A classy new Android malware household dubbed “Albiriox” has emerged on the cybercrime panorama, providing superior distant entry capabilities as a Malware-as-a-Service (MaaS).
Recognized by researchers at Cleafy, the malware is designed to execute On-Machine Fraud (ODF) by granting attackers full management over contaminated units, permitting them to bypass safety measures and drain monetary accounts.
Albiriox first appeared in September 2025 inside unique underground boards, transitioning from a non-public beta section to a public business providing by October.
The operation is believed to be managed by Russian-speaking risk actors who’ve aggressively marketed the software. The service was launched with a subscription mannequin, charging associates roughly $650 per thirty days to entry the malware’s complete toolkit.
Not like easy credential stealers, Albiriox is engineered for real-time interplay. It leverages a VNC (Digital Community Computing) module that streams the sufferer’s display on to the attacker.
This enables criminals to carry out banking fraud manually on the sufferer’s gadget, typically whereas the consumer is unaware, successfully circumventing gadget fingerprinting and two-factor authentication (2FA) protocols.
Two-Stage An infection Chain
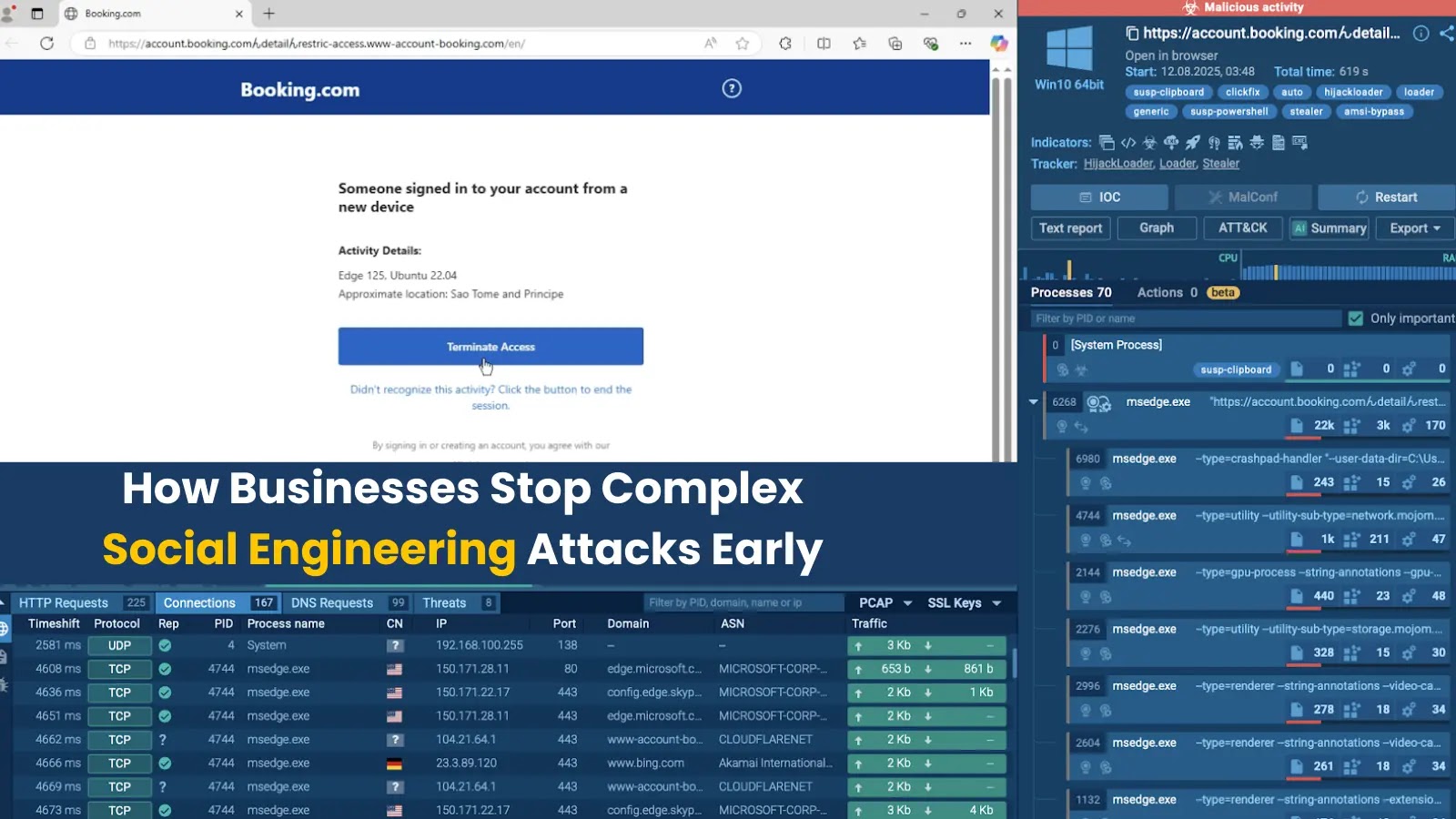
The distribution of Albiriox depends on a misleading two-stage course of designed to evade detection. Early campaigns focused customers in Austria utilizing a fraudulent model of the favored “Penny Market” utility. The an infection chain usually follows these steps:
Social Engineering: Victims obtain SMS messages with shortened hyperlinks promising reductions or prizes, redirecting them to a pretend Google Play Retailer web page.
Dropper Set up: The consumer downloads a dropper utility (e.g., the pretend Penny app).
Payload Supply: As soon as put in, the dropper requests “Set up Unknown Apps” permissions and fetches the precise Albiriox payload from a command-and-control (C2) server.
