An deserted replace server related to enter technique editor (IME) software program Sogou Zhuyin was leveraged by menace actors as a part of an espionage marketing campaign to ship a number of malware households, together with C6DOOR and GTELAM, in assaults primarily concentrating on customers throughout Jap Asia.
“Attackers employed refined an infection chains, resembling hijacked software program updates and pretend cloud storage or login pages, to distribute malware and gather delicate data,” Development Micro researchers Nick Dai and Pierre Lee stated in an exhaustive report.
The marketing campaign, recognized in June 2025, has been codenamed TAOTH by the cybersecurity firm. Targets of the exercise primarily embody dissidents, journalists, researchers, and know-how/enterprise leaders in China, Taiwan, Hong Kong, Japan, South Korea, and abroad Taiwanese communities. Taiwan accounts for 49% of all targets, adopted by Cambodia (11%) and the U.S. (7%).
It is stated the attackers, in October 2024, took management of the lapsed area title (“sogouzhuyin[.]com”) related to Sogou Zhuyin, a reliable IME service that stopped receiving updates in June 2019, to disseminate malicious payloads a month later. It is estimated that a number of hundred victims had been impacted.
“The attacker took over the deserted replace server and, after registering it, used the area to host malicious updates since October 2024,” the researchers stated. “Via this channel, a number of malware households have been deployed, together with GTELAM, C6DOOR, DESFY, and TOSHIS.”
The deployed malware households serve completely different functions, together with distant entry (RAT), data theft, and backdoor performance. To evade detection, the menace actors additionally leveraged third-party cloud companies to hide their community actions throughout the assault chain.
These malware strains allow distant entry, data theft, and backdoor performance, with the attackers additionally utilizing reliable cloud storage companies like Google Drive as an information exfiltration level and to hide the malicious community site visitors.
The assault chain begins when unsuspecting customers obtain the official installer for Sogou Zhuyin from the Web, such because the Conventional Chinese language Wikipedia web page entry for Sogou Zhuyin, which, in March 2025, was modified to level customers to the malicious area dl[.]sogouzhuyin[.]com.
Whereas the installer is totally innocuous, the malicious exercise kicks in when the automated replace course of is triggered a few hours after set up, inflicting the updater binary, “ZhuyinUp.exe,” to fetch an replace configuration file from an embedded URL: “srv-pc.sogouzhuyin[.]com/v1/improve/model.”
It is this replace course of that has been tampered with to DESFY, GTELAM, C6DOOR, and TOSHIS with the final word aim of profiling and gathering information from high-value targets –
TOSHIS (First detected December 2024), a loader designed to fetch next-stage payloads (Cobalt Strike or Merlin agent for Mythic framework) from an exterior server. It is also a variant of Xiangoop, which has been attributed to Tropic Trooper and has been used to ship Cobalt Strike or a backdoor referred to as EntryShell prior to now.
DESFY (First detected Might 2025), a spy ware that collects file names from two areas: Desktop and Program Recordsdata
GTELAM (First detected Might 2025), one other spy ware that collects file names matching a particular set of extensions (PDF, DOC, DOCX, XLS, XLSX, PPT, and PPTX), and exfiltrates the small print to Google Drive
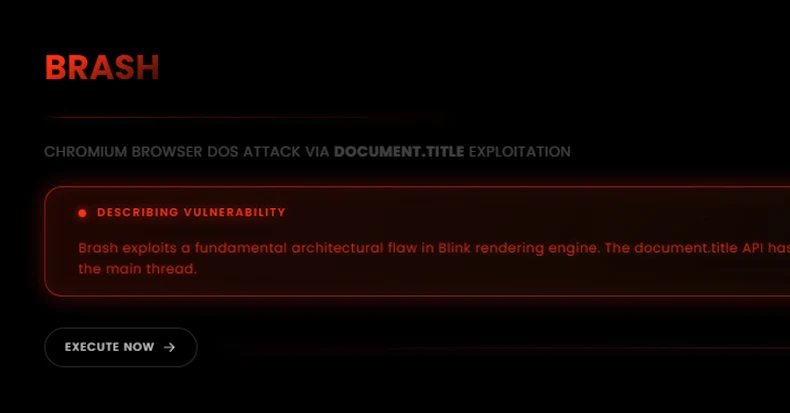
C6DOOR, a bespoke Go-based backdoor that makes use of HTTP and WebSocket protocols for command-and-control in order to obtain directions to assemble system data, run arbitrary instructions, carry out file operations, add/obtain recordsdata, seize screenshots, listing working processes, enumerate directories, and inject shellcode right into a focused course of
Additional evaluation of C6DOOR has uncovered the presence of embedded Simplified Chinese language characters inside the pattern, suggesting that the menace actor behind the artifact could also be proficient in Chinese language.
