A classy phishing marketing campaign concentrating on organizations has emerged, exploiting the trusted fame of Veeam Software program via weaponized WAV audio recordsdata delivered through e mail.
The assault represents an evolution in social engineering techniques, combining conventional phishing strategies with audio-based deception to bypass typical safety measures and person consciousness coaching.
The malicious marketing campaign begins with seemingly official voicemail notifications that mimic normal VoIP system alerts when calls are missed.
Attackers craft emails containing WAV file attachments that, when opened, play recordings of people impersonating Veeam Software program representatives.
The audio message particularly references expired backup licenses, creating urgency round vital enterprise infrastructure to immediate rapid motion from recipients.
Web Storm Middle researchers recognized this marketing campaign after receiving studies from safety professionals who encountered the suspicious emails.
The assault demonstrates specific sophistication in its use of audio social engineering, as voice-based deception can usually bypass visible cues that usually alert customers to phishing makes an attempt.
The recorded message states: “Hello, that is xxxx from Veeam Software program. I’m calling you right this moment relating to your backup license which has expired this month. Would you please give me a name to debate about it?”
Audio-Primarily based Social Engineering Mechanism
The weaponized WAV recordsdata function the first assault vector, leveraging psychological manipulation via auditory channels.
Not like conventional text-based phishing, this method exploits customers’ tendency to belief voice communications, notably once they seem to originate from official software program distributors.
The attackers display broad-spectrum concentrating on, as recipients included people with no connection to Veeam environments, indicating a mass distribution technique reasonably than exact reconnaissance-based concentrating on.
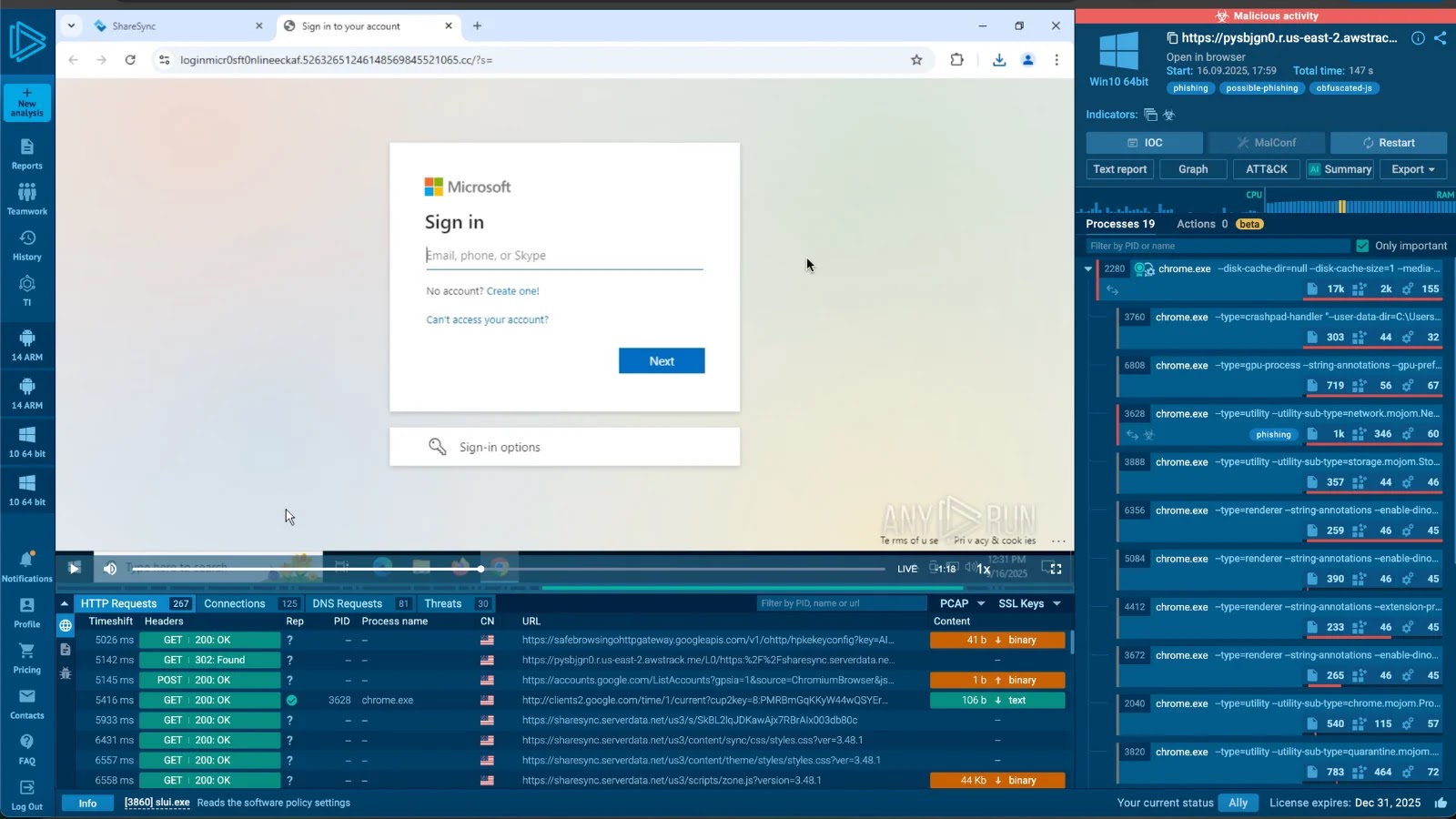
Increase detection, scale back alert fatigue, speed up response; all with an interactive sandbox constructed for safety groups -> Strive ANY.RUN Now