A classy new ransomware-as-a-service operation has emerged with superior AI-powered negotiation capabilities and cell administration options, concentrating on organizations throughout healthcare, automotive, and industrial sectors.
GLOBAL GROUP, operated by risk actor “$$$”, has claimed 17 victims throughout a number of nations since its June 2025 launch, demonstrating speedy operational scaling by means of automated techniques and strategic partnerships with Preliminary Entry Brokers.
Key Takeaways1. GLOBAL GROUP launched in June 2025 as a rebranded Black Lock RaaS operation, claiming 17 victims throughout the US, UK, Australia, and Brazil.2. AI-powered negotiation system automates sufferer communications and permits non-English talking associates to demand seven-figure ransoms.3. Partnerships with Preliminary Entry Brokers and brute-force instruments concentrating on VPN/Outlook techniques speed up deployment whereas bypassing EDR detection.4. Cellular-friendly affiliate panel helps cross-platform ransomware builds with an 85% revenue-sharing mannequin to draw new operatives.
AI-Powered Negotiation System
GLOBAL GROUP first appeared on June 2, 2025, when risk actor “$$$” promoted the operation on the Ramp4u cybercriminal discussion board.
The group’s devoted leak website, accessible through Tor tackle vg6xwkmfyirv3l6qtqus7jykcuvgx6imegb73hqny2avxccnmqt5m2id[.]onion, initially listed 9 victims inside 5 days of launch.
GLOBAL GROUP DLS hosted on the Tor community
By July 14, 2025, the operation had expanded to 17 confirmed victims spanning the USA, the UK, Australia, and Brazil.
EclecticIQ analysts assess with medium confidence that GLOBAL GROUP represents a rebranding of the Black Lock RaaS operation.
Technical proof helps this connection, together with shared infrastructure hosted by Russian VPS supplier IpServer at IP tackle 193.19.119[.]4.
An operational safety failure uncovered this infrastructure when the group’s API endpoint /posts leaked JSON metadata containing the true internet hosting setting particulars.
