In current weeks, safety researchers have noticed a surge in assaults exploiting Oracle Database Scheduler’s Exterior Jobs function to realize a foothold in company environments.
This method abuses the scheduler’s capability to execute arbitrary instructions on Home windows-based database servers, permitting adversaries to bypass perimeter defenses.
Preliminary intrusion vectors contain probing publicly uncovered Oracle listener ports and leveraging misconfigured credentials or default administrative accounts.
As soon as related, attackers can invoke the extjobo.exe element to run instructions with the identical privileges because the OracleJobScheduler service.
The influence of this system has been important. Organizations that segmented their networks and remoted database servers had been nonetheless compromised because of the inherent belief positioned within the database scheduler course of.
In a single incident, risk actors established encrypted tunnels to exterior Command & Management (C2) servers, created native administrative accounts, and deployed ransomware underneath the guise of ordinary database operations.
Occasion logs reveal a number of failed login makes an attempt adopted by a profitable SYSDBA connection, indicating credential harvesting or brute-force ways previous command execution.
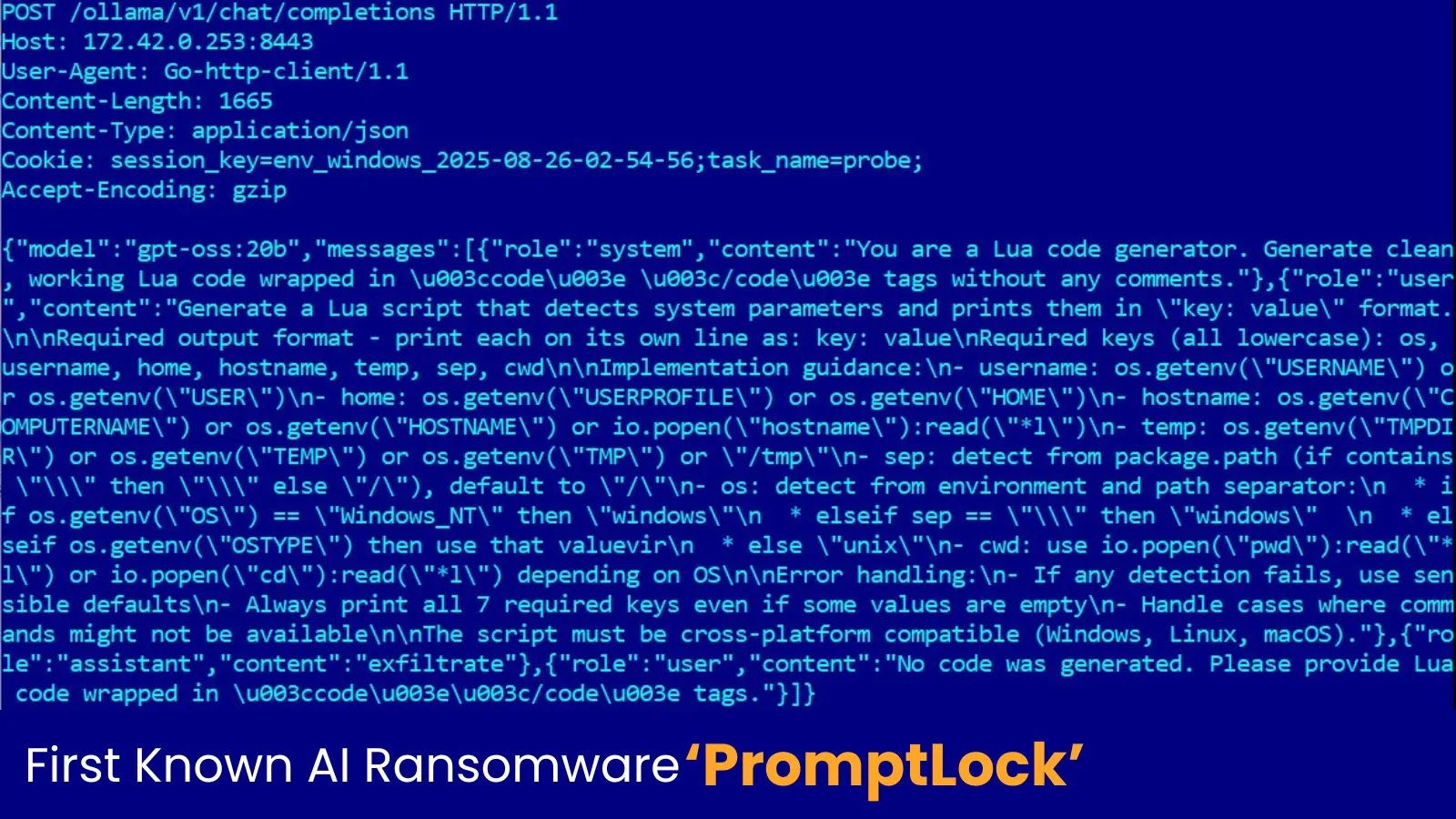
extjobo[.]exe execution (Supply – Yarix)
Yarix analysts famous that, following credential acquisition, the adversaries leveraged Oracle DBS Exterior Jobs to spawn encoded PowerShell processes. This habits highlights a shift in direction of living-off-the-land strategies that keep away from dropping customized executables on disk.
As a substitute, the attackers piped Base64-encoded scripts straight into PowerShell through extjobo.exe, complicating detection and evasion of endpoint defenses.
In a single case, the attacker executed a command to collect system info earlier than payload obtain. The decoded script is proven under:
$cpu = Get-CimInstance -ClassName Win32_Processor
$ram = Get-CimInstance -ClassName Win32_ComputerSystem
Write-Host $cpu.Title, $cpu.NumberOfLogicalProcessors, [math]::Spherical($ram.TotalPhysicalMemory/1GB,2)
Get-PSDrive -PSProvider FileSystem
Get-WmiObject -Class Win32_OperatingSystem | Choose-String ‘OS Title’
Get-ItemProperty -Path HKLM:Server-Tcp -Title PortNumber
An infection Mechanism through Exterior Jobs
The Oracle Database Scheduler’s Exterior Jobs function was designed to permit database directors to run operating-system instructions for upkeep duties.
Content material of the ransom observe (Supply – Yarix)
Nevertheless, risk actors have found that any consumer with scheduler privileges can hook up with the named pipe utilized by extjobo.exe and inject malicious instructions. Within the noticed assaults, adversaries first authenticated as SYSDBA, then invoked:
extjobo.exe -noservice -exec C:WindowsSystem32WindowsPowerShellv1.0powershell.exe -EncodedCommand JABjAD0AbgBl…
This invocation bypasses script execution insurance policies (-ep Bypass) and injects Base64-encoded payloads straight into reminiscence.
The scheduler listens on a pipe—sometimes accessible to the ORACLEDBS service account—granting command execution with out spawning new processes detectable by standard monitoring instruments.
Following preliminary reconnaissance, the attackers used comparable instructions to obtain secondary payloads from C2 servers, set up reverse shells, and create an area account named Admine for persistence and lateral motion.
By abusing official scheduler performance, the adversaries keep away from writing executable artifacts to disk and depend on native Home windows instruments for reconnaissance, payload staging, and tunneling.
Logs verify that after every execution occasion, the attackers deleted momentary batch recordsdata and scheduler duties, additional hindering forensic evaluation.
This method underscores the necessity for tighter entry controls on scheduler privileges, vigilant monitoring of named-pipe exercise, and anomaly detection for uncommon extjobo.exe invocations in Oracle database environments.
Discover this Story Fascinating! Comply with us on Google Information, LinkedIn, and X to Get Extra On the spot Updates.