BlindEagle, a South American risk group, has launched a classy marketing campaign in opposition to Colombian authorities companies, demonstrating an alarming evolution in assault strategies.
In early September 2025, the group focused a authorities company underneath the Ministry of Commerce, Trade and Tourism (MCIT) utilizing coordinated phishing emails and multi-stage malware supply.
This assault represents a major escalation within the complexity and class of BlindEagle’s operations, shifting past primary malware deployment to a fastidiously orchestrated chain involving a number of malicious parts.
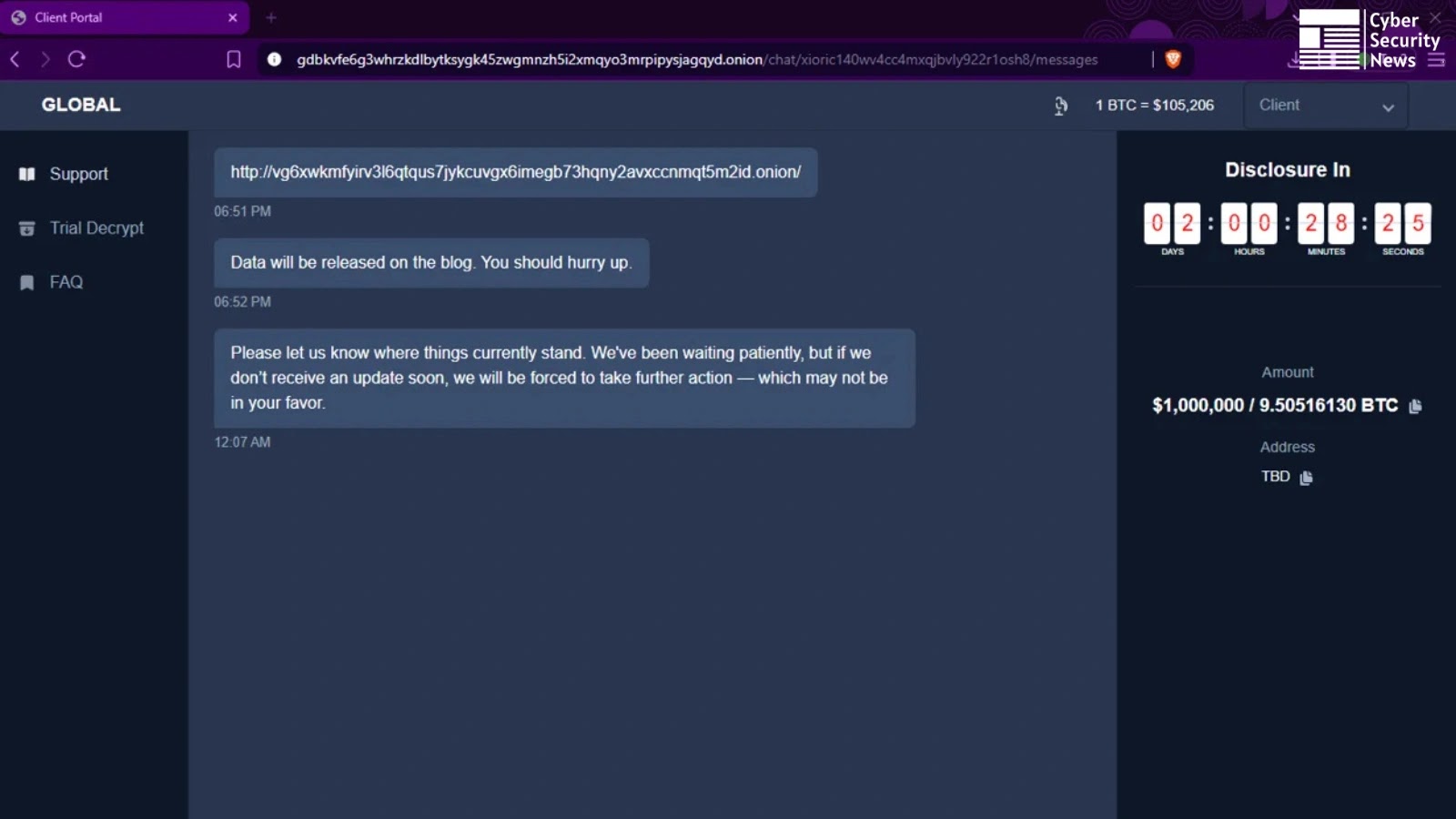
The assault begins with a strategically crafted phishing e-mail impersonating the Colombian judicial system.
The e-mail makes use of authorized terminology and official authorities formatting to create a way of urgency, pressuring recipients to verify receipt of what seems to be a labor lawsuit notification.
Remarkably, the phishing e-mail was despatched from a compromised account inside the identical group, lending credibility to the message and bypassing typical e-mail safety measures.
This inner compromise allowed the attackers to use belief relationships and keep away from detection by safety protocols that sometimes flag exterior threats.
Zscaler analysts recognized the whole assault chain and decided that BlindEagle employed an unusually advanced file-less methodology to evade detection programs.
The SVG attachment included in BlindEagle’s phishing e-mail (Supply – Zscaler)
The preliminary attachment is an SVG (Scalable Vector Graphics) picture containing encoded HTML that directs customers to a fraudulent net portal mimicking the legit Colombian judicial department.
As soon as a person interacts with this portal, the assault chain unfolds by three JavaScript recordsdata and a PowerShell command, every stage progressively deobfuscating the subsequent element by numerous encoding strategies, together with Base64 and customized obfuscation algorithms.
An infection mechanism
The an infection mechanism demonstrates specific sophistication by the usage of steganography and legit companies for payload supply.
JavaScript recordsdata within the assault chain use intricate deobfuscation routines the place integer arrays are transformed to executable code.
The PowerShell command downloads a picture file from the Web Archive, extracts a Base64-encoded malicious payload hidden inside it, and hundreds the payload immediately into reminiscence utilizing .NET reflection.
Fraudulent net portal introduced to the person throughout BlindEagle’s assault (Supply – Zscaler)
This in-memory execution prevents any malicious file from touching the disk, considerably complicating detection efforts for conventional file-based safety options.
The PowerShell script executes Caminho, a downloader malware with Portuguese language artifacts in its code, which then retrieves DCRAT by Discord’s content material supply community.
DCRAT consists of superior evasion capabilities, notably patching Microsoft’s Antimalware Scan Interface (AMSI) to disable detection mechanisms.
Decoded BlindEagle PowerShell command (Supply – Zscaler)
The malware establishes persistence by scheduled duties and registry modifications, offering attackers sustained entry to compromised programs.
This marketing campaign showcases BlindEagle’s maturation as a risk actor, combining social engineering experience with technical proficiency in obfuscation, steganography, and legit service abuse to conduct focused assaults in opposition to authorities infrastructure with minimal detection danger.
Observe us on Google Information, LinkedIn, and X to Get Extra Instantaneous Updates, Set CSN as a Most popular Supply in Google.