Jun 12, 2025Ravie LakshmananVulnerability / Software program Safety
ConnectWise has disclosed that it is planning to rotate the digital code signing certificates used to signal ScreenConnect, ConnectWise Automate, and ConnectWise distant monitoring and administration (RMM) executables attributable to safety considerations.
The corporate mentioned it is doing so “attributable to considerations raised by a third-party researcher about how ScreenConnect dealt with sure configuration information in earlier variations.”
Whereas the corporate didn’t publicly elaborate on the character of the issue, it has shed extra mild in a personal FAQ accessible solely to its clients (and later shared on Reddit) –
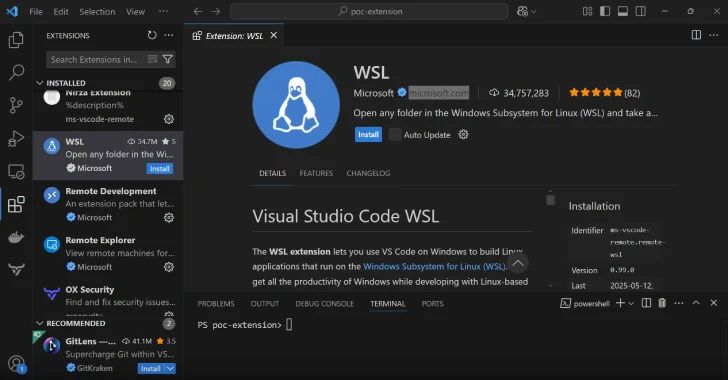
The priority stems from ScreenConnect utilizing the flexibility to retailer configuration information in an obtainable space of the installer that’s not signed however is a part of the installer. We’re utilizing this capacity to cross down configuration data for the connection (between the agent and server) such because the URL the place the agent ought to name again with out invalidating the signature. The unsigned space is utilized by our software program and others for personalization, nonetheless, when coupled with the capabilities of a distant management answer, it may create an insecure design sample by right now’s safety requirements.
Apart from issuing new certificates, the corporate mentioned it is releasing an replace that is designed to enhance how the aforementioned configuration information is managed in ScreenConnect.
The revocation of digital certificates is predicted to happen by June 13 at 8 p.m. ET (June 14, 12 a.m. UTC). ConnectWise has emphasised that the problem doesn’t contain a compromise of its programs or certificates.
It is price noting that mechanically ConnectWise is already within the strategy of updating certificates and brokers throughout all its cloud situations of Automate and RMM.
Nonetheless, these utilizing on-premise variations of ScreenConnect or Automate are required to replace to the newest construct and validate that each one brokers are up to date earlier than the cutoff date to keep away from any potential service disruptions.
“We had already deliberate enhancements to certificates administration and product hardening, however these efforts at the moment are being applied on an accelerated timeline,” ConnectWise mentioned. We perceive this may increasingly create challenges and are dedicated to supporting you thru the transition.”
The event comes merely days after the corporate disclosed {that a} suspected nation-state risk actor breached its programs and affected a small variety of its clients by exploiting CVE-2025-3935 to conduct ViewState code injection assaults.
It additionally comes as attackers are more and more counting on reliable RMM software program like ScreenConnect and others to acquire stealthy, persistent distant entry, successfully permitting them to mix in with regular exercise and fly underneath the radar.
This assault methodology, known as living-off-the-land (LotL), makes it potential to hijack the software program’s inherent capabilities for distant entry, file switch, and command execution.
Discovered this text attention-grabbing? Comply with us on Twitter and LinkedIn to learn extra unique content material we publish.