A complicated intrusion during which menace actors co-opted the reliable, open-source Velociraptor digital forensics and incident response (DFIR) software to determine a covert distant entry channel.
This represents an evolution from the long-standing tactic of abusing distant monitoring and administration (RMM) utilities, with attackers now repurposing DFIR frameworks to reduce customized malware deployment and evade detection.
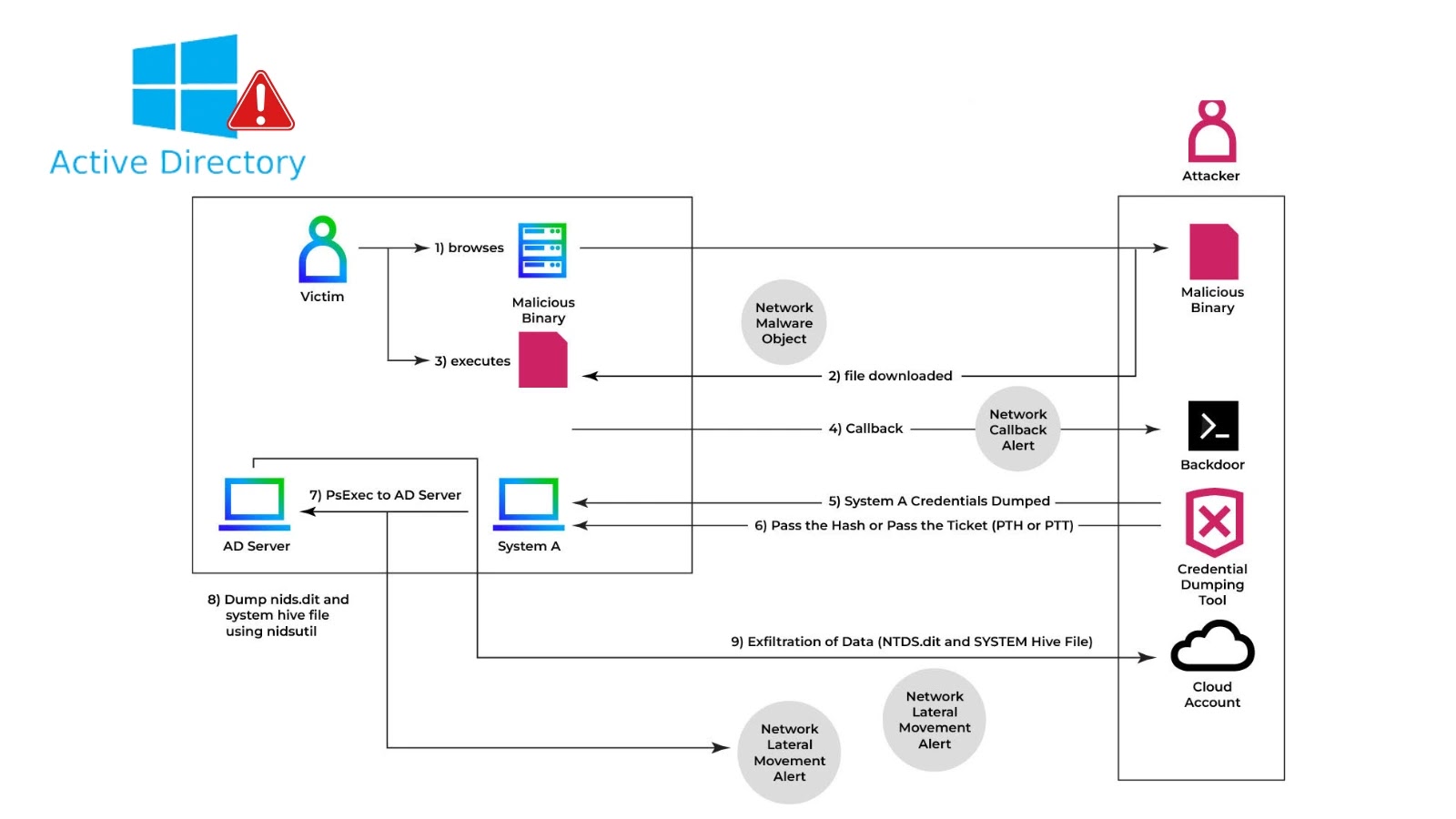
Through the assault, the adversary leveraged the native Home windows msiexec utility to obtain and set up a malicious Velociraptor MSI bundle from a Cloudflare Employees–hosted staging area, recordsdata.qaubctgg.employees.dev.
This staging space additionally housed different attacker instruments, comparable to a Cloudflare tunneling element and the Radmin distant administration software. As soon as put in, Velociraptor was configured to speak with a command-and-control (C2) server at velo.qaubctgg.employees[.]dev.
