A financially motivated menace group dubbed Grasping Sponge has been systematically concentrating on Mexican monetary establishments and organizations since 2021 with a closely modified model of the AllaKore distant entry trojan (RAT).
The marketing campaign represents a classy evolution of cybercriminal ways, combining conventional social engineering with superior technical capabilities designed particularly for monetary fraud operations.
The menace actors deploy their malware by means of spear-phishing campaigns and drive-by downloads, using trojanized Microsoft installer (MSI) information that masquerade as legit software program updates.
These malicious packages include a .NET downloader element that retrieves the custom-made AllaKore payload from command-and-control servers hosted on Hostwinds infrastructure in Dallas, Texas.
Earlier and present execution chains (Supply – Arctic Wolf)
The attackers have demonstrated specific crafty of their geographic concentrating on, implementing server-side geofencing mechanisms that limit payload supply solely to methods positioned inside Mexico.
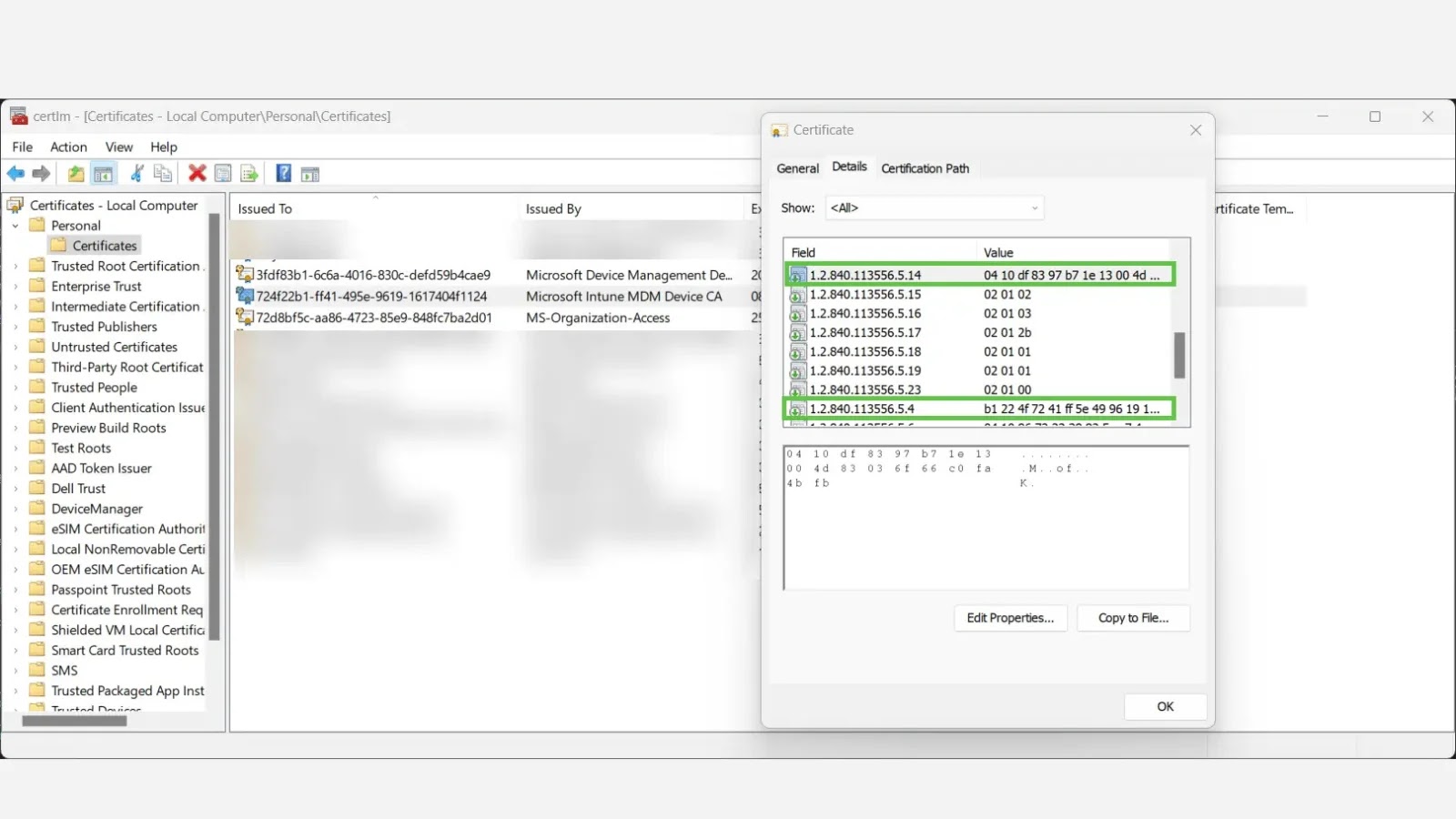
Arctic Wolf Labs researchers recognized vital enhancements to the menace group’s operational capabilities, noting the mixing of SystemBC as a secondary an infection vector.
This multi-platform malware proxy device allows the attackers to ascertain persistent backdoor entry and deploy extra malicious payloads as wanted.
The researchers noticed that latest campaigns have moved away from client-side geographic filtering to server-side restrictions, making detection and evaluation significantly more difficult for safety groups.
Superior Persistence and Evasion Mechanisms
The modified AllaKore variant employs subtle persistence methods that display the group’s technical maturity.
Disassembly of AllaKore’s replace and persistence mechanism (Supply – Arctic Wolf)
Upon profitable an infection, the malware establishes persistence by putting an up to date model of itself within the system’s Startup folder, retrieved from the URI endpoint /z1.txt.
The persistence mechanism is coupled with a complete cleanup operation utilizing PowerShell scripts that get rid of traces of the preliminary an infection vector from the %APPDATA% listing.
The malware’s evasion capabilities embody a Person Account Management (UAC) bypass method using Microsoft’s Connection Supervisor Profile Installer (CMSTP.exe).
This legit Home windows binary is exploited to proxy execution of malicious code whereas showing as a routine system replace course of labeled “Actualizando” (Spanish for “updating”).
The .NET downloader element makes use of a particular user-agent string Mozilla/4.0 (appropriate; MSIE 6.0; Home windows NT 5.2; .NET CLR 1.0.3705;) for command-and-control communications, using base64 encoding to obfuscate community site visitors patterns.
Increase detection, cut back alert fatigue, speed up response; all with an interactive sandbox constructed for safety groups -> Strive ANY.RUN Now