In a classy marketing campaign uncovered throughout a latest Superior Continuous Menace Hunt (ACTH) by Trustwave’s SpiderLabs group, menace actors weaponized a legit distant administration software, ScreenConnect, to deploy the Xworm Distant Entry Trojan (RAT) by a misleading, multi-stage an infection chain.
By abusing pretend AI-themed content material and manipulating digital signatures, the attackers bypassed Endpoint Detection and Response (EDR) alerts and relied on human-led menace looking to disclose the hidden payloads.
The operation started with social engineering lures masquerading as AI video recordsdata. Victims had been enticed to go to a pretend AI web site, “gptgrok[.]ai,” which redirected to “anhemvn6[.]com.”
There, customers downloaded a file named “Creation_Made_By_GrokAI.mp4 Grok.com” that was the truth is the “ScreenConnect.ClientSetup.msi” installer. Variations together with “Creation_Made_By_GoogleAI.mp4 Google.com” and “Creation_Made_By_SoraAI.mp4 OpenAI.com” recommend a broad marketing campaign leveraging AI buzzwords for credibility.
Code-Signing Certificates Abuse
Curiously, collected samples confirmed that the menace actors manipulated Authenticode Microsoft code-signing certificates to embed malicious configurations inside the digital signature of the legit ScreenConnect binary.
A legitimate signature for a modified ScreenConnect installer.
As soon as executed, the installer dropped and launched the ScreenConnect shopper within the consumer’s Temp listing. Preconfigured to run hidden, it linked silently to an attacker-controlled ScreenConnect server through a relay, utilizing parameters embedded inside the authenticode signature to evade tampering and preserve a sound digital signature.
Visible indicators resembling icons and notifications had been disabled, making certain the session remained invisible to the top consumer.
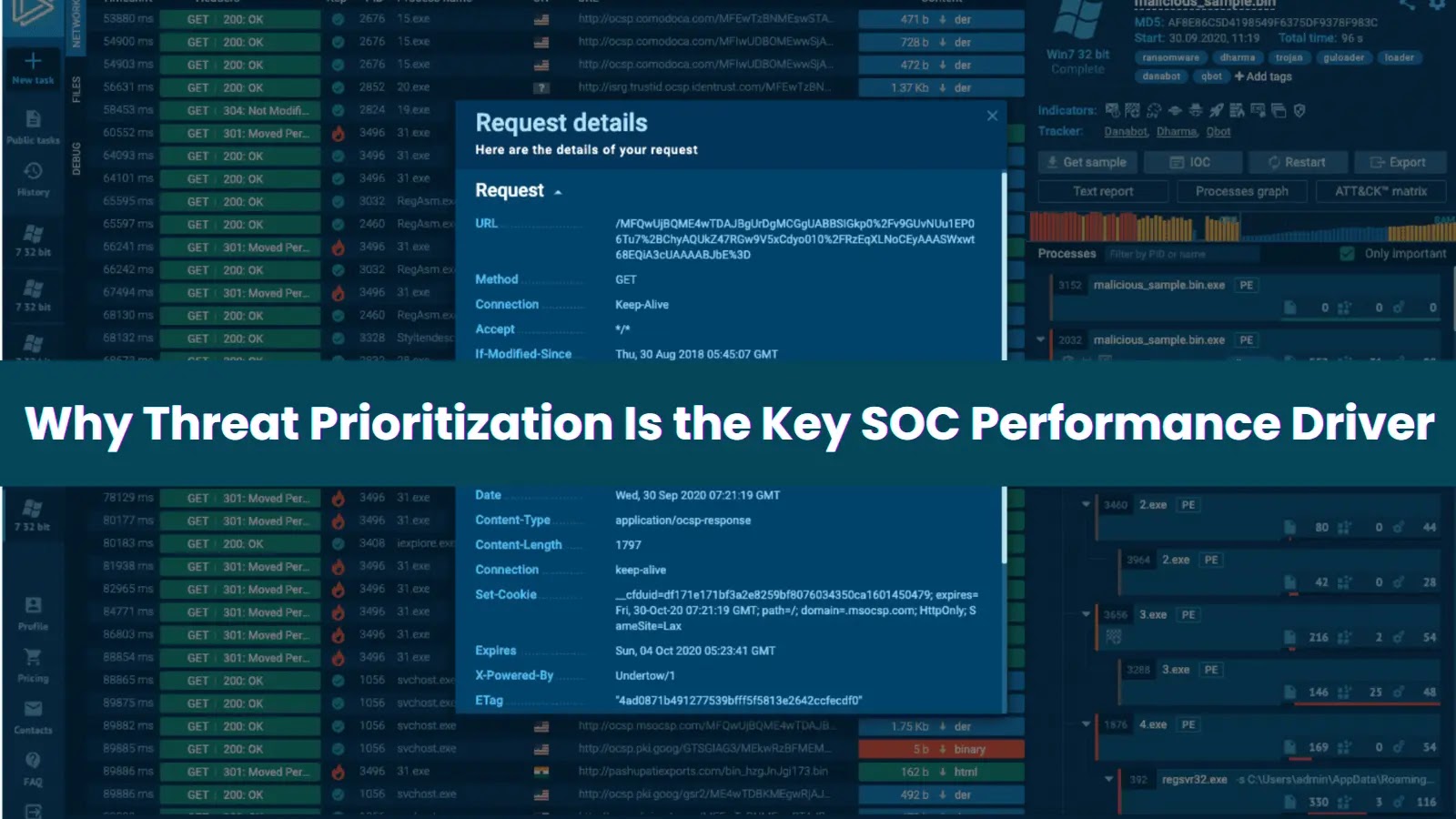
In the course of the distant entry session, the attackers deployed a batch script, “X-META Firebase_crypted.bat,” triggering mshta.exe to launch one other hidden batch file. This script downloaded and unpacked “5btc.zip” from “anhemvn4[.]com,” revealing a Python interpreter renamed to pw.exe and an encoded “basse64.txt” payload.