Malware evaluation reveals that GLOBAL GROUP makes use of a custom-made variant of the earlier Mamona ransomware, sharing the equivalent mutex key GlobalFxo16jmdgujs437.
The present variant, compiled in Golang, employs ChaCha20-Poly1305 encryption and helps cross-platform deployment throughout Home windows, Linux, and macOS environments.
GLOBAL GROUP’s most distinctive function is its AI-driven negotiation panel, designed to help non-English-speaking associates in sufferer communications.
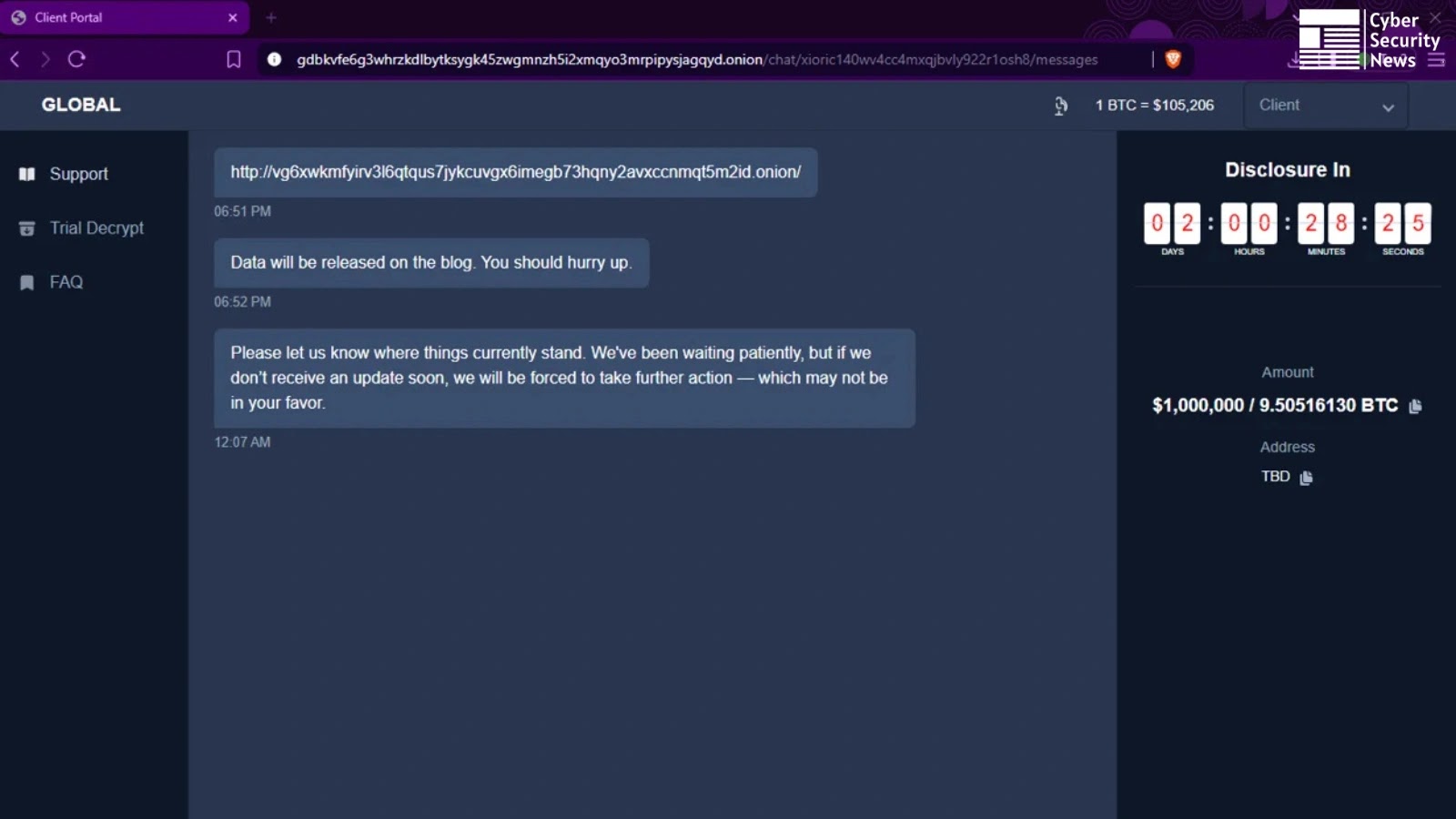
Negotiation panel, risk actor calls for 1 million US {dollars}
This automated system will increase psychological strain throughout ransom negotiations and facilitates seven-figure fee calls for. Latest negotiations have proven calls for reaching $1 million USD (roughly 9.5 BTC).
The operation presents an 85% revenue-sharing mannequin to draw associates, positioning itself competitively towards different RaaS operators.
A promotional video on the leak website showcases a complete affiliate panel supporting cell gadget administration, permitting operatives to conduct negotiations through smartphones.
The platform helps customized ransomware builds for ESXi, NAS, BSD, and Home windows techniques whereas claiming to be “undetectable by EDR”.
GLOBAL GROUP accelerates operations by means of partnerships with Preliminary Entry Brokers (IABs), buying pre-compromised community entry somewhat than conducting preliminary infiltration.
Risk actor “$$$” has acquired RDP entry to U.S. legislation companies and webshell entry to Linux-based SAP NetWeaver techniques. The operation notably targets edge community home equipment, together with Fortinet, Palo Alto, and Cisco VPN gadgets.
The group additionally makes use of brute-force instruments concentrating on Microsoft Outlook Net Entry and RDWeb portals, enabling speedy deployment whereas bypassing conventional endpoint detection techniques.
This technique permits associates to deal with payload supply and extortion somewhat than community penetration, considerably lowering time-to-compromise.
Examine dwell malware conduct, hint each step of an assault, and make sooner, smarter safety choices -> Attempt ANY.RUN now