Aug 05, 2025Ravie LakshmananSocial Engineering / Malware
A mixture of propagation strategies, narrative sophistication, and evasion methods enabled the social engineering tactic referred to as ClickFix to take off the best way it did over the previous yr, in keeping with new findings from Guardio Labs.
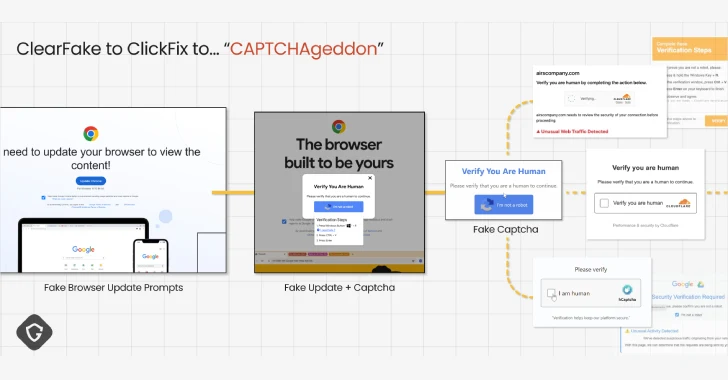
“Like a real-world virus variant, this new ‘ClickFix’ pressure shortly outpaced and finally worn out the notorious faux browser replace rip-off that plagued the net simply final yr,” safety researcher Shaked Chen mentioned in a report shared with The Hacker Information.
“It did so by eradicating the necessity for file downloads, utilizing smarter social engineering techniques, and spreading by trusted infrastructure. The consequence – a wave of infections starting from mass drive-by assaults to hyper-targeted spear-phishing lures.”
ClickFix is the title given to a social engineering tactic the place potential targets are deceived into infecting their very own machines below the guise of fixing a non-existent difficulty or a CAPTCHA verification. It was first detected within the wild in early 2024.
In these assaults, an infection vectors as various as phishing emails, drive-by downloads, malvertising, and search engine marketing (search engine optimisation) poisoning are employed to direct customers to faux pages that show the error messages.
These messages have one aim: Information victims to observe a collection of steps that trigger a covertly copied malicious command to their clipboard to be executed when pasted on the Home windows Run dialog field or the Terminal app, within the case of Apple macOS.
The nefarious command, in flip, triggers the execution of a multi-stage sequence that ends in the deployment of varied sorts of malware, comparable to stealers, distant entry trojans, and loaders, underscoring the pliability of the risk.
The tactic has change into so efficient and potent that it has led to what Guardio calls a CAPTCHAgeddon, with each cybercriminal and nation-state actors wielding it in dozens of campaigns in a brief span of time.
ClickFix is a extra stealthy mutation of ClearFake, which entails leveraging compromised WordPress websites to serve faux browser replace pop-ups that, in flip, ship stealer malware. ClearFake subsequently went on to include superior evasion techniques like EtherHiding to hide the next-stage payload utilizing Binance’s Good Chain (BSC) contracts.
Guardio mentioned the evolution of ClickFix and its success is the results of fixed refinement when it comes to propagation vectors, the diversification of the lures and messaging, and the totally different strategies used to get forward of the detection curve, a lot in order that it finally supplanted ClearFake.
“Early prompts had been generic, however they shortly turned extra persuasive, including urgency or suspicion cues,” Chen mentioned. “These tweaks elevated compliance charges by exploiting fundamental psychological strain.”
Among the notable methods the assault method has tailored embody the abuse of Google Scripts to host the faux CAPTCHA flows, thereby leveraging the belief related to Google’s area, in addition to embedding the payload inside legitimate-looking file sources like socket.io.min.js.
“This chilling record of methods – obfuscation, dynamic loading, legitimate-looking recordsdata, cross-platform dealing with, third-party payload supply, and abuse of trusted hosts like Google – demonstrates how risk actors have repeatedly tailored to keep away from detection,” Chen added.
“It’s a stark reminder that these attackers will not be simply refining their phishing lures or social engineering techniques however are investing closely in technical strategies to make sure their assaults stay efficient and resilient towards safety measures.”