Between August and October 2025, a complicated phishing marketing campaign has emerged concentrating on Colombian and Spanish-speaking customers by way of misleading emails masquerading as official communications from Colombia’s Lawyer Common’s workplace.
The marketing campaign employs a rigorously crafted social engineering technique, luring victims with notifications about supposed lawsuits processed by way of labor courts.
This marks a big shift in assault ways as risk actors broaden PureHVNC deployment into areas beforehand untouched by this malware.
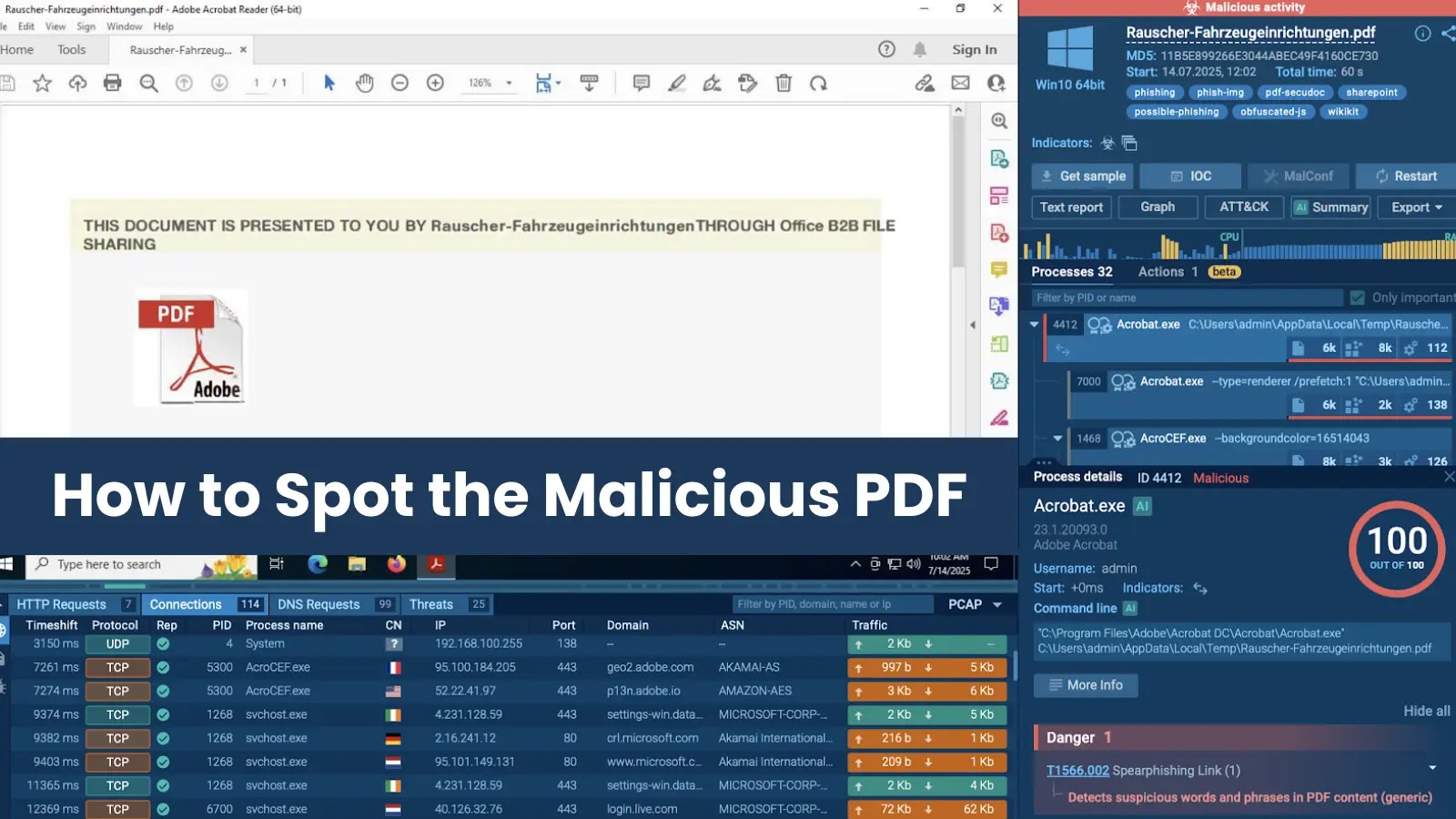
Instance e mail (Supply – IBM)
The assault chain begins when recipients encounter an e mail containing an SVG attachment that leads them by way of Google Drive, the place clicking on the doc triggers an automated obtain of a password-protected ZIP archive.
7 ZIP archive contents (Supply – IBM)
Inside this archive lies a renamed executable disguised with a judiciary-themed filename “02 BOLETA FISCAL.exe”, which is definitely a authentic javaw.exe file repurposed for malicious DLL side-loading.
This preliminary stage deploys Hijackloader, an more and more prevalent loader beforehand noticed delivering RemcosRAT to CrowdStrike clients.
IBM X-Drive analysts recognized this marketing campaign as significantly noteworthy as a result of it represents the primary noticed occasion of PureHVNC being delivered to Spanish-speaking customers by way of such coordinated efforts.
The malware, sometimes bought on darkish internet boards and Telegram channels by PureCoder, demonstrates superior evasion capabilities that separate it from normal distant entry trojans.
An infection Mechanism and Persistence
The malware operates by way of a complicated multi-stage an infection course of designed to evade safety detection.
The assault exploits DLL side-loading, the place the malicious JLI.dll hijacks Home windows’ library loading procedures to inject the second-stage payload MSTH7EN.dll immediately into reminiscence utilizing the LoadLibraryW() API perform.
This shellcode ultimately masses into vssapi.dll by way of reminiscence manipulation strategies involving VirtualProtect() calls that modify the .textual content part to PAGE_EXECUTE_READWRITE permissions.
The third-stage payload comprises encrypted configuration knowledge together with course of identify hashes that set off execution delays when safety software program is detected.
When activated, the malware queries operating processes and makes use of NtDelayExecution() API calls to pause execution, demonstrating consciousness of its operational surroundings.
The whole an infection chain in the end establishes communication with the command server sofiavergara[.]duckdns[.]org, granting attackers full distant entry over compromised techniques.
This marketing campaign highlights how judicial and authorized themes proceed serving as efficient social engineering vectors, significantly in opposition to authorities and company workers in Latin America.
Comply with us on Google Information, LinkedIn, and X to Get Extra Instantaneous Updates, Set CSN as a Most well-liked Supply in Google.