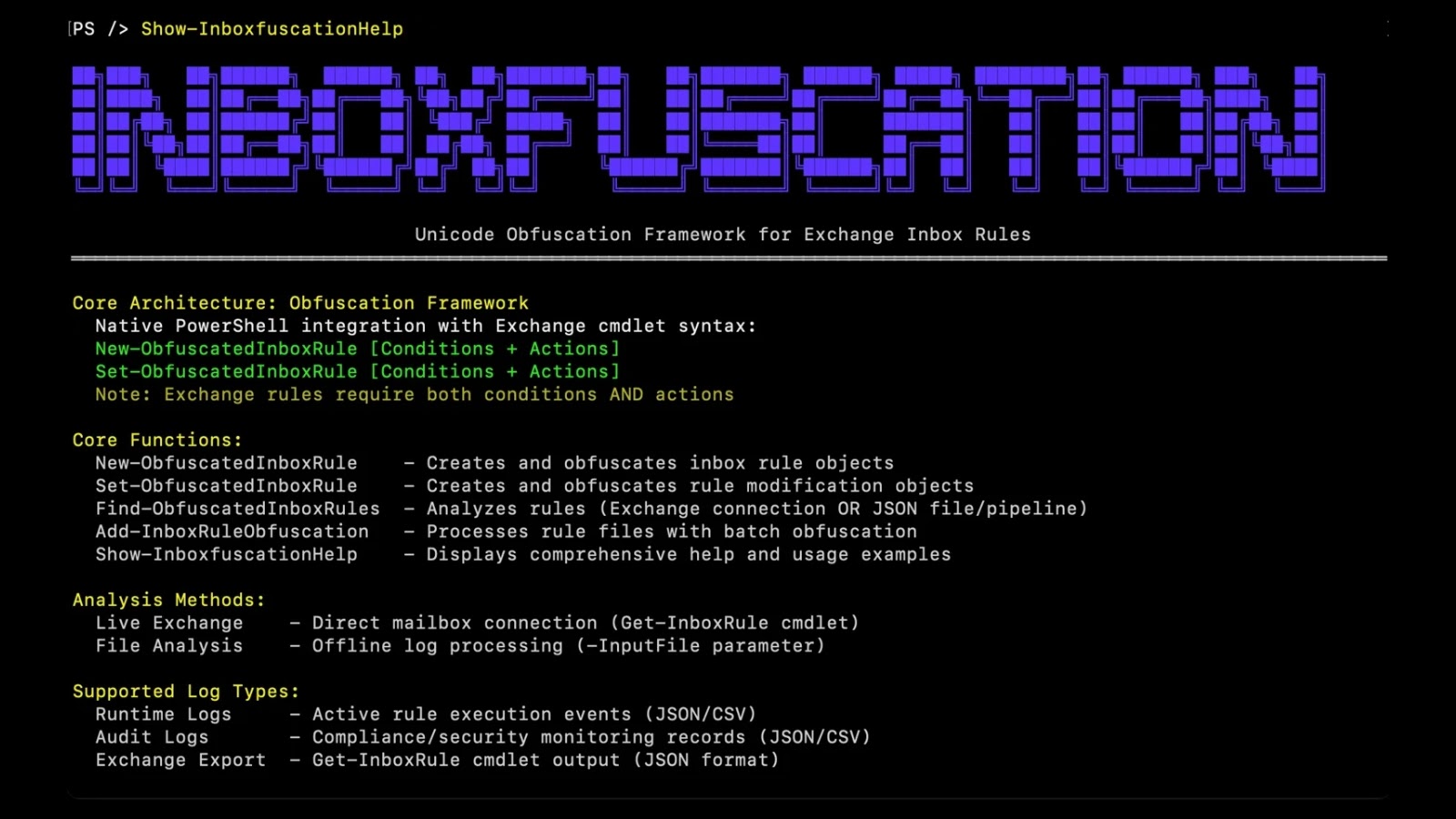
Subsequent, the intruder executed an obfuscated PowerShell command to retrieve Visible Studio Code (code.exe) from the identical employees.dev folder and ran it with the built-in tunnel characteristic enabled.
Course of tree exhibiting Velociraptor creating Visible Studio Code tunnel.
By putting in code.exe as a Home windows service and redirecting its output to a log file, the menace actor successfully created a persistent, encrypted tunnel to the attacker’s C2 infrastructure.
This system bypassed many conventional safety controls, because the tunneling characteristic in Visible Studio Code is usually used legitimately by builders for distant collaboration, in keeping with Sophos’ investigation.
In response, CTU analysts offered the affected group with mitigation steering, enabling speedy isolation of the compromised host. This containment measure prevented the adversary from advancing to their final objective of ransomware deployment.
Though distant entry abuse by way of RMM instruments is a well-recognized tactic documented in earlier incidents involving SimpleHelp vulnerabilities and digital machine–primarily based instruments, this case marks one of many first noticed cases during which DFIR software program itself was weaponized.
By pivoting to Velociraptor, the attackers decreased reliance on bespoke malware, reducing their operational footprint and complicating attribution.
CTU’s evaluation signifies that this tradecraft must be handled as a probable precursor to ransomware. Organizations are subsequently suggested to:
Monitor unauthorized deployments of DFIR and incident response instruments, together with Velociraptor, throughout endpoints and servers.
Implement complete EDR methods able to detecting atypical processes and suspicious command traces.
Implement strict utility allow-listing insurance policies to dam unapproved installers and repair creations.
Frequently audit community site visitors for surprising encrypted tunnels or anomalous C2 beaconing.
Keep sturdy, offline backups and rehearse ransomware restoration plans.
Safety groups ought to assessment and prohibit entry to those domains, considering the danger of interacting with probably malicious content material.
Indicator TypeDomainDescriptionInstallerfiles.qaubctgg.employees.dev/v2.msiVelociraptor MSI packageTunneling Toolfiles.qaubctgg.employees.dev/code.exeVisual Studio Code executableAdditional MSIworkers.dev/sc.msiSecondary malware installer
By treating unauthorized use of incident response instruments as a high-risk occasion and adopting layered detection and prevention measures, organizations can considerably scale back the influence of such assaults and halt adversaries earlier than they deploy ransomware.
Discover this Story Fascinating! Comply with us on LinkedIn and X to Get Extra On the spot Updates.