The Open VSX Registry and the Eclipse Basis have accomplished their investigation into a big safety incident involving uncovered developer tokens and malicious extensions.
The great response reveals how the platform is strengthening defenses throughout all the VS Code extension ecosystem following the breach.
The safety incident started when researchers at Wiz recognized a number of extension publishing tokens inadvertently uncovered by builders in public repositories.
Investigation confirmed {that a} restricted variety of tokens related to Open VSX accounts had been compromised, making a direct pathway for attackers to publish or modify extensions with out authorization.
The Open VSX workforce emphasised that these exposures resulted from developer errors moderately than infrastructure compromise, instantly revoking all affected tokens upon discovery. The publicity highlighted a vital vulnerability within the improvement workflow the place delicate credentials can simply slip into model management methods.
Understanding the Menace
Open VSX collaborated with Microsoft Safety Response Middle to introduce a brand new token prefix format particularly designed for simpler and extra correct scanning of uncovered tokens throughout public repositories, enabling builders and safety groups to establish compromised credentials sooner.
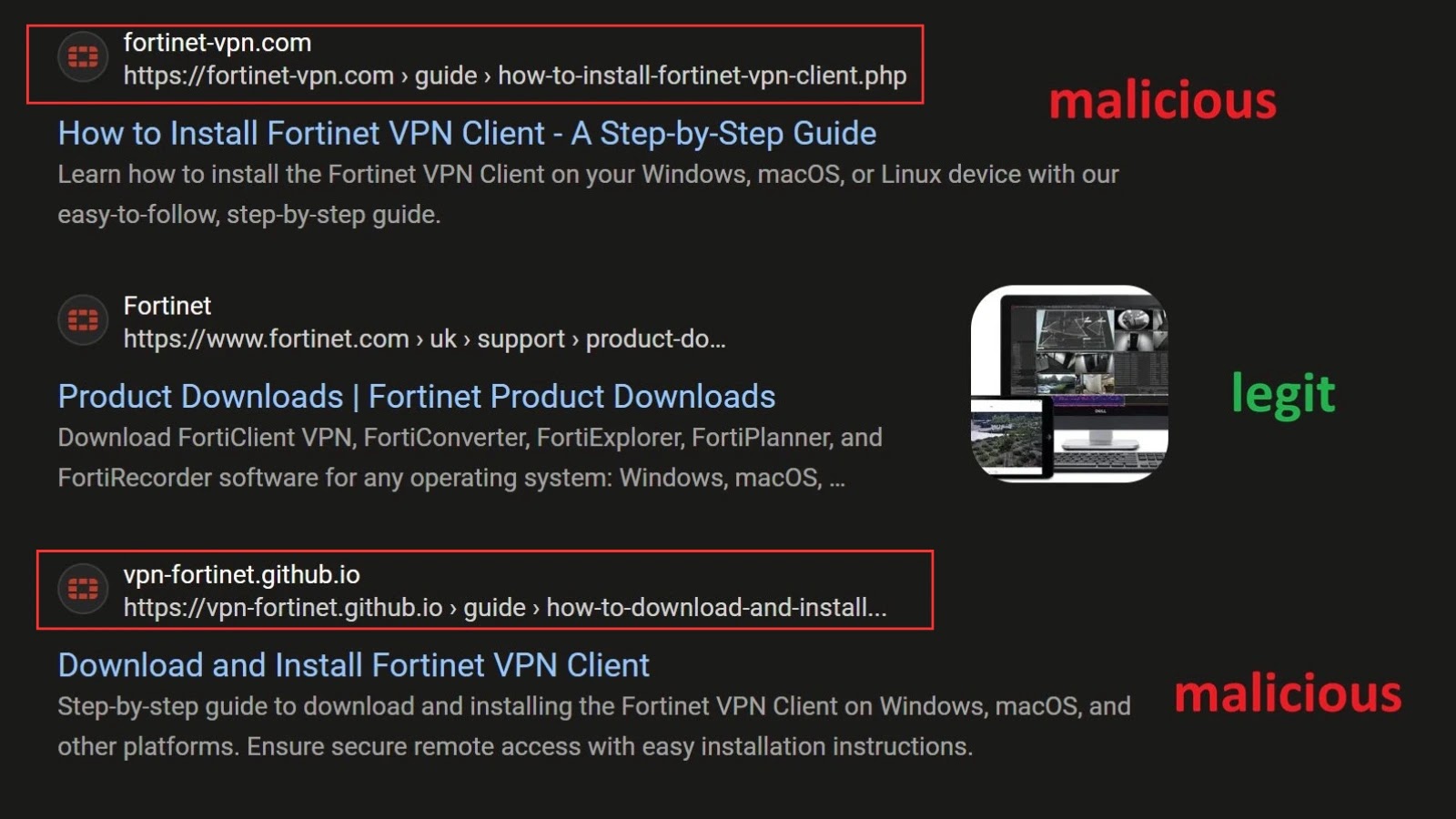
Safety researchers at Koi Safety subsequently recognized a coordinated malware marketing campaign known as “GlassWorm” that leveraged the leaked tokens to publish malicious extensions to the platform.
Whereas preliminary reviews characterised this as a self-propagating worm corresponding to the ShaiHulud incident on npm, Open VSX clarified that the malware operated in a different way.
The extensions have been designed to steal developer credentials, enabling attackers to increase their attain throughout the ecosystem, however the malware didn’t autonomously replicate or propagate throughout methods.
The marketing campaign resulted in a number of malicious extensions reaching {the marketplace} earlier than removing. Open VSX eliminated all recognized malicious extensions instantly upon notification and revoked or rotated related tokens immediately.
Nevertheless, reported obtain statistics require context. The cited determine of 35,800 downloads contains inflated counts generated by bot site visitors and visibility-boosting ways employed by risk actors, doubtlessly overstating precise person impression.
As of October 21, 2025, Open VSX declared the incident absolutely contained with no indication of ongoing compromise or remaining malicious extensions on the platform.
The response led to concrete enhancements strengthening platform safety, together with implementing shorter default token validity intervals to restrict leak impression, streamlining token revocation workflows for sooner response instances, and deploying automated safety scanning at publication to detect malicious code patterns earlier than extensions attain customers.
Open VSX continues intensive collaboration with affected builders, ecosystem companions, and unbiased researchers to keep up transparency and reinforce preventive measures.
These enhancements show how safety incidents, whereas disruptive, can drive significant ecosystem hardening and set up stronger protections for the broader developer neighborhood counting on open-source extension marketplaces.
Comply with us on Google Information, LinkedIn, and X for each day cybersecurity updates. Contact us to characteristic your tales.