Chinese language-affiliated risk actor UNC6384 has been actively leveraging a essential Home windows shortcut vulnerability to focus on European diplomatic entities throughout Hungary, Belgium, Serbia, Italy, and the Netherlands.
Arctic Wolf researchers recognized this refined cyber espionage marketing campaign working all through September and October 2025, representing a major evolution within the group’s operational capabilities and geographic attain.
The assault begins with fastidiously crafted spearphishing emails containing URLs that ship malicious LNK information disguised as professional diplomatic convention agendas.
These information reference genuine European Fee conferences, NATO protection procurement workshops, and multilateral coordination occasions.
When customers click on these seemingly harmless shortcuts, a essential flaw in Home windows shortcut dealing with permits silent command execution that the majority detection methods fail to catch.
UNC6384 quickly adopted the ZDI-CAN-25373 vulnerability inside simply six months of its March 2025 public disclosure, demonstrating distinctive operational agility and vulnerability monitoring capabilities.
Execution chain (Supply – Arctic Wolf)
Arctic Wolf analysts detected the malware after the second paragraph of analysis, noting the subtle an infection mechanism that builds a posh multi-stage assault chain designed to evade conventional safety defenses.
Technical An infection Mechanism and Payload Supply
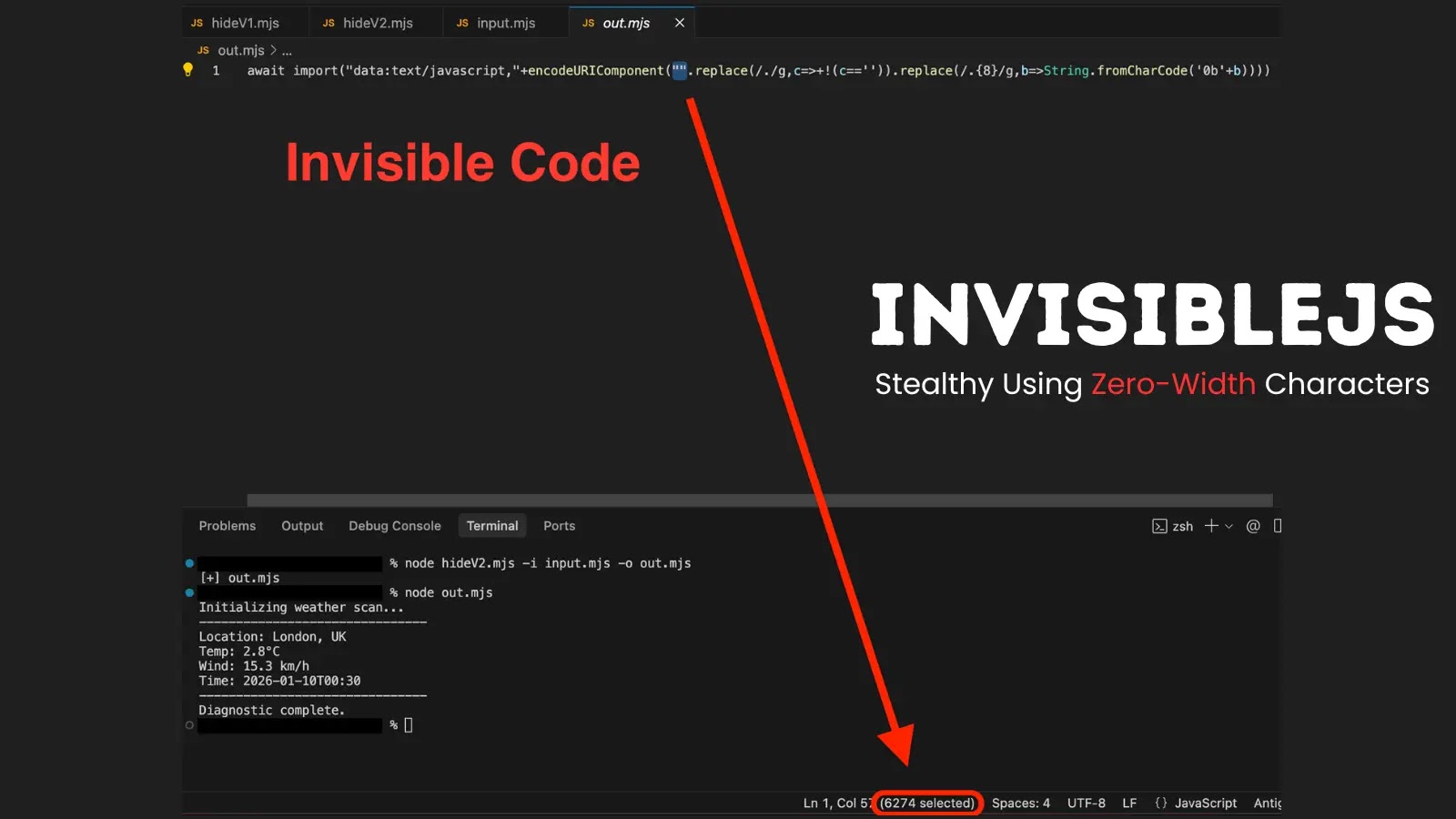
The exploitation mechanism cleverly abuses whitespace padding throughout the LNK file’s COMMAND_LINE_ARGUMENTS construction to cover malicious instructions from person visibility.
Upon execution, the compromised shortcut silently invokes PowerShell to extract and decompress a tar archive containing three essential parts: a professional, digitally signed Canon printer utility, a malicious DLL loader, and an encrypted PlugX distant entry trojan payload.
The assault chain employs DLL side-loading, exploiting normal Home windows library search order processes. When the Canon executable launches, it instinctively searches for supporting libraries in its native listing earlier than checking system folders.
The malicious DLL positioned there transparently masses, then decrypts the PlugX payload utilizing a hardcoded RC4 key and injects it straight into the professional course of’s reminiscence area, creating a virtually undetectable persistent backdoor.
The PlugX malware establishes encrypted HTTPS command and management connections utilizing randomized parameters throughout a number of redundant domains together with racineupci[.]org and dorareco[.]internet.
The malware creates hidden persistence directories with spoofed names like “SamsungDriver” and modifies Home windows registry Run keys, making certain continued entry throughout system restarts.
This marketing campaign demonstrates nation-state stage sophistication, combining zero-day exploitation data with meticulous social engineering concentrating on particular diplomatic personnel and occasions, representing a considerable intelligence assortment risk to European authorities operations.
Comply with us on Google Information, LinkedIn, and X to Get Extra Instantaneous Updates, Set CSN as a Most well-liked Supply in Google.