As an alternative of saving malicious code to disk, the menace actors used msedge.exe and chrome.exe course of hollowing—injecting Base64–encoded Python instructions fetched straight from a public GitHub repository. This fileless execution approach hindered static detection and allowed Xworm RAT elements to be delivered stealthily.
basse64.txt being acknowledged as a recognized stealer on VirusTotal.
Persistence was established by making a Run key in HKEY_CURRENT_USERSoftwareMicrosoftWindowsCurrentVersionRun named “Home windows Safety,” pointing to a “backup.bat” script in “C:xmetavip.”
On every login, this script re-launched pw.exe with new Base64 instructions, fetching extra payloads resembling “buquabua.txt” to take care of long-term entry.
The marketing campaign additionally included credential entry and discovery phases. WMI queries gathered working system and antivirus particulars, whereas the RAT tried to reap browser-stored login knowledge from Chrome, Edge, and Firefox profiles.
SpiderLabs analysts famous that the GitHub repository internet hosting the obfuscated Python scripts contained eleven recordsdata—cut up between persistence implanters and complicated RAT loaders created only a week earlier than the assault.
One closing payload script, “Exppiyt.txt,” embedded a command-and-control server IP (5[.]181[.]165[.]102:7705) that was not flagged as malicious on VirusTotal on the time of research.
This incident highlights a rising pattern: attackers are co-opting trusted instruments and AI branding to bypass automated defenses. Fashionable EDR and signature-based options struggled to detect this menace, underscoring the important function of proactive, human-led menace looking.
The SpiderLabs group’s investigation demonstrated that solely by meticulous handbook timeline evaluation and behavioral looking can these stealthy assaults be revealed.
As adversaries refine their tradecraft, leveraging code-signing manipulation, fileless execution, and legit administration platforms, organizations should spend money on expert menace hunters who can assume like attackers.
The SpiderLabs findings reinforce the strategic benefit of mixing automated detection with professional evaluation to uncover hidden threats earlier than they will inflict harm.
Appendix – Indicators of compromise:
Discover this Story Fascinating! Observe us on LinkedIn and X to Get Extra Prompt Updates.