The sudden emergence of the “TeamsPhantom” malware in early June rattled faculty districts and multinational companies alike.
Masquerading as a innocent Microsoft Groups plug-in, the menace weaponized professional assembly invites to sideload a multi-stage loader that siphoned Azure AD refresh tokens and session cookies.
Inside forty-eight hours, telemetry confirmed probing exercise on greater than 24,000 endpoints, whereas red-team simulations confirmed the malware’s means to pivot into SharePoint and OneDrive assets.
Regardless of a flurry of anomalous Graph API calls lighting up SOC dashboards, it was 13-year-old Dylan—already celebrated for a number of accountable disclosures—who correlated the site visitors to a beforehand unseen token-replay approach.
Microsoft analysts quickly famous the marketing campaign’s distinctive abuse of conversational webhooks to impersonate tenant directors, validating Dylan’s findings and triggering an emergency takedown window. The attacker’s chain from spear-phishing invite to privilege escalation.
Impression assessments reveal selective exfiltration of proprietary paperwork and Groups chat histories, intensifying considerations over intellectual-property leakage.
Victims reported phantom calendar entries and rogue channels, indicators that allowed blue groups to pivot hunts towards the plug-in’s hashed manifest.
Dylan’s after-action temporary warns that interface extensibility, when left unguarded, turns into a high-impact assault floor. Whereas these items maps the adversary’s replay loop in opposition to Microsoft’s Zero-Belief pillars.
By the week’s finish, Microsoft revoked 187 compromised code-signing certificates and tightened store-side validation.
But copy-cat variants already probe new obfuscation layers, illustrating how rapidly legal tooling evolves.
Dylan, now the youngest contributor to MSRC’s malware-response playbooks, has begun co-authoring detection logic that flags unsolicited add-on manifests—proof that recent eyes can upend entrenched threat-intel paradigms.
An infection Mechanism
In contrast to macro-laden Workplace droppers, TeamsPhantom embeds its bootstrapper inside a Base64-encoded appSettings block that the Groups shopper parses at start-up.
The blob expands into an obfuscated PowerShell loader operating in constrained-language mode, trimming AMSI visibility. As soon as memory-resident, the loader decrypts its C2 record by XOR-ing every byte with the tenant’s personal GUID—a sly trick that defeats static indicators.
A 38-line JavaScript module then hooks the onMessageReceived handler to reap authentication cookies in actual time.
$guid = (Get-AzureADTenantDetail).ObjectId
$appCfg = Get-Content material “$Env:APPDATAMicrosoftGroupsappSettings.json” | ConvertFrom-Json
$bytes = [Convert]::FromBase64String($appCfg.bootstrap)
$decoded = -join ($bytes | % { $_ -bxor ($guid.ToByteArray()[$_-1]) })
Invoke-Expression ([Text.Encoding]::UTF8.GetString($decoded))
Microsoft’s patch closes the manifest-validation hole, however defenders are urged to watch tenant-wide add-on registrations and hunt for GUID-based XOR loops in script blocks.
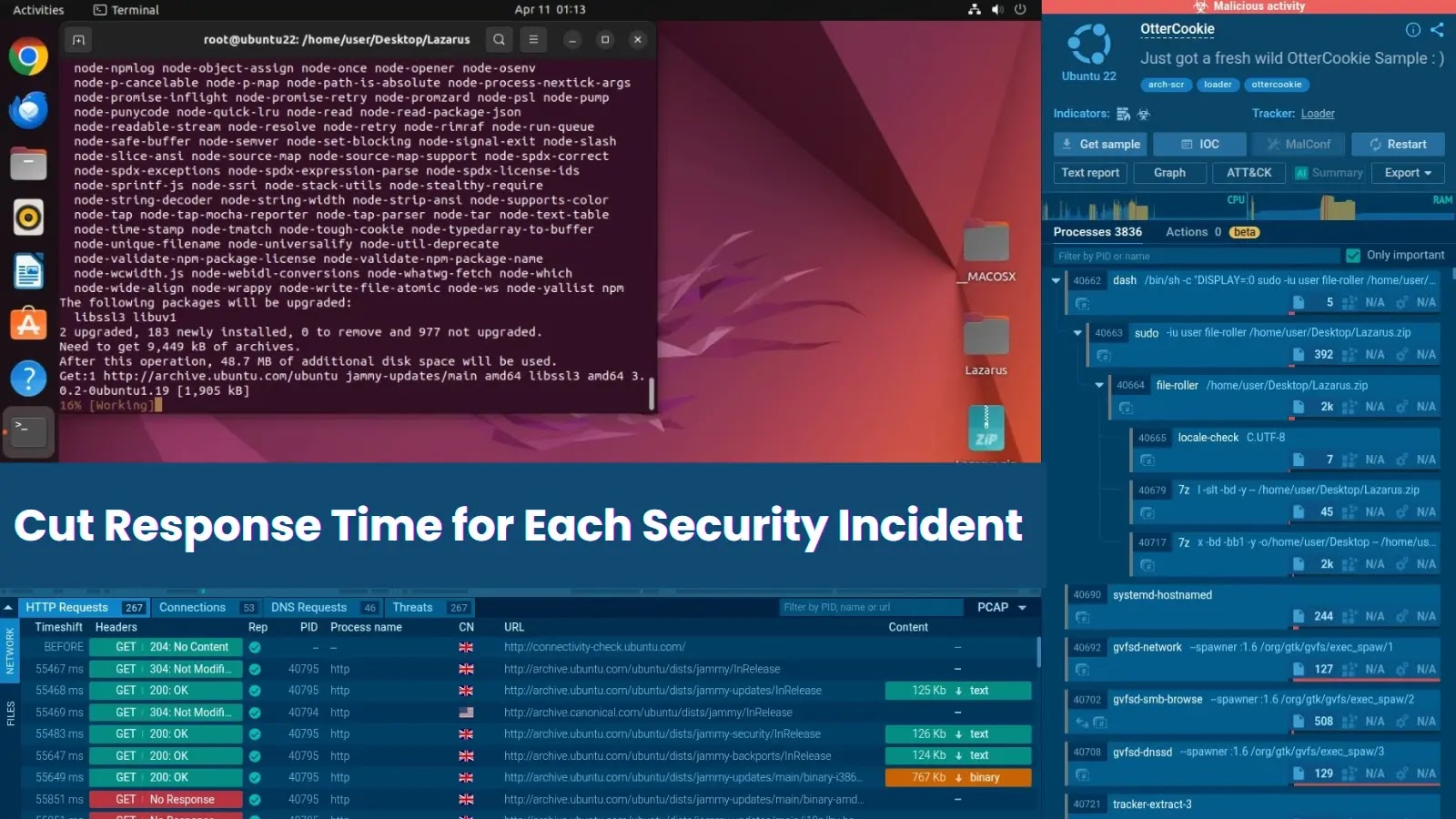
Examine reside malware conduct, hint each step of an assault, and make sooner, smarter safety selections -> Attempt ANY.RUN now