]org) starting in August 2024, all of which resolved to the identical IP deal with (“45.135.232[.]38”) that is related to Proton66.The usage of dynamic DNS companies like DuckDNS additionally performs a key position in these operations. As a substitute of registering new domains every time, attackers rotate subdomains tied to a single IP deal with — making detection tougher for defenders.
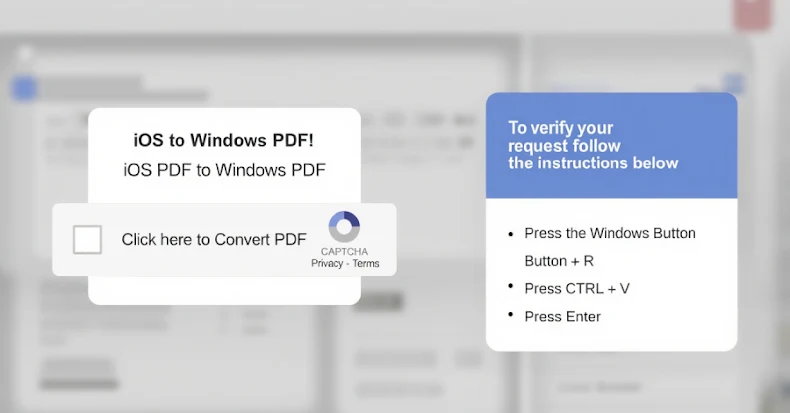
“The domains in query have been used to host a wide range of malicious content material, together with phishing pages and VBS scripts that function the preliminary stage of malware deployment,” safety researcher Serhii Melnyk stated. “These scripts act as loaders for second-stage instruments, which, on this marketing campaign, are restricted to publicly out there and sometimes open-source RATs.”Whereas VBS might sound outdated, it is nonetheless a go-to software for preliminary entry attributable to its compatibility with Home windows methods and skill to run silently within the background. Attackers use it to obtain malware loaders, bypass antivirus instruments, and mix into regular person exercise. These light-weight scripts are sometimes step one in multi-stage assaults, which later deploy RATs, information stealers, or keyloggers.
The phishing pages have been discovered to legit Colombian banks and monetary establishments, together with Bancolombia, BBVA, Banco Caja Social, and Davivienda. Blind Eagle, often known as AguilaCiega, APT-C-36, and APT-Q-98, is thought for its concentrating on of entities in South America, notably Colombia and Ecuador.
The misleading websites are engineered to reap person credentials and different delicate info. The VBS payloads hosted on the infrastructure come fitted with capabilities to retrieve encrypted executable information from a distant server, primarily performing as a loader for commodity RATS like AsyncRAT or Remcos RAT.
Moreover, an evaluation of the VBS codes has revealed overlaps with Vbs-Crypter, a software linked to a subscription-based crypter service known as Crypters and Instruments that is used to obfuscate and pack VBS payloads with an intention to keep away from detection.
Trustwave stated it additionally found a botnet panel that enables customers to “management contaminated machines, retrieve exfiltrated information, and work together with contaminated endpoints via a broad set of capabilities usually present in commodity RAT administration suites.”
The disclosure comes as Darktrace revealed particulars of a Blind Eagle marketing campaign that has been concentrating on Colombian organizations since November 2024 by exploiting a now-patched Home windows flaw (CVE-2024-43451) to obtain and execute the next-stage payload, a conduct that was first documented by Examine Level in March 2025.
“The persistence of Blind Eagle and skill to adapt its ways, even after patches have been launched, and the velocity at which the group have been in a position to proceed utilizing pre-established TTPs highlights that well timed vulnerability administration and patch software, whereas important, will not be a standalone protection,” the corporate stated.
Discovered this text attention-grabbing? Observe us on Twitter and LinkedIn to learn extra unique content material we submit.