The PureHVNC distant administration device (RAT) has emerged as a classy part of the Pure malware household, gaining prominence in mid-2025 amid an uptick in focused intrusion campaigns.
Originating from underground boards and Telegram channels, PureHVNC is marketed by its creator, often called PureCoder, alongside companion instruments comparable to PureCrypter, PureLogs, and PureMiner.
Its adoption by cybercriminal clients displays a rising demand for modular malware suites able to stealthy full system management and knowledge exfiltration.
Preliminary deployments have leveraged the ClickFix phishing method, luring victims with counterfeit job gives to execute malicious scripts, setting the stage for multi-stage intrusions.
In a single notable incident, attackers deployed a Rust Loader, adopted by PureHVNC RAT and the Sliver command-and-control framework over an eight-day window.
Test Level analysts famous that in this marketing campaign, PureHVNC communicated with its management server to retrieve three GitHub URLs internet hosting supporting modules, straight implicating the developer’s personal GitHub accounts within the malware’s operational infrastructure.
These GitHub repositories contained browser driver executables and plugin information important for TwitchBot and YouTubeBot functionalities, illustrating an uncommon developer-sourced provide chain for malware help information.
Past its preliminary infiltration ways, PureHVNC demonstrates superior capabilities for persistence and privilege escalation.
Upon execution, the RAT registers itself by way of scheduled duties named to imitate official Google Updater providers, guaranteeing resilience throughout reboots.
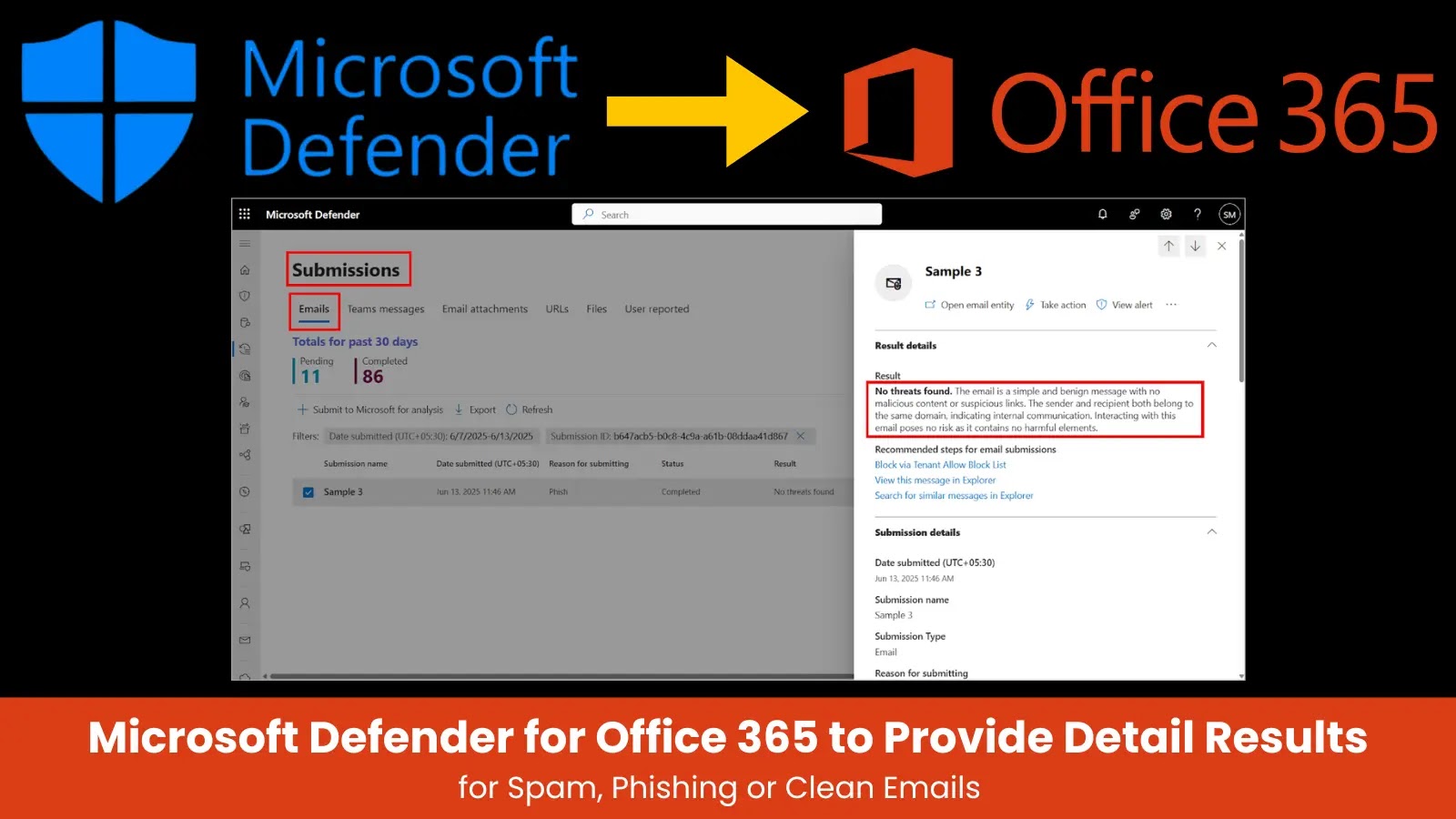
An infection chain (Supply – Test Level)
If operating with out administrative privileges, it prompts a UAC elevation loop utilizing PowerShell:-
whereas ($true) {
Begin-Course of -FilePath cmd[.]exe -Verb runas -ArgumentList ‘regsvr32[.]exe MALWARE[.]dll –typerenderer’
exit
}
As soon as elevated, the loader establishes a mutex (MistyRoseNavy) to forestall duplicate execution and creates a scheduled activity with a one-minute repetition interval.
ClickFix Immediate (Supply – Test Level)
This strategy, mixed with AMSI bypass by way of an LdrLoadDll hook, permits PureHVNC to stay undetected by real-time defenses whereas sustaining management of the endpoint.
An infection Mechanism
PureHVNC’s preliminary loader is a .NET meeting delivered by the Rust Loader shellcode. The loader decrypts its payload utilizing ChaCha20-Poly1305, validates payload dimension towards a 1 KB threshold, and allocates executable reminiscence to host the decrypted .NET meeting.
The embedded meeting is then loaded and executed, initializing the RAT’s primary loop. Communication is established over SSL streams, the place the bot sends Gzip-compressed system data—together with OS model, put in antivirus merchandise, and metadata like marketing campaign ID—to the C2 server.
Incoming instructions are acquired as compressed buffers, decompressed, deserialized, and dispatched to plugin threads for execution.
By segmenting payload supply and using encryption and compression, PureHVNC evades static signature detection and complicates network-based discovery, underscoring its stealthy an infection mechanism.
Free reside webinar on new malware ways from our analysts! Study superior detection strategies -> Register for Free