Aug 18, 2025Ravie LakshmananMalware / Enterprise Safety
The risk actors behind the Noodlophile malware are leveraging spear-phishing emails and up to date supply mechanisms to deploy the knowledge stealer in assaults aimed toward enterprises situated within the U.S., Europe, Baltic international locations, and the Asia-Pacific (APAC) area.
“The Noodlophile marketing campaign, lively for over a 12 months, now leverages superior spear-phishing emails posing as copyright infringement notices, tailor-made with reconnaissance-derived particulars like particular Fb Web page IDs and firm possession info,” Morphisec researcher Shmuel Uzan stated in a report shared with The Hacker Information.
Noodlophile was beforehand detailed by the cybersecurity vendor in Might 2025, uncovering the attackers’ use of pretend synthetic intelligence (AI)-powered instruments as lures to propagate the malware. These counterfeit packages have been discovered to be marketed on social media platforms like Fb.
That stated, the adoption of copyright infringement lures isn’t a brand new improvement. Again in November 2024, Examine Level uncovered a large-scale phishing operation that focused people and organizations beneath the false premise of copyright infringement violations to drop the Rhadamanthys Stealer.
However the newest iteration of the Noodlophile assaults reveals notable deviation, significantly relating to using reputable software program vulnerabilities, obfuscated staging through Telegram, and dynamic payload execution.
All of it begins with a phishing electronic mail that seeks to trick workers into downloading and working malicious payloads by inducing a false sense of urgency, claiming copyright violations on particular Fb Pages. The messages originate from Gmail accounts in an effort to evade suspicion.
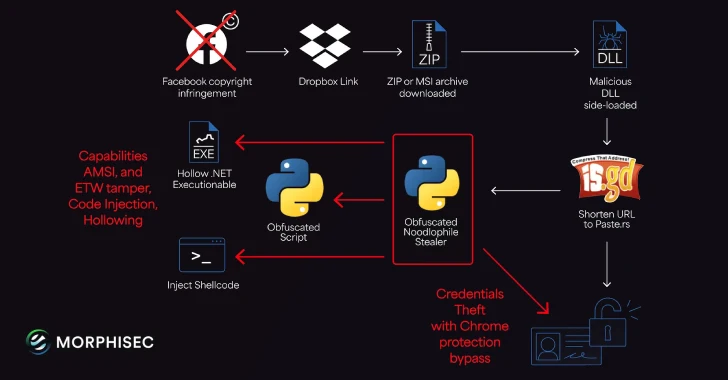
Current inside the message is a Dropbox hyperlink that drops a ZIP or MSI installer, which, in flip, sideloads a malicious DLL utilizing reputable binaries related to Haihaisoft PDF Reader to finally launch the obfuscated Noodlophile stealer, however not earlier than working batch scripts to determine persistence utilizing Home windows Registry.
What’s notable in regards to the assault chain is that it leverages Telegram group descriptions as a useless drop resolver to fetch the precise server (“paste[.]rs”) that hosts the stealer payload to problem detection and takedown efforts.
“This method builds on the earlier marketing campaign’s methods (e.g., Base64-encoded archives, LOLBin abuse like certutil.exe), however provides layers of evasion via Telegram-based command-and-control and in-memory execution to keep away from disk-based detection,” Uzan stated.
Noodlophile is a full-fledged stealer that may seize knowledge from net browsers and collect system info. Evaluation of the stealer supply code signifies ongoing improvement efforts to increase on its capabilities to facilitate screenshot seize, keylogging, file exfiltration, course of monitoring, community info gathering, file encryption, and browser historical past extraction.
“The intensive focusing on of browser knowledge underscores the marketing campaign’s give attention to enterprises with vital social media footprints, significantly on platforms like Fb,” Morphisec stated. “These unimplemented features point out that the stealer’s builders are actively working to increase its capabilities, probably remodeling it right into a extra versatile and harmful risk.”