Jul 18, 2025Ravie LakshmananCyber Espionage / Malware
A number of sectors in China, Hong Kong, and Pakistan have develop into the goal of a menace exercise cluster tracked as UNG0002 (aka Unknown Group 0002) as a part of a broader cyber espionage marketing campaign.
“This menace entity demonstrates a powerful choice for utilizing shortcut information (LNK), VBScript, and post-exploitation instruments corresponding to Cobalt Strike and Metasploit, whereas persistently deploying CV-themed decoy paperwork to lure victims,” Seqrite Labs researcher Subhajeet Singha stated in a report revealed this week.
The exercise encompasses two main campaigns, one referred to as Operation Cobalt Whisper which occurred between Could and September 2024, and Operation AmberMist that occurred between January and Could 2025.
Targets of those campaigns embody protection, electrotechnical engineering, vitality, civil aviation, academia, medical establishments, cybersecurity, gaming, and software program improvement sectors.
Operation Cobalt Whisper was first documented by Seqrite Labs in late October 2024, detailing using ZIP archives propagated by way of spear-phishing assaults to ship Cobalt Strike beacons, a post-exploitation framework, utilizing LNK and Visible Primary Scripts as interim payloads.
“The scope and complexity of the marketing campaign, coupled with the tailor-made lures, strongly counsel a focused effort by an APT group to compromise delicate analysis and mental property in these industries,” the corporate famous on the time.
The AmberMist assault chains have been discovered to leverage spear-phishing emails as a place to begin to ship LNK information masquerading as curriculum vitae and resumes to unleash a multi-stage an infection course of that ends in the deployment of INET RAT and Blister DLL loader.
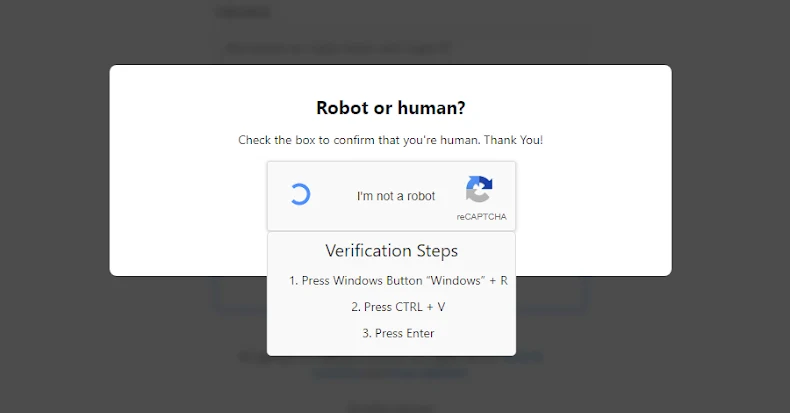
Alternate assault sequences detected in January 2025 have been discovered to redirect e mail recipients to faux touchdown pages spoofing Pakistan’s Ministry of Maritime Affairs (MoMA) web site to serve faux CAPTCHA verification checks that make use of ClickFix techniques to launch PowerShell instructions, that are used to execute Shadow RAT.
Shadow RAT, launched by way of DLL side-loading, is able to establishing contact with a distant server to await additional instructions. INET RAT is assessed to be a modified model of Shadow RAT, whereas the Blister DLL implant features as a shellcode loader, ultimately paving the way in which for a reverse-shell primarily based implant.
The precise origins of the menace actor stay unclear, however proof factors to it being an espionage-focused group from Southeast Asia.
“UNG0002 represents a classy and protracted menace entity from South Asia that has maintained constant operations focusing on a number of Asian jurisdictions since at the very least Could 2024,” Singha stated. “The group demonstrates excessive adaptability and technical proficiency, constantly evolving their toolset whereas sustaining constant techniques, methods, and procedures.”