A crucial safety vulnerability in AWS Organizations has been found that might enable attackers to realize full management over total multi-account AWS environments by means of a mis-scoped managed coverage.
The flaw, recognized within the AmazonGuardDutyFullAccess managed coverage model 1, allows privilege escalation from a compromised member account to full organizational takeover, together with potential management of the administration account itself.
The vulnerability stems from an improperly scoped permission inside the AWS-managed coverage that grants the organizations:RegisterDelegatedAdministrator motion with unrestricted useful resource entry.
This oversight permits attackers who compromise a person or position within the administration account with the weak coverage connected to register any account inside the group as a delegated administrator for delicate providers, successfully bypassing meant safety boundaries.
The assault vector leverages AWS Organizations’ delegated administrator characteristic, which was designed to cut back reliance on extremely privileged administration accounts by permitting particular member accounts to manage providers organization-wide.
Nonetheless, the mis-scoped coverage transforms this safety characteristic into a robust escalation mechanism.
An attacker can chain delegation privileges with management over a member account to achieve administrative entry to crucial providers akin to AWS Identification and Entry Administration Identification Middle (previously SSO) or CloudFormation StackSets throughout all organizational accounts.
Cymulate researchers recognized this vulnerability throughout their investigation of AWS Organizations cross-account pivoting and compromise eventualities.
The analysis workforce, led by Ben Zamir, found that the coverage’s overly permissive construction might allow attackers to delegate delicate providers to accounts below their management, subsequently manipulating organization-wide identification administration or deploying malicious infrastructure throughout all the atmosphere.
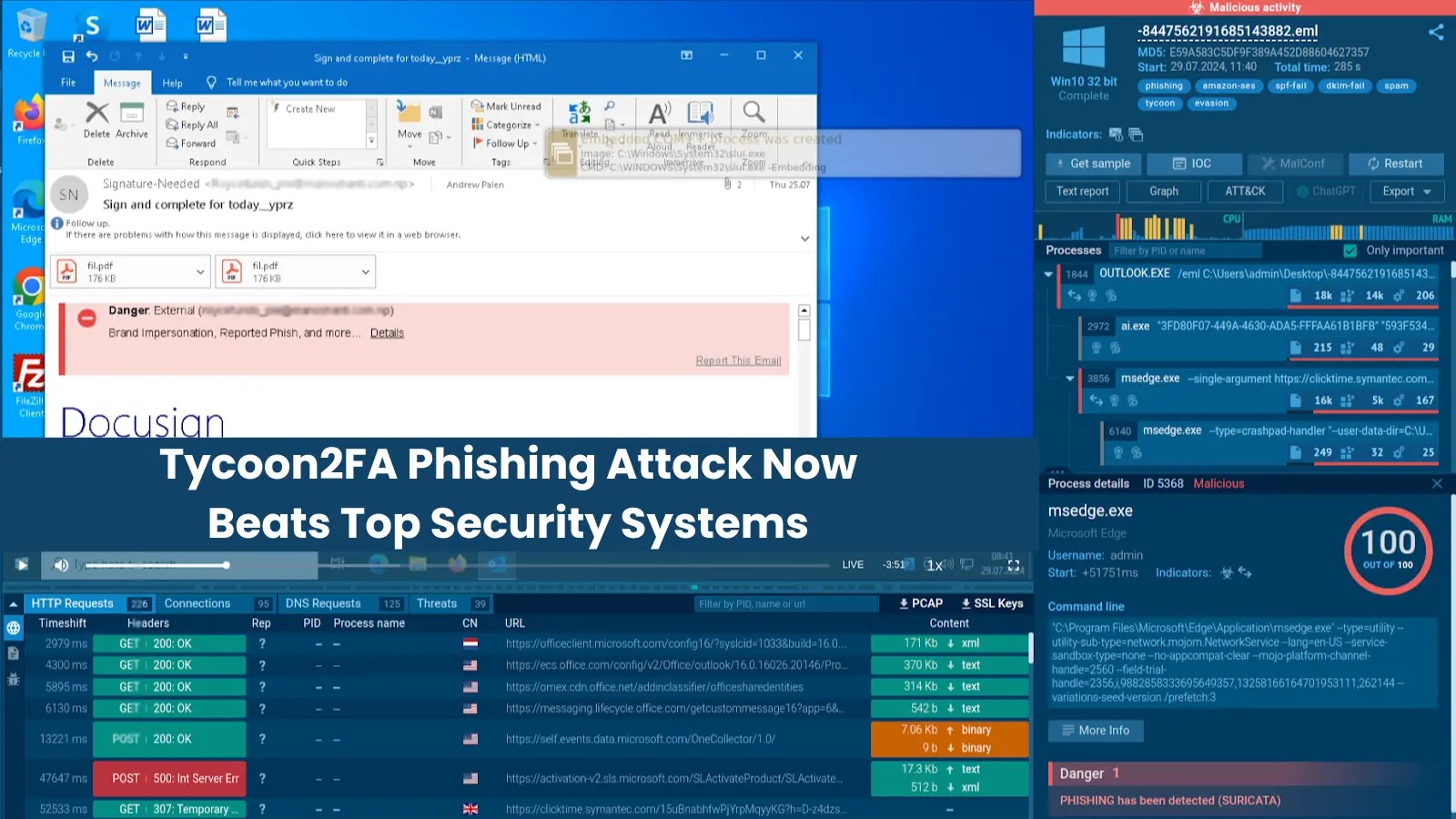
The technical exploitation course of includes a number of crucial steps that reveal the severity of this vulnerability.
As soon as an attacker compromises a administration account identification with the weak coverage, they’ll execute the next command to register a managed account as a delegated administrator:-
aws organizations register-delegated-administrator –account-id –service-principal
Persistence and Privilege Escalation Mechanism
Essentially the most regarding side of this vulnerability lies in its capability to determine persistent, organization-wide entry by means of authentic AWS options.
Persistence and Privilege Escalation (Supply – Cymulate)
When an attacker efficiently registers a compromised account as a delegated administrator for AWS Identification Middle, they acquire the power to control permission units, person teams, and entry configurations throughout all organizational accounts.
This functionality permits them so as to add malicious identities to high-privilege teams or reset passwords of customers with administrative entry to the administration account.
The persistence mechanism is especially insidious as a result of it operates by means of authentic delegation channels that will not set off conventional safety alerts.
Assault stream (Supply – Cymulate)
Attackers can modify current permission units or create new ones with elevated privileges, guaranteeing continued entry even when the preliminary compromise vector is found and remediated.
Moreover, the read-only organizational entry granted to delegated directors supplies full visibility into the atmosphere construction, enabling attackers to determine high-value targets and plan refined multi-account assaults.
AWS has responded to this discovery by releasing model 2 of the AmazonGuardDutyFullAccess managed coverage with stricter useful resource constraints that get rid of the escalation path.
Nonetheless, current roles and customers connected to model 1 stay weak till directors manually improve to the corrected coverage.
Organizations ought to instantly audit all principals utilizing the weak coverage and implement the up to date model to stop potential exploitation of this crucial safety flaw.
Examine reside malware conduct, hint each step of an assault, and make sooner, smarter safety choices -> Strive ANY.RUN now