Jul 01, 2025Ravie LakshmananVulnerability / Browser Safety
Google has launched safety updates to deal with a vulnerability in its Chrome browser for which an exploit exists within the wild.
The zero-day vulnerability, tracked as CVE-2025-6554 (CVSS rating: N/A), has been described as a kind complicated flaw within the V8 JavaScript and WebAssembly engine.
“Sort confusion in V8 in Google Chrome previous to 138.0.7204.96 allowed a distant attacker to carry out arbitrary learn/write through a crafted HTML web page,” based on an outline of the bug on the NIST’s Nationwide Vulnerability Database (NVD).
Sort confusion vulnerabilities can have extreme penalties as they are often exploited to set off sudden software program conduct, ensuing within the execution of arbitrary code and program crashes.Zero-day bugs like this are particularly dangerous as a result of attackers usually begin utilizing them earlier than a repair is obtainable. In real-world assaults, these flaws can let hackers set up spyware and adware, launch drive-by downloads, or quietly run dangerous code — generally simply by getting somebody to open a malicious web site.
Clément Lecigne of Google’s Risk Evaluation Group (TAG) has been credited with discovering and reporting the flaw on June 25, 2025, indicating that it could have been weaponized in extremely focused assaults.The involvement of Google’s Risk Evaluation Group usually alerts that an exploit could also be linked to focused assaults — probably involving nation-state actors or surveillance operations. TAG usually investigates severe threats like phishing campaigns, zero-click exploits, or makes an attempt to bypass browser sandboxing.
The tech large additionally famous that the difficulty was mitigated the following day by way of a configuration change that was pushed out to the Steady channel throughout all platforms. For on a regular basis customers, which means the menace might not be widespread but, nevertheless it’s nonetheless pressing to patch — particularly in the event you’re in roles dealing with delicate or high-value knowledge.
Google has not launched any extra particulars concerning the vulnerability and who could have exploited it, however acknowledged that “an exploit for CVE-2025-6554 exists within the wild.”
CVE-2025-6554 is the fourth zero-day vulnerability in Chrome to be addressed by Google because the begin of the 12 months after CVE-2025-2783, CVE-2025-4664, and CVE-2025-5419. Nevertheless, it bears noting that there isn’t a readability on whether or not CVE-2025-4664 has been abused in a malicious context.
