A complicated phishing marketing campaign leveraging the Snake Keylogger malware has emerged, exploiting reputable Java debugging utilities to bypass safety mechanisms and goal organizations worldwide.
The Russian-originated .NET malware, distributed by means of a Malware as a Service (MaaS) mannequin, represents a major evolution in cybercriminal ways by abusing trusted system parts that usually evade detection.
The marketing campaign employs spear-phishing emails themed round petroleum product gross sales, capitalizing on heightened geopolitical tensions within the Center East.
Instance of a spear phishing electronic mail (Supply – CN-SEC)
These malicious communications impersonate main oil firms, significantly focusing on organizations within the power sector throughout a interval of worldwide concern over potential disruptions to grease logistics by means of the Strait of Hormuz.
CN-SEC analysts recognized this marketing campaign as significantly noteworthy as a consequence of its unprecedented abuse of jsadebugd.exe, a reputable Java debugging utility that has by no means earlier than been documented for malicious functions.
The attackers show refined understanding of system structure by leveraging this trusted binary to execute their payload whereas sustaining stealth.
The malware employs a multi-stage an infection course of starting with compressed attachments containing the reputable jsadebugd.exe binary, renamed to seem as a petroleum-related doc.
When executed, the malware makes use of DLL sideloading methods to load malicious code by means of the jli.dll library, subsequently injecting the Snake Keylogger payload into the reputable InstallUtil.exe course of.
Superior Evasion By means of Binary Header Manipulation
The malware’s most refined evasion method includes storing the Snake Keylogger binary inside concrt141.dll whereas strategically positioning malicious code instantly earlier than the usual MZ header.
This placement permits the payload to stay hidden from standard signature-based detection programs that depend on customary PE file construction evaluation.
The binary header manipulation could be noticed within the malware’s construction:-
Offset (h) 00 01 02 03 04 05 06 07 08 09 0A 0B 0C 0D 0E 0F
00000000 00 01 00 00 00 00 72 01 00 4D 5A 90 00 03 00 00
This method successfully masks the malicious payload whereas sustaining file legitimacy.
The malware establishes persistence by means of registry modification at SOFTWAREMicrosoftWindowsCurrentVersionRun, guaranteeing continued execution throughout system reboots whereas copying parts to %USERPROFILEpercentSystemRootDoc.
Upon profitable set up, Snake Keylogger harvests credentials from over 40 browsers and functions, together with Chrome, Firefox, Microsoft Outlook, and FileZilla, whereas amassing system data by means of reputable providers like reallyfreegeoip.org.
The stolen information is exfiltrated through SMTP to attacker-controlled electronic mail addresses, finishing a complete information theft operation.
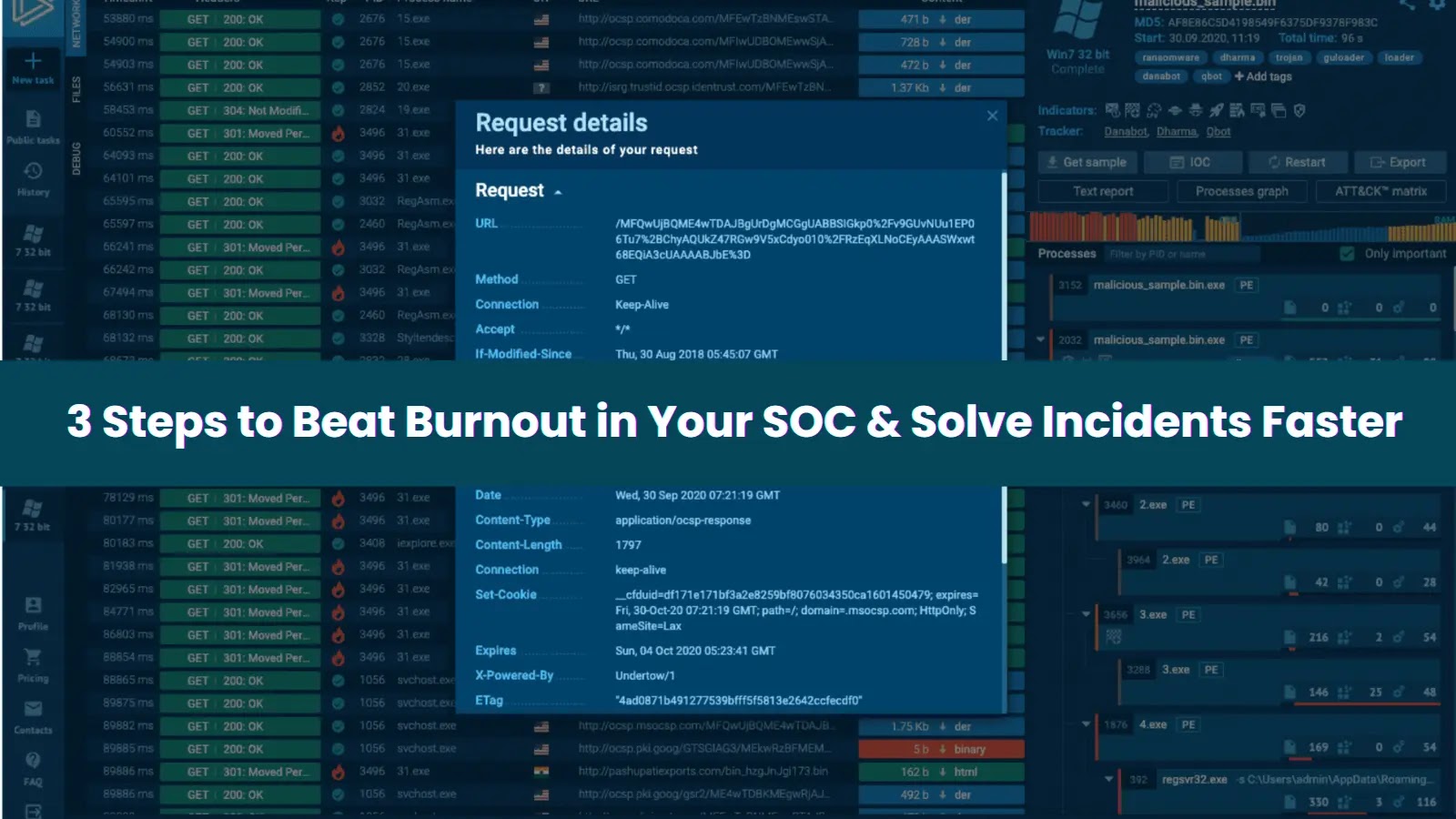
Examine reside malware conduct, hint each step of an assault, and make sooner, smarter safety selections -> Strive ANY.RUN now