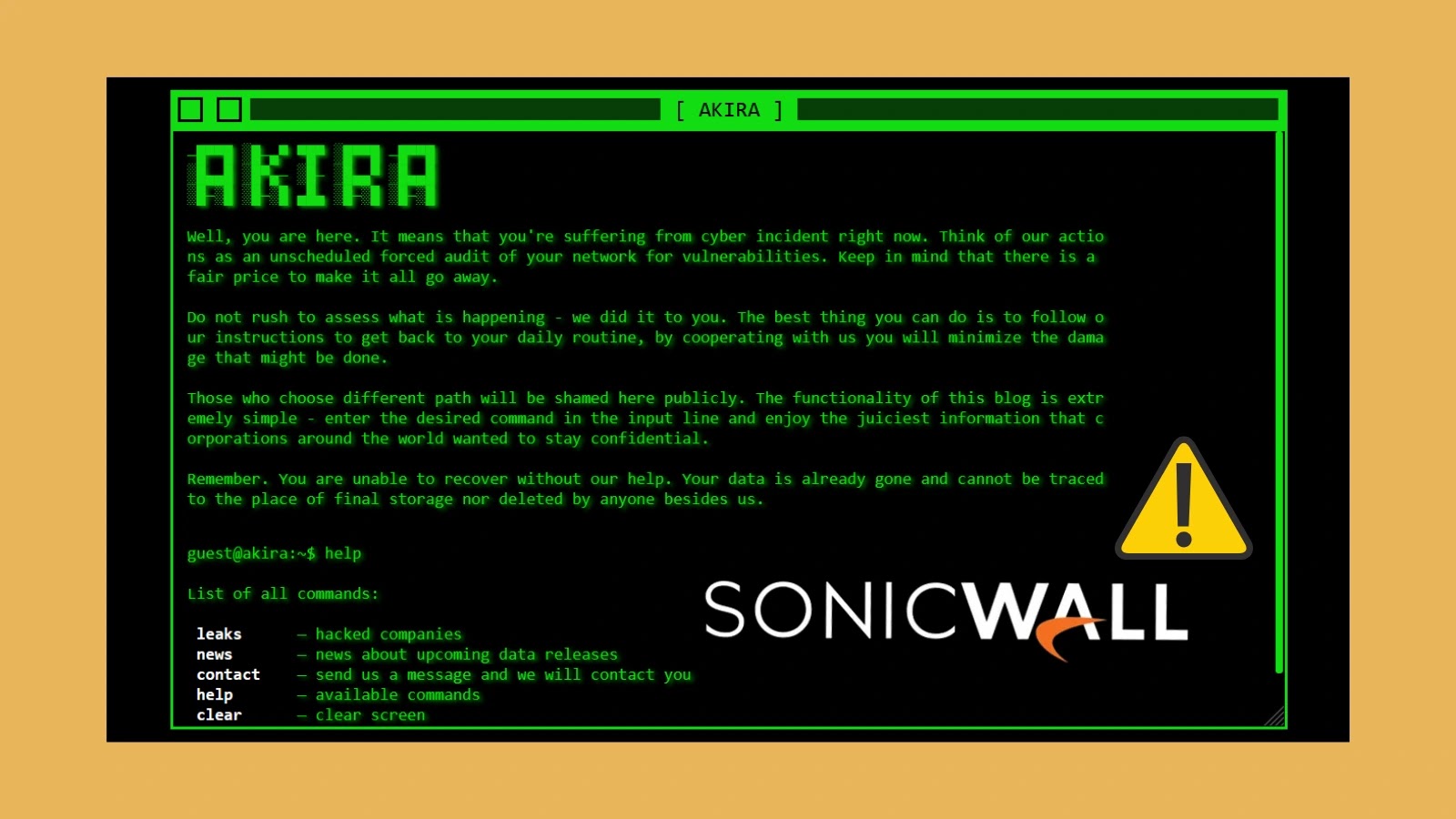
A classy evasion method employed by Akira ransomware associates, exploiting authentic Home windows drivers to bypass antivirus and endpoint detection and response (EDR) programs throughout latest SonicWall VPN assault campaigns.
The assaults, which have escalated from late July by early August 2025, exhibit the menace actors’ evolving techniques to keep up persistence and keep away from detection in compromised environments.
Key Takeaways1. Akira makes use of authentic Home windows drivers to bypass safety controls.2. Exploits undisclosed SonicWall VPN vulnerability for preliminary entry.3. Disable SSLVPN, allow MFA, hunt for malicious driver hashes.
Akira Ransomware Leverages Home windows Drivers
In keeping with GuidePoint Safety studies, Akira ransomware operators are leveraging two particular Home windows drivers in what safety consultants classify as a Carry Your Personal Weak Driver (BYOVD) assault methodology.
The primary driver, rwdrv.sys (SHA256: 16f83f056177c4ec24c7e99d01ca9d9d6713bd0497eeedb777a3ffefa99c97f0), is a authentic part of ThrottleStop, a Home windows efficiency tuning utility designed for Intel CPUs.
Menace actors register this driver as a service to achieve kernel-level entry to compromised programs.
The second driver, hlpdrv.sys (SHA256: bd1f381e5a3db22e88776b7873d4d2835e9a1ec620571d2b1da0c58f81c84a56), serves a extra malicious goal by immediately focusing on Home windows Defender.
When executed, it modifies the DisableAntiSpyware registry settings inside REGISTRYMACHINESOFTWAREPoliciesMicrosoftWindows DefenderDisableAntiSpyware by regedit.exe execution.
Each drivers are usually deployed to the trail Customers$$REDACTED]AppDataLocalTemp and registered as providers named “mgdsrv” and “KMHLPSVC” respectively.
SonicWall VPN Concentrating on
The motive force-based evasion methods have been noticed constantly throughout a number of Akira ransomware incident response circumstances related to SonicWall VPN exploitation.
Whereas the precise vulnerability stays undisclosed, SonicWall has acknowledged the menace and issued emergency suggestions, together with disabling SSLVPN providers the place sensible, implementing multi-factor authentication (MFA), and enabling Botnet safety with Geo-IP filtering.
Safety groups can detect these threats utilizing YARA guidelines that determine the malicious hlpdrv.sys driver based mostly on PE file construction, particular imports from ntoskrnl.exe together with ZwSetSecurityObject and PsLookupProcessByProcessId, and artifact strings corresponding to “SystemKMHLPDRV” and “HlpDrv”.
Organizations ought to prioritize trying to find these indicators whereas implementing SonicWall’s really helpful hardening measures to forestall preliminary entry.
Indicators Of Compromise (IOCs)
Equip your SOC with full entry to the most recent menace information from ANY.RUN TI Lookup that may Enhance incident response -> Get 14-day Free Trial