Sep 11, 2025Ravie LakshmananMalware / Credential Theft
Cybersecurity researchers have disclosed particulars of a brand new marketing campaign that leverages ConnectWise ScreenConnect, a authentic Distant Monitoring and Administration (RMM) software program, to ship a fleshless loader that drops a distant entry trojan (RAT) known as AsyncRAT to steal delicate information from compromised hosts.
“The attacker used ScreenConnect to achieve distant entry, then executed a layered VBScript and PowerShell loader that fetched and ran obfuscated elements from exterior URLs,” LevelBlue stated in a report shared with The Hacker Information. “These elements included encoded .NET assemblies finally unpacking into AsyncRAT whereas sustaining persistence through a pretend ‘Skype Updater’ scheduled job.”
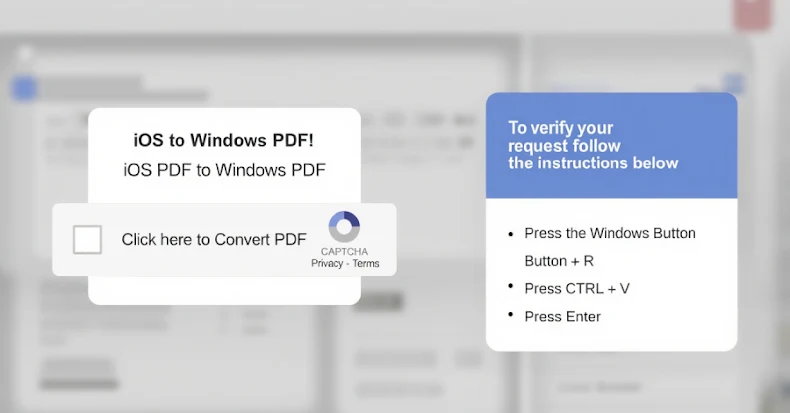
Within the an infection chain documented by the cybersecurity firm, the menace actors have been discovered to leverage a ScreenConnect deployment to provoke a distant session and launch a Visible Primary Script payload through hands-on-keyboard exercise.
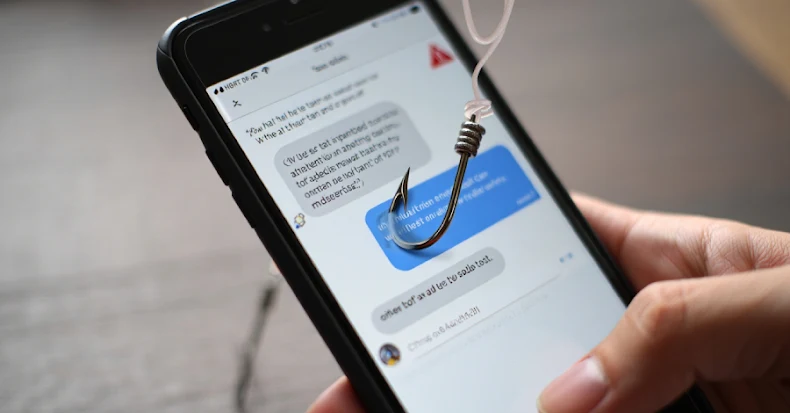
“We noticed trojanized ScreenConnect installers masquerading as monetary and different enterprise paperwork being despatched through phishing emails,” Sean Shirley, LevelBlue MDR SOC Analyst, instructed The Hacker Information.
The script, for its half, is designed to retrieve two exterior payloads (“logs.ldk” and “logs.ldr”) from an attacker-controlled server by the use of a PowerShell script. The primary of the 2 recordsdata, “logs.ldk,” is a DLL that is chargeable for writing a secondary Visible Primary Script to disk, utilizing it to ascertain persistence utilizing a scheduled job by passing it off as “Skype Updater” to evade detection.
This Visible Primary Script comprises the identical PowerShell logic noticed initially of the assault. The scheduled job ensures that the payload is robotically executed after each login.
The PowerShell script, apart from loading “logs.ldk” as a .NET meeting, passes “logs.ldr” as enter to the loaded meeting, resulting in the execution of a binary (“AsyncClient.exe”), which is the AsyncRAT payload with capabilities to log keystrokes, steal browser credentials , fingerprint the system, and scan for put in cryptocurrency pockets desktop apps and browser extensions in Google Chrome, Courageous, Microsoft Edge, Opera, and Mozilla Firefox.
All this collected info is finally exfiltrated to a command-and-control (C2) server (“3osch20.duckdns[.]org”) over a TCP socket, to which the malware beacons so as to execute payloads and obtain post-exploitation instructions. The C2 connection settings are both hard-coded or pulled from a distant Pastebin URL.
“Fileless malware continues to pose a big problem to trendy cybersecurity defenses as a consequence of its stealthy nature and reliance on authentic system instruments for execution,” LevelBlue stated. “In contrast to conventional malware that writes payloads to disk, fileless threats function in reminiscence, making them more durable to detect, analyze, and eradicate.”