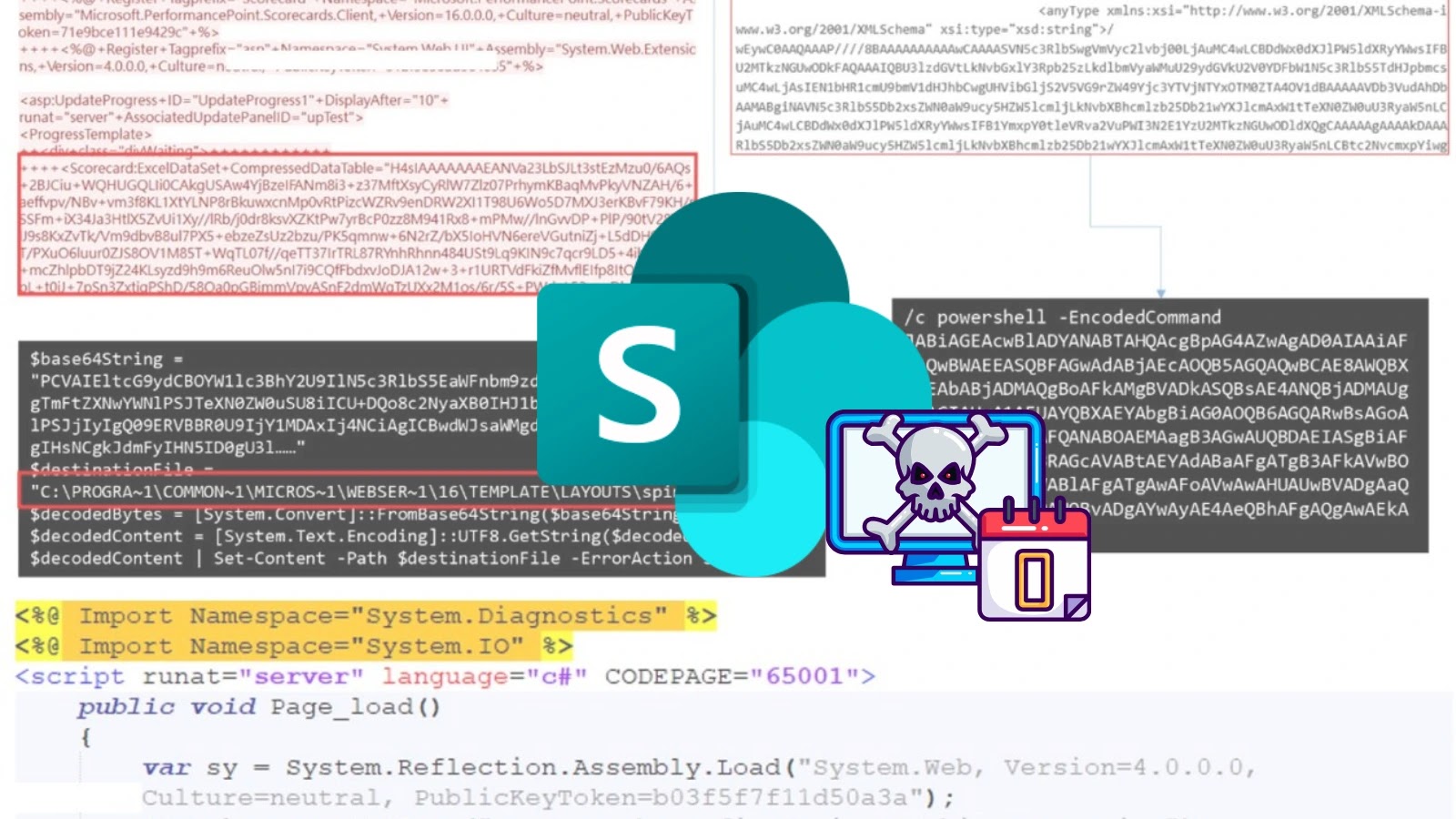
A important new menace focusing on Microsoft SharePoint servers via a complicated exploit chain dubbed “ToolShell.”