Latest iterations have advanced to incorporate WhatsApp-based lures, requiring customers to enter telephone numbers to obtain obtain hyperlinks, additional filtering targets to particular areas like Austria.
Albiriox’s structure focuses on stealth and management. It makes use of “Golden Crypt,” a third-party crypting service, to render the malware Absolutely Undetectable (FUD) by static antivirus engines. As soon as lively, it employs Accessibility Companies to execute overlay assaults and keylogging.
The malware comes hardcoded with a goal record of over 400 purposes. This intensive record consists of main conventional banking apps, cryptocurrency wallets, and cost processors worldwide, Cleafy added.
The next desk outlines the technical profile of the Albiriox operations noticed throughout the evaluation.
FeatureDetailsMalware TypeAndroid Banking Trojan / Distant Entry Trojan (RAT)Distribution ModelMalware-as-a-Service (MaaS)Main TacticsOn-Machine Fraud (ODF), Overlay Assaults, VNC StreamingTarget Scope400+ Monetary & Crypto ApplicationsEvasion Method“Golden Crypt” obfuscation, JSONPacker, Two-stage dropperCommand & ControlUnencrypted TCP Socket with JSON-based instructions
Albiriox’s fast improvement cycle suggests it’s positioning itself as a dominant software for monetary fraud. Its potential to mix display streaming with accessibility manipulation permits risk actors to function invisibly behind black-screen overlays, making it a crucial risk to monetary establishments and Android customers worldwide.
IOCs
Indicator TypeValuePort / NotesC2 Server IP194.32.79.945555 (Linked to samplef5b501e3…)Supply Domaingoogle-app-download[.]downloadPhishing / Dropper DeliveryDelivery Domaingoogle-get[.]downloadPhishing / Dropper DeliveryDelivery Domaingoogle-aplication[.]downloadPhishing / Dropper DeliveryDelivery Domainplay.google-get[.]storePhishing / Dropper DeliveryDelivery Domaingoogle-app-get[.]comPhishing / Dropper DeliveryDelivery Domaingoogle-get-app[.]comPhishing / Dropper DeliveryDelivery Domaingoogle-app-install[.]comPhishing / Dropper Supply
Comply with us on Google Information, LinkedIn, and X for day by day cybersecurity updates. Contact us to characteristic your tales.