In January 2025, cybersecurity consultants at Wiz Analysis discovered that Chinese language AI specialist DeepSeek had suffered a knowledge leak, placing greater than 1 million delicate log streams in danger.
In keeping with the Wiz Analysis staff, they recognized a publicly accessible ClickHouse database belonging to DeepSeek. This allowed “full management over database operations, together with the flexibility to entry inside information”, Wiz Analysis acknowledged, with greater than one million strains of log streams concerned, containing chat historical past, secret keys and extra.
Wiz instantly reported the problem to DeepSeek, which rapidly secured the publicity. Nonetheless, the incident underscored the hazard of knowledge leakage.
Intentional or unintentional?
Knowledge leakage is a broad idea, overlaying a variety of eventualities. As IBM notes, the time period basically refers to a state of affairs the place “delicate info is unintentionally uncovered to unauthorized events”.
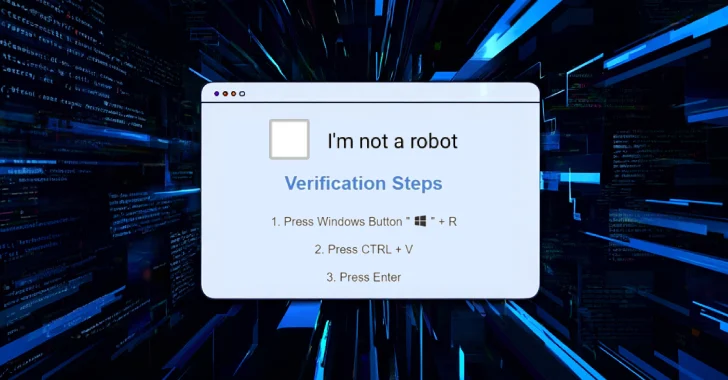
It could possibly be intentional or unintentional. On the intentional aspect, for example, hackers may use phishing or social engineering methods to govern a corporation’s staff into exposing their private information.
There’s even the chance of an insider threats: for example, a employee with a grudge who seeks to compromise programs, maybe for monetary profit or as a part of some quest for revenge.
However unintentional leakage is simply as huge a priority. This could possibly be a case of easy human error: sending an e-mail to the improper individual or offering an excessive amount of info to a 3rd occasion for instance.
There are a variety of frequent vectors – we’ll run by only a few.
Misconfigured cloud storage
Cloud misconfigurations could be a frequent trigger of knowledge leakage. The Cloud Safety Alliance highlights the hazard from easy errors, like leaving default passwords in place or failing to correctly configure entry controls.
Endpoint vulnerabilities
Knowledge processed by {hardware} like unencrypted laptops or saved in units reminiscent of USBs could be a key vulnerability for leakage; it’s vital that staff are conscious of – and observe – organizational safety insurance policies to mitigate this danger.
Emails and messaging
There’s an actual hazard that information could be intercepted: this might come from a easy error (sending a delicate attachment to the improper deal with) or by a deliberate assault. Sturdy encryption is crucial to make sure it stays in the proper fingers.
Shadow IT
Staff usually use their very own IT as a part of their each day working lives (reminiscent of exterior cloud applied sciences), together with for information storage. Whereas this isn’t usually malicious, it could actually make danger administration harder, notes the UK’s Nationwide Cyber Safety Centre (NCSC), “since you gained’t have a full understanding of what it’s essential defend and what you worth most.”
Monetary and authorized issues
There are a number of frequent drivers of knowledge leakage, starting from weak entry controls to a scarcity of data-classification insurance policies, inadequate monitoring, and insufficient worker coaching. However irrespective of the precise trigger, the implications could be devastating.
For instance, regulatory authorities all over the world now implement strict information safety insurance policies, which may end up in enormous fines for organizations that fail to conform; this contains the EU’s Common Daa Safety Regulation (GDPR) and the California Shopper Privateness Act (CCPA).
There’s additionally the broader danger of dropping mental property (IP) or different delicate firm info. Crimes like bank card fraud may stem from a leak, whereas public corporations may even see a fall of their share worth.
Maybe most significantly, failing to guard worker and buyer information may have a devastating affect on a corporation’s repute, with long-term unfavorable implications for the enterprise.
Constructing your defenses
So how can organizations defend themselves, their staff and their prospects from the risks of knowledge leakage? Listed here are some key approaches:
Implement least-privilege entry: By granting customers entry solely to the info they should carry out their job, the ‘blast radius’ of a breach or leakage will likely be considerably diminished.
Pursue information loss prevention (DLP): This can be a wide-ranging answer, combining applied sciences like AI and antivirus software program with methods and actions centered on folks and processes, all with the goal of figuring out and stopping data-connected hurt.
Classify delicate information: Safety begins with data. Develop an intensive understanding of your riskiest information to make sure you know the place to prioritize your safety implementation.
Audits: Via each exterior audit checks and a complete inside audit program, organizations can enhance their probabilities of figuring out potential vulnerabilities.
Coaching: After all, no technical answer or operational enhancement can succeed with out full worker engagement and understanding. Satisfactory coaching will guarantee your employees and different stakeholders are in control, whereas engagement might even produce new insights into vulnerabilities and mitigation methods.
CompassDRP: Detect leaked information
As your digital assault floor grows, so does the chance of knowledge leakage. Outpost24’s CompassDRP helps organizations handle this increasing risk surroundings, with a key module centered on information leakage.
The characteristic has essential purposes for a lot of companies. These embody:
Detect probably leaked paperwork or confidential information: Customers usually depend on unauthorized or misconfigured purposes to share paperwork and generally confidential information with prospects or colleagues. The Knowledge Leakage characteristic is designed to detect such instances throughout quite a few sources, together with doc repositories.
Detect probably leaked supply code: Such leakages may reveal inside info to an attacker, together with IP and even the authentication tokens within the code. The Knowledge Leakage characteristic searches code repositories to detect these leaks.
Organizations of all sizes take care of rising volumes of knowledge immediately. This can be a enormous benefit, serving to collect insights into your enterprise and your buyer base. Nonetheless, it additionally poses dangers, as we’ve seen.
By embracing technological innovation and operational enhancements, you’ll be able to assist guarantee your group realizes the numerous advantages of this info with out succumbing to the risks and dear penalties of knowledge leakage. Ebook a CompassDRP stay demo.
Discovered this text attention-grabbing? This text is a contributed piece from considered one of our valued companions. Observe us on Google Information, Twitter and LinkedIn to learn extra unique content material we publish.