A newly found zero-day vulnerability in Elastic’s Endpoint Detection and Response (EDR) answer permits attackers to bypass safety measures, execute malicious code, and set off a BSOD system crash, in response to the Ashes Cybersecurity analysis.
The vulnerability resides in a core part of the safety software program, successfully turning the defensive device right into a weapon in opposition to the methods it’s meant to guard.
The essential flaw was discovered within the “elastic-endpoint-driver.sys,” a kernel driver signed by Microsoft and developed by Elasticsearch, Inc. This driver is a basic a part of the Elastic Defend and Elastic Agent safety options.
The researcher who found the vulnerability has detailed a four-step assault chain that exploits this flaw to realize an entire system compromise.
The assault begins with an EDR Bypass, the place an attacker can use a {custom} loader to avoid Elastic’s safety protections. As soon as the EDR is blinded, the attacker can proceed to Distant Code Execution (RCE), operating malicious code on the system with out being detected or blocked.
The third step entails establishing Persistence by planting a {custom} kernel driver that may work together with the susceptible Elastic driver. Lastly, the attacker can set off a Privileged Persistent Denial of Service, inflicting the system to crash repeatedly and rendering it unusable.
Elastic EDR 0-Day Vulnerability
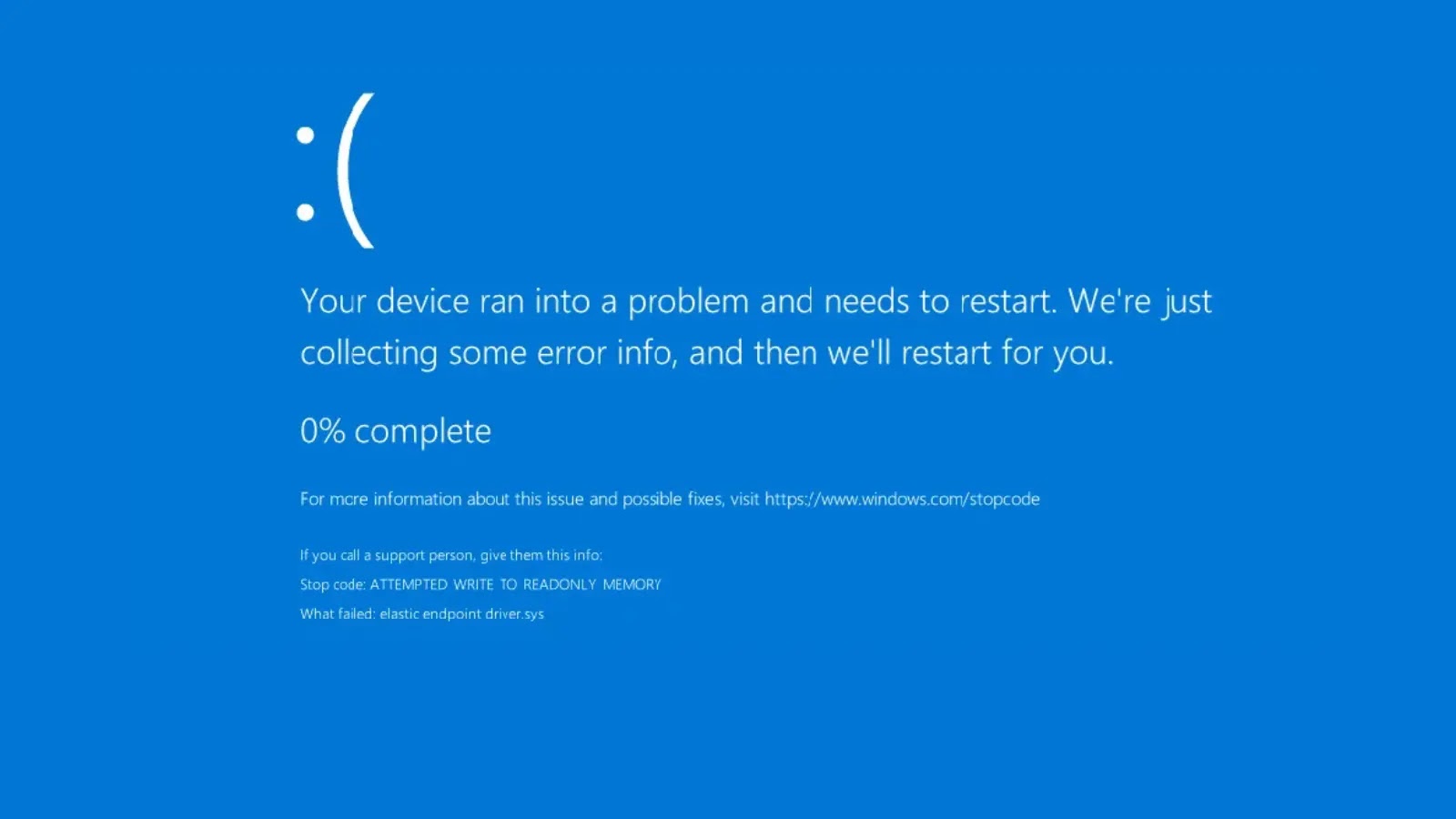
On the coronary heart of the vulnerability is a CWE-476: NULL Pointer Dereference. In response to the Ashes Cybersecurity analysis, the “elastic-endpoint-driver.sys” driver improperly handles reminiscence operations inside its privileged kernel routines.
Below sure situations, a pointer controllable from user-mode is handed right into a kernel operate with out correct validation. If this pointer is null, has been freed, or is corrupted, the kernel makes an attempt to dereference it, resulting in a system-wide crash, generally referred to as the Blue Display of Demise (BSOD).
The researcher demonstrated that this vulnerability isn’t just a theoretical bug however a dependable and reproducible exploit. A custom-built Proof of Idea, consisting of a C-based loader and a {custom} driver, was used to set off the flaw below managed situations.
This proof-of-concept first bypasses the EDR, hundreds the {custom} driver, establishes persistence so the motive force reloads on reboot, after which interacts with the susceptible Elastic driver to trigger the BSOD.
This successfully proves that the Elastic driver itself could be manipulated to exhibit malware-like conduct.
The implications of this zero-day are extreme for enterprises counting on Elastic’s safety merchandise. Each group utilizing Elastic’s SIEM and EDR options might doubtlessly be harboring a vulnerability that may be remotely exploited to disable their endpoints at scale.
This example creates a big threat, as a trusted, signed kernel driver could be become a persistent, privileged weapon.
The invention timeline for this vulnerability started on June 2nd, 2025. Disclosure makes an attempt had been made by HackerOne on June eleventh and the Zero Day Initiative (ZDI) on July twenty ninth. Following these makes an attempt, an unbiased disclosure was made on August sixteenth, 2025.
The affected product is elastic-endpoint-driver.sys in model 8.17.6, although all subsequent variations are believed to be susceptible, as no patch has been launched.
The researcher famous that the vulnerability was found throughout user-mode testing operations and that their group, Ashes Cybersecurity Pvt Ltd., is a paying buyer of Elastic. “A defender that crashes, blinds or disables its personal system on command is indistinguishable from malware,” the researcher said, highlighting the erosion of belief this causes not solely in Elastic however within the broader safety business. Till a patch is issued, clients stay uncovered to this energetic zero-day risk.
Enhance your SOC and assist your crew defend your enterprise with free top-notch risk intelligence: Request TI Lookup Premium Trial.