Jun 12, 2025The Hacker NewsArtificial Intelligence / SaaS Safety
AI is altering every little thing — from how we code, to how we promote, to how we safe. However whereas most conversations concentrate on what AI can do, this one focuses on what AI can break — when you’re not paying consideration.
Behind each AI agent, chatbot, or automation script lies a rising variety of non-human identities — API keys, service accounts, OAuth tokens — silently working within the background.
And here is the issue:
🔐 They’re invisible
🧠 They’re highly effective
🚨 They’re unsecured
In conventional id safety, we defend customers. With AI, we have quietly handed over management to software program that impersonates customers — usually with extra entry, fewer guardrails, and no oversight.
This is not theoretical. Attackers are already exploiting these identities to:
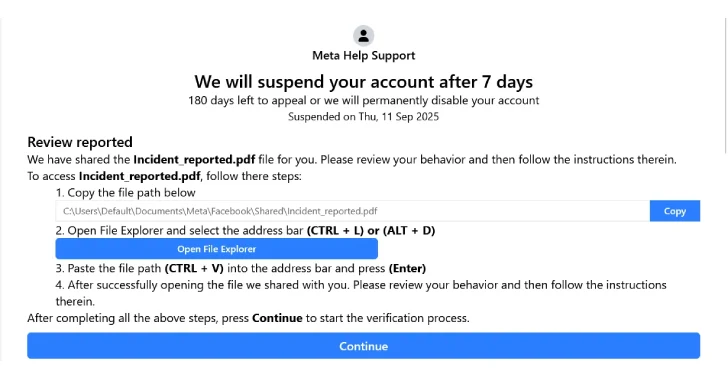
Transfer laterally by cloud infrastructure
Deploy malware through automation pipelines
Exfiltrate information — with out triggering a single alert
As soon as compromised, these identities can silently unlock vital techniques. You aren’t getting a second probability to repair what you may’t see.
In the event you’re constructing AI instruments, deploying LLMs, or integrating automation into your SaaS stack — you are already relying on NHIs. And chances are high, they are not secured. Conventional IAM instruments aren’t constructed for this. You want new methods — quick.
This upcoming webinar, “Uncovering the Invisible Identities Behind AI Brokers — and Securing Them,” led by Jonathan Sander, Area CTO at Astrix Safety, isn’t one other “AI hype” discuss. It is a wake-up name — and a roadmap.
What You will Study (and Really Use)
How AI brokers create unseen id sprawl
Actual-world assault tales that by no means made the information
Why conventional IAM instruments cannot defend NHIs
Easy, scalable methods to see, safe, and monitor these identities
Most organizations do not realize how uncovered they’re — till it is too late.
Watch this Webinar
This session is important for safety leaders, CTOs, DevOps leads, and AI groups who cannot afford silent failure.
The earlier you acknowledge the chance, the quicker you may repair it.
Seats are restricted. And attackers aren’t ready. Reserve Your Spot Now
Discovered this text fascinating? This text is a contributed piece from one in all our valued companions. Observe us on Twitter and LinkedIn to learn extra unique content material we submit.