Sep 12, 2025Ravie LakshmananVulnerability / Cyber Espionage
The U.S. Cybersecurity and Infrastructure Safety Company (CISA) on Thursday added a essential safety flaw impacting Dassault Systèmes DELMIA Apriso Manufacturing Operations Administration (MOM) software program to its Identified Exploited Vulnerabilities (KEV) catalog, based mostly on proof of energetic exploitation.
The vulnerability, tracked as CVE-2025-5086, carries a CVSS rating of 9.0 out of 10.0. In response to Dassault, the problem impacts variations from Launch 2020 by means of Launch 2025.
“Dassault Systèmes DELMIA Apriso comprises a deserialization of untrusted information vulnerability that would result in a distant code execution,” the company mentioned in an advisory.
The addition of CVE-2025-5086 to the KEV catalog comes after the SANS Web Storm Middle reported seeing exploitation makes an attempt focusing on the flaw that originate from the IP handle 156.244.33[.]162, which geolocates to Mexico.
The assaults contain sending an HTTP request to the “/apriso/WebServices/FlexNetOperationsService.svc/Invoke” endpoint with a Base64-encoded payload that decodes to a GZIP-compressed Home windows executable (“fwitxz01.dll”), Johannes B. Ullrich, the dean of analysis on the SANS Know-how Institute, mentioned.
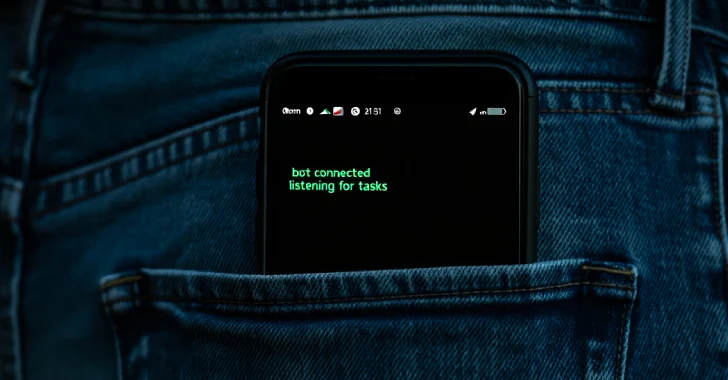
Kaspersky has flagged the DLL as “Trojan.MSIL.Zapchast.gen,” which the corporate describes as a bug designed to electronically spy on a consumer’s actions, together with capturing keyboard enter, taking screenshots, and gathering a listing of energetic purposes, amongst others.
“The collected data is distributed to the cybercriminal by varied means, together with electronic mail, FTP, and HTTP (by sending information in a request),” the Russian cybersecurity vendor added.
Zapchast variants, in line with Bitdefender and Pattern Micro, have been distributed through phishing emails bearing malicious attachments for over a decade. It is presently not clear if “Trojan.MSIL.Zapchast.gen” is an improved model of the identical malware.
In mild of energetic exploitation, Federal Civilian Government Department (FCEB) businesses are suggested to use the required updates by October 2, 2025, to safe their networks.