“It seems that the attacker was nonetheless within the reconnaissance section, primarily in search of high-value targets,” Development Micro stated. “In consequence, no additional post-exploitation actions had been noticed within the majority of sufferer programs. In one of many circumstances we analyzed, the attacker was inspecting the sufferer’s atmosphere and establishing a tunnel utilizing Visible Studio Code.”
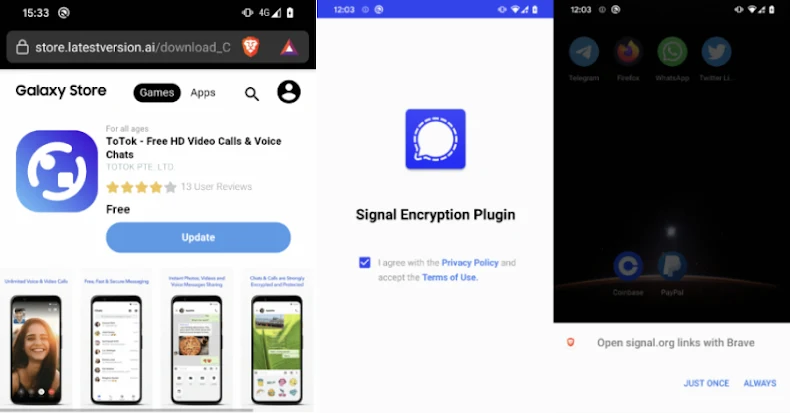
Apparently, there’s proof that TOSHIS was additionally distributed to targets utilizing a phishing web site, seemingly in reference to a spear-phishing marketing campaign concentrating on Jap Asia and, to a lesser extent, Norway and the U.S. The phishing assaults have additionally been noticed adopting a two-pronged method –
Serving faux login pages with lures associated to free coupons or PDF readers that redirect and grant OAuth consent to attacker-controlled apps, or
Serving faux cloud storage pages that mimic Tencent Cloud StreamLink to obtain malicious ZIP archives containing TOSHIS
These phishing emails embody a booby-trapped URL and a decoy doc that methods the recipient into interacting with the malicious content material, in the end activating a multi-stage assault sequence designed to drop TOSHIS utilizing DLL side-loading or get hold of unauthorized entry and management over their Google or Microsoft mailboxes by an OAuth permission immediate.
Development Micro stated the TAOTH shares infrastructure and tooling overlap with beforehand documented menace exercise by ITOCHU, portray the image of a persistent menace actor with a concentrate on reconnaissance, espionage, and electronic mail abuse.
To fight these threats, organizations are beneficial to routinely audit their environments for any end-of-support software program and promptly take away or substitute such functions. Customers are urged to evaluate the permissions requested by cloud functions earlier than granting entry.
“Within the Sogou Zhuyin operation, the menace actor maintained a low profile, conducting reconnaissance to determine beneficial targets amongst victims,” the corporate stated. “In the meantime, within the ongoing spear-phishing operations, the attacker distributed malicious emails to the targets for additional exploitation.”