Since its emergence in February 2025, the NightSpire ransomware group has quickly distinguished itself by way of a classy double-extortion technique that mixes focused encryption with public knowledge leaks.
Initially surfacing in South Korea, the group leveraged vulnerabilities in company networks to realize preliminary entry, typically exploiting outdated VPN home equipment and unpatched Distant Desktop Protocol providers.
As soon as inside, NightSpire deploys custom-made payloads that scan linked file shares and databases, making certain most affect by prioritizing high-value property.
The group’s emblematic brand, emblazoned on its Devoted Leak Website, underscores its professionalized method to cyber extortion.
NightSpire Staff brand (Supply – ASEC)
Inside weeks of its first public disclosure, NightSpire orchestrated assaults in opposition to organizations throughout North America, Asia, and Europe, hitting sectors corresponding to retail and wholesale in america, chemical manufacturing in Japan, and maritime logistics in Thailand.
Victims report encrypted extensions renamed to “.nspire,” accompanied by a ransom observe named readme.txt in every compromised listing.
ASEC analysts famous that these notes make use of extremely threatening language and embody countdown timers for knowledge launch, heightening stress on victims to barter earlier than delicate info is made public.
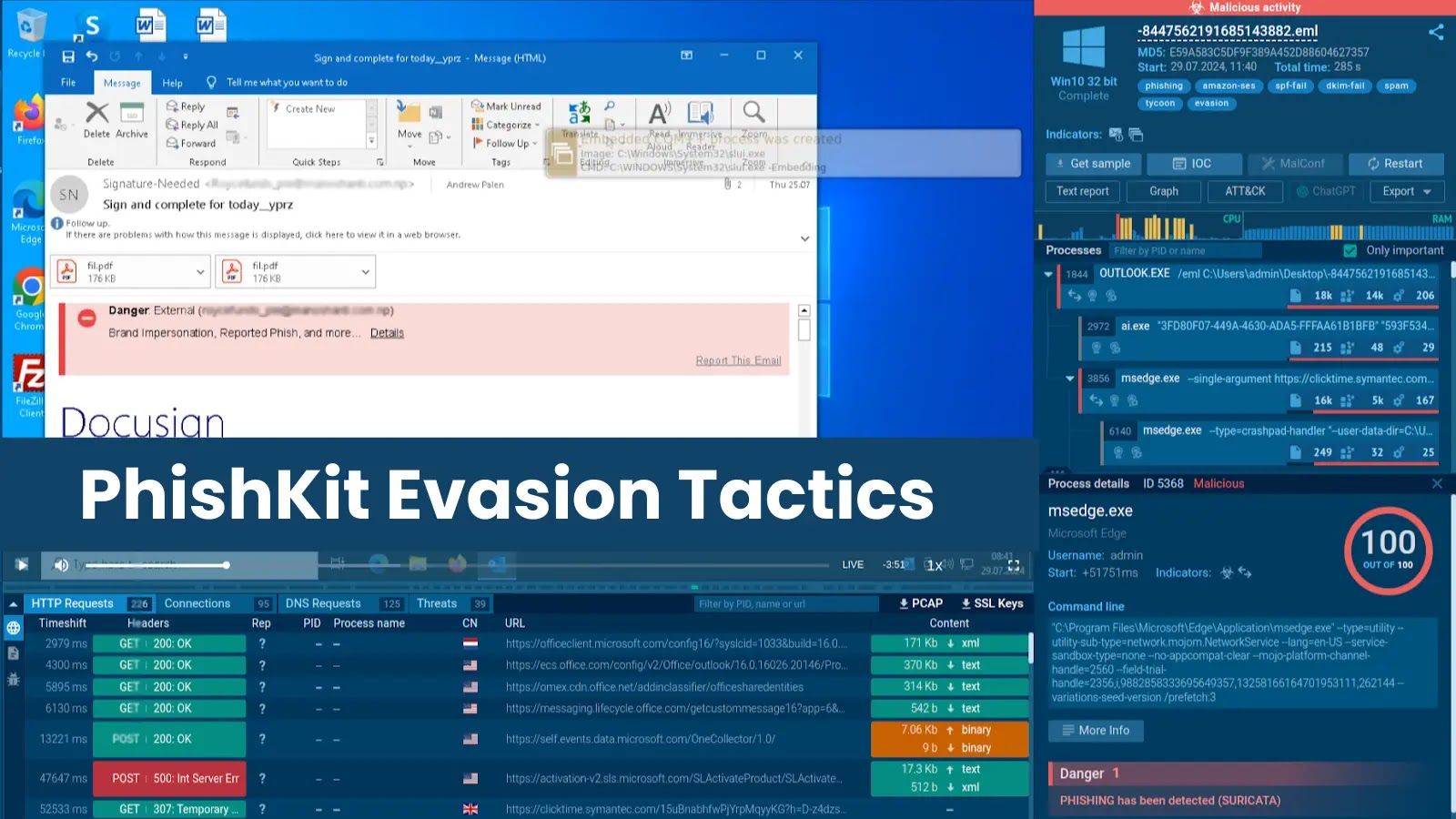
As NightSpire’s footprint expanded, safety researchers started to dissect its underlying infrastructure.
The ransomware binaries reveal a modular structure able to switching between block encryption and full encryption routines relying on file sort.
In keeping with reverse engineering by ASEC researchers, massive recordsdata corresponding to digital disk photos (.vhdx, .vmdk) and archives (.zip) are processed in 1 MB chunks utilizing an AES-CBC block encryption perform, whereas paperwork and smaller recordsdata endure full-file encryption with the identical cipher.
Encrypted file construction (Supply – ASEC)
By inserting the AES key on the finish of every encrypted file—then securing it with RSA and appending it to the file tail—NightSpire ensures that each automated and guide restoration with out cost stay nearly unattainable.
An infection Evaluation
NightSpire’s an infection mechanism hinges on a multi-stage loader that first disables Home windows Defender and deletes quantity shadow copies to forestall simple rollback.
The loader initiates by querying the OS with the _Stat() perform to enumerate accessible recordsdata and directories, filtering out system-critical paths to keep away from destabilizing the host.
Folder contaminated by NightSpire ransomware (Supply – ASEC)
As soon as the file system map is constructed, the next pseudocode outlines the encryption resolution logic:-
if (ext in {“.iso”, “.vhdx”, “.vmdk”, “.zip”, “.vib”, “.bak”, “.mdf”, “.flt”, “.ldf”}) {
main_EncryptFilev2(filePath, aesKey, rsaPubKey, chunkSize = 1MB);
} else {
main_EncryptFilev1(filePath, aesKey, rsaPubKey);
}
After encrypting every goal, the loader writes a readme.txt ransom observe in the identical folder, then communicates success to the group’s command-and-control server over an encrypted Telegram channel.
Throughout this part, the ransomware additionally screenshots the desktop and exfiltrates them alongside crucial paperwork, reinforcing its leverage. The result’s a fast, stealthy compromise that leaves conventional detection mechanisms scrambling.
Enhance your SOC and assist your group shield your online business with free top-notch menace intelligence: Request TI Lookup Premium Trial.