A complicated backdoor malware often known as Backdoor.WIN32.Buterat has emerged as a big menace to enterprise networks, demonstrating superior persistence methods and stealth capabilities that allow attackers to take care of long-term unauthorized entry to compromised methods.
The malware has been recognized focusing on authorities and company environments by way of rigorously orchestrated phishing campaigns, malicious e-mail attachments, and trojanized software program downloads.
Not like typical malware centered on fast harm or information extraction, Buterat prioritizes longevity and covert operations.
The backdoor establishes encrypted communication channels with distant command-and-control servers, permitting menace actors to execute arbitrary instructions, deploy extra payloads, and transfer laterally throughout community infrastructure whereas evading conventional detection mechanisms.
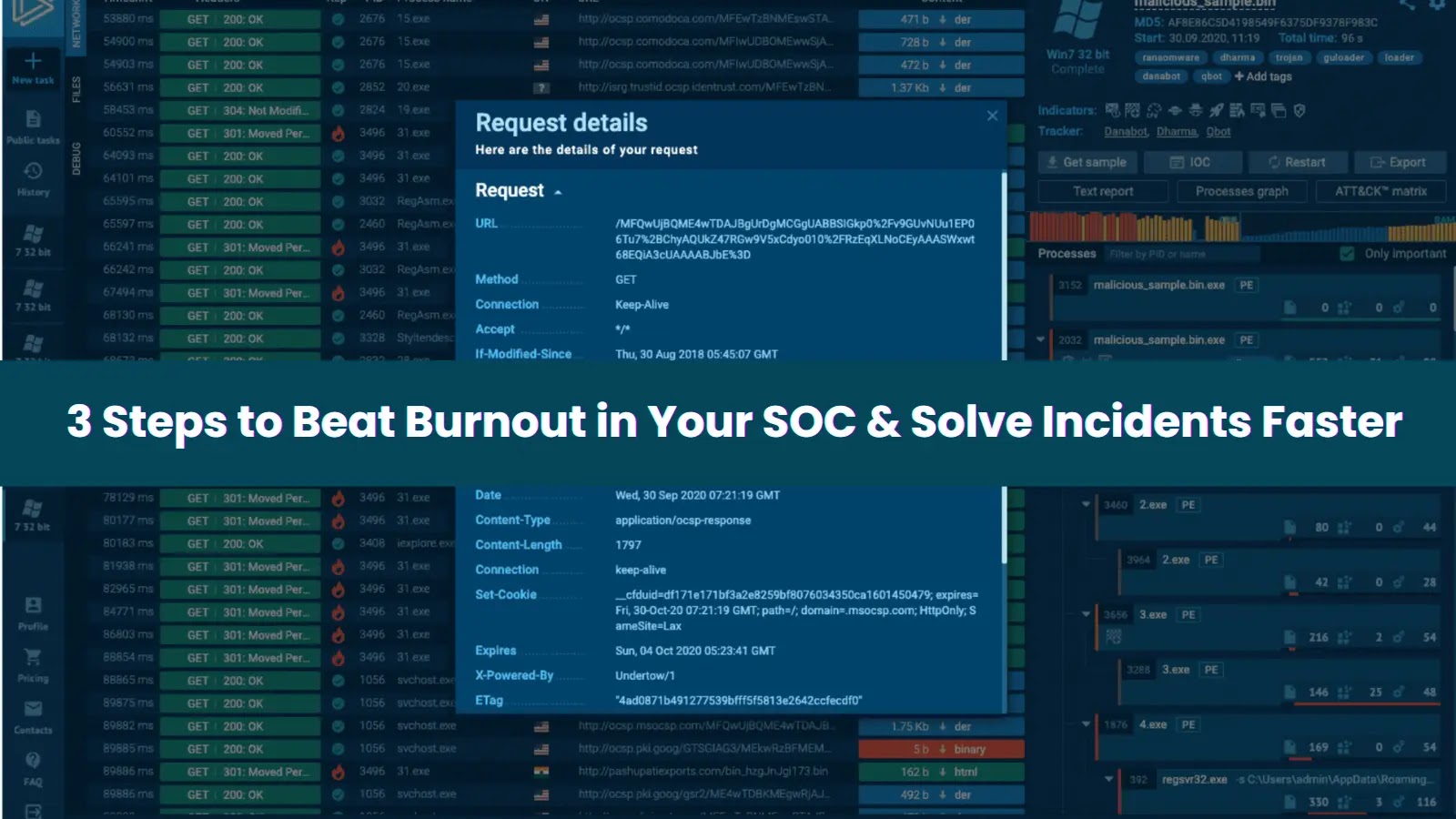
Level Wild researchers recognized the malware pattern with SHA-256 hash f50ec4cf0d0472a3e40ff8b9d713fb0995e648ecedf15082a88b6e6f1789cdab, revealing its compilation utilizing Borland Delphi and complicated obfuscation methods.
Execution Stream (Supply – Level Wild)
The malware disguises its processes below legit system duties and modifies registry keys to attain persistence throughout system reboots.
Superior Thread Manipulation and Injection Methods
Buterat employs subtle thread manipulation strategies that set it other than typical backdoor implementations.
The malware leverages obfuscated API calls, notably SetThreadContext and ResumeThread, to attain exact management over thread execution with out creating new processes or altering entry factors.
This method permits the backdoor to hijack present threads seamlessly, making detection considerably more difficult for behavioral evaluation methods.
The SetThreadContext API gives attackers with granular management over thread states, permitting them to inject malicious code into legit processes with out triggering course of creation alerts.
Following thread context modification, the malware makes use of ResumeThread to activate compromised threads with altered execution flows.
This method represents a complicated evasion mechanism that bypasses light-weight behavioral detection methods generally deployed in enterprise environments.
Throughout an infection, Buterat drops a number of executable information together with amhost.exe, bmhost.exe, cmhost.exe, dmhost.exe, and lqL1gG.exe within the consumer listing, establishing a number of persistence factors.
The malware makes an attempt communication with its command-and-control server at enabling distant management capabilities for information exfiltration and extra payload deployment.
Safety groups ought to monitor for these particular indicators of compromise and implement network-level blocking to stop communication with recognized malicious infrastructure.
Enhance your SOC and assist your workforce shield your corporation with free top-notch menace intelligence: Request TI Lookup Premium Trial.