An enormous leak of inner tooling, backdoors, and intelligence-gathering artifacts attributed to North Korea’s state-sponsored APT group Kimsuky has been printed on-line by presumed insiders.
The 34,000-page dump exposes dwell phishing infrastructure, kernel-level backdoors, Cobalt Strike payloads, and stolen authorities certificates.
Key Takeaways1. Insider leak of Kimsuky’s full phishing toolkit concentrating on dcc.mil.kr.2. Discovery of Tomcat kernel LKM backdoor and customized Cobalt Strike beacon.3. Compromise contains stolen GPKI certificates, MoFA electronic mail code, and onnara_sso entry to inner South Korean networks.
Kimsuky Hackers Information Breach
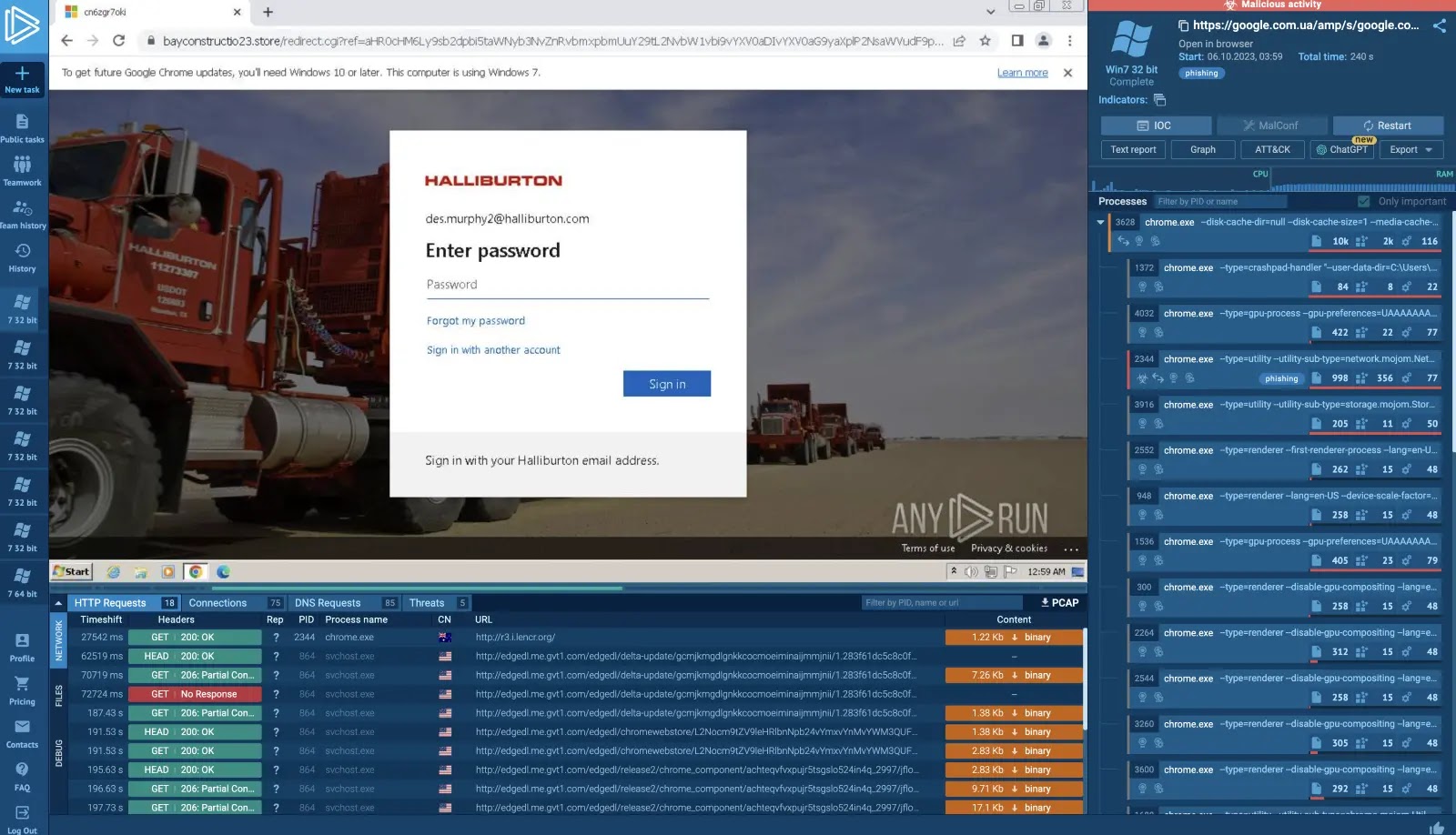
In line with Saber (“cyborg”) the archive contains the total supply for a customized phishing platform used towards South Korea’s Protection Counterintelligence Command (dcc.mil.kr). The breach reveals information akin to generator[.]php and config[.]php, containing:
An IP blacklist in config.php blocks safety vendor scanners (Pattern Micro, Google) from detecting the faux website.
Victims coming into credentials on the spoofed HTTPS area are instantly redirected again to a legit https://dcc.mil[.]kr URI, triggering a login error and masking the credential theft.
Among the many artifacts is a Tomcat Distant Kernel Backdoor (LKM) that detects a secret TCP SEQ + IP ID “knock” to spawn a hidden grasp.c course of:
As soon as triggered, the module opens an SSL-encrypted channel between attacker and sufferer. The hardcoded grasp password “Miu2jACgXeDsxd” stays fixed throughout deployments.
As well as, a Non-public Cobalt Strike Beacon written in Java was recovered, with configuration parameters:
BeaconType: HTTP
Port: 8172
SleepTime: 60842 ms
UserAgent: Mozilla/5.0 (appropriate; MSIE 9.0…)
The supply code listing (.thought/workspace.xml) reveals lively improvement as just lately as June 2024.
The leak additionally incorporates a full dump of the South Korea Ministry of International Affairs electronic mail server code (mofa.go.kr[.]7z) and stolen Authorities Public Key Infrastructure certificates protected by a cracked Java utility (cert.java).
Brute-force logs document repeated password makes an attempt (5697452641) towards unification.go.kr and spo.go[.]kr.
Builders planted an SSO instrument named onnara_sso with code referencing onnara9.saas.gcloud.go.kr, indicating persistent entry to inner authorities portals.
This unprecedented knowledge dump provides defenders a deep take a look at Kimsuky’s TTPs: port knocking, in-memory kernel implants, customized C2 frameworks, and abuse of stolen certificates.
Organizations in South Korea and allied nations ought to instantly audit uncovered code patterns, revoke compromised certificates, and deploy network-level detection for anomalous TCP SEQ/IP ID mixtures.
Increase your SOC and assist your staff defend what you are promoting with free top-notch risk intelligence: Request TI Lookup Premium Trial.