Jul 03, 2025Ravie LakshmananThreat Intelligence / Vulnerability
The French cybersecurity company on Tuesday revealed that a lot of entities spanning governmental, telecommunications, media, finance, and transport sectors within the nation had been impacted by a malicious marketing campaign undertaken by a Chinese language hacking group by weaponizing a number of zero-day vulnerabilities in Ivanti Cloud Companies Equipment (CSA) units.
The marketing campaign, detected in the beginning of September 2024, has been attributed to a definite intrusion set codenamed Houken, which is assessed to share some stage overlaps with a risk cluster tracked by Google Mandiant underneath the moniker UNC5174 (aka Uteus or Uetus).
“Whereas its operators use zero-day vulnerabilities and a complicated rootkit, additionally they leverage a large variety of open-source instruments largely crafted by Chinese language-speaking builders,” the French Nationwide Company for the Safety of Data Methods (ANSSI) stated. “Houken’s assault infrastructure is made up of various parts — together with industrial VPNs and devoted servers.”
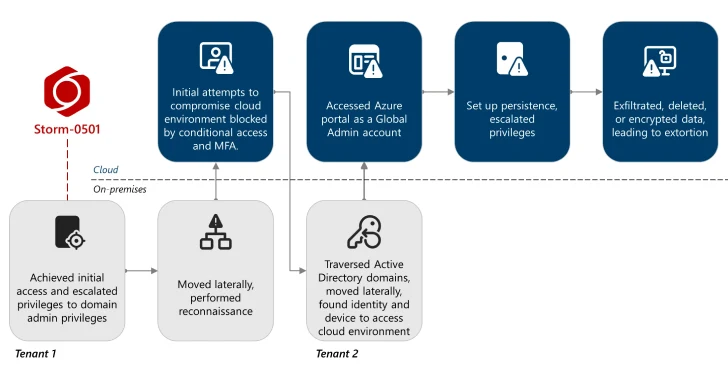
The company theorized that Houken is probably going being utilized by an preliminary entry dealer since 2023 with an intention to realize a foothold into goal networks after which shared with different risk actors involved in finishing up follow-on post-exploitation actions, reflective of a multi-party method to vulnerability exploitation, as identified by HarfangLab.
“A primary occasion identifies vulnerabilities, a second makes use of them at scale to create alternatives, then accesses are distributed to 3rd events which additional try and develop targets of curiosity,” the French cybersecurity firm famous earlier this February.
“The operators behind the UNC5174 and Houken intrusion units are doubtless primarily in search of helpful preliminary accesses to promote to a state-linked actor in search of insightful intelligence,” the company added.
In current months, UNC5174 has been linked to the lively exploitation of SAP NetWeaver flaws to ship GOREVERSE, a variant of GoReShell. The hacking crew has additionally leveraged vulnerabilities in Palo Alto Networks, Connectwise ScreenConnect, and F5 BIG-IP software program previously to ship the SNOWLIGHT malware, which is then used to drop a Golang tunneling utility known as GOHEAVY.
One other report from SentinelOne attributed the risk actor to an intrusion towards a “main European media group” in late September 2024.
Within the assaults documented by ANSSI, the attackers have been noticed exploiting three safety defects in Ivanti CSA units, CVE-2024-8963, CVE-2024-9380, and CVE-2024-8190, as zero-days to acquire credentials and set up persistence utilizing one of many three strategies –
Straight deploying PHP net shells
Modifying present PHP scripts to inject net shell capabilities, and
Putting in a kernel module that serves as a rootkit
The assaults are characterised by means of publicly out there net shells like Behinder and neo-reGeorg, adopted by the deployment of GOREVERSE to keep up persistence after lateral actions. Additionally employed is an HTTP proxy tunneling software known as suo5 and a Linux kernel module named “sysinitd.ko” that was documented by Fortinet in October 2024 and January 2025.
“It’s composed of a kernel module (sysinitd.ko) and a user-space executable file (sysinitd) put in on the focused gadget by the execution of a shell script: set up.sh,” ANSSI stated. “By hijacking inbound TCP site visitors over all ports, and invoking shells, sysinitd.ko and sysinitd permit the distant execution of any command with root privileges.”
That is not all. Moreover conducting reconnaissance and working within the UTC+8 time zone (which corresponds to China Customary Time), the attackers have been noticed trying to patch the vulnerabilities, prone to forestall exploitation by different unrelated actors, ANSSI added.
It is suspected that the risk actors have a large concentrating on vary, comprising governmental and schooling sectors in Southeast Asia, non-governmental organizations positioned in China, together with Hong Kong and Macau, and governmental, defence, schooling, media or telecommunication sectors within the West.
On prime of that, the tradecraft similarities between Houken and UNC5174 have raised the chance that they’re operated by a typical risk actor. That having stated, at the very least in a single incident, the risk actors are stated to have weaponized the entry to deploy cryptocurrency miners, underscoring their monetary motivations.
“The risk actor behind the Houken and UNC5174 intrusion units may correspond to a non-public entity, promoting accesses and worthwhile information to a number of state-linked our bodies whereas in search of its personal pursuits main profitable oriented operations,” ANSSI stated.
Discovered this text attention-grabbing? Observe us on Twitter and LinkedIn to learn extra unique content material we submit.