This multi-stage assault combines beforehand patched vulnerabilities with recent zero-day exploits to attain full system compromise, affecting SharePoint Enterprise Server 2016, SharePoint Server 2019, and SharePoint Server Subscription Version.
Key Takeaways1. ToolShell exploits 4 SharePoint CVEs (two patched, two zero-days) for full system control2. Deploys superior internet shells for distant command execution and cryptographic key theft3. Patch instantly and implement detection methods to dam lively assaults
Vulnerability Chain Targets SharePoint Infrastructure
The ToolShell marketing campaign leverages a harmful mixture of 4 CVEs to ascertain distant code execution capabilities.
Risk actors are exploiting two beforehand patched vulnerabilities (CVE-2025-49704 and CVE-2025-49706) alongside two newly found zero-day variants (CVE-2025-53770 and CVE-2025-53771).
The Cybersecurity and Infrastructure Safety Company (CISA) has already added these CVEs to its Recognized Exploited Vulnerabilities catalog, highlighting the severity of this menace.
Preliminary reconnaissance includes attackers utilizing easy CURL and PowerShell instructions to probe goal methods and extract system info.
The assault usually begins with the exploitation of the “spinstall0.aspx” endpoint, permitting attackers to add configuration knowledge to distant servers.
This probing part allows menace actors to fingerprint goal environments earlier than deploying extra subtle payloads.
The marketing campaign deploys two main malicious parts: GhostWebShell and KeySiphon. GhostWebShell represents a extremely subtle ASP.NET internet shell designed for persistent distant entry.
It embeds a Base64-encoded ASP.NET web page that exposes a “?cmd=” parameter, enabling attackers to execute arbitrary system instructions via “cmd.exe /c ” syntax.
The online shell employs superior evasion strategies, quickly manipulating inner BuildManager flags utilizing reflection to bypass precompilation checks.
It registers a customized VirtualPathProvider for fileless operation, injecting malicious pages from reminiscence beneath reliable SharePoint paths resembling “/_layouts/15/ghostfile.aspx.”
After command execution, the shell restores authentic BuildManager flags to attenuate detection footprints.
KeySiphon serves as a reconnaissance instrument that captures complete system intelligence. It collects important info together with logical drive configurations, machine specs, CPU core counts, system uptime, and working system particulars.
Accumulating system info
Most regarding, KeySiphon extracts utility validation and decryption keys via the “System.Internet” namespace, particularly invoking “MachineKeySection.GetApplicationConfig()” to reveal cryptographic secrets and techniques that allow authentication token forgery and ViewState manipulation.
Organizations ought to instantly apply accessible patches and implement layered detection methods combining community monitoring, endpoint safety, and complete log evaluation.
Given the fast weaponization of those vulnerabilities, safety groups should prioritize SharePoint infrastructure hardening and take into account implementing extra entry controls to mitigate potential compromise makes an attempt.
IOCs
IP157[.]245[.]126[.]186159[.]203[.]88[.]182146[.]190[.]224[.]250203[.]160[.]80[.]77203[.]160[.]86[.]111205[.]198[.]84[.]197159[.]89[.]10[.]213165[.]232[.]162[.]99185[.]169[.]0[.]111146[.]70[.]41[.]178165[.]154[.]196[.]91
File10e01ce96889c7b4366cfa1e7d99759e4e2b6e5dfe378087d9e836b7278abfb67e3fff35ef909c556bdf6d9a63f0403718bf09fecf4e03037238176e86cf4e980548fad567c22ccf19031671f7ec1f53b735abf93dc11245bc9ea4dfd463fe403adbebbc2093615bb9210bfdb8ebb0841c62426bee8820f86ff0a64d15206041
Expertise quicker, extra correct phishing detection and enhanced safety for your small business with real-time sandbox analysis-> Strive ANY.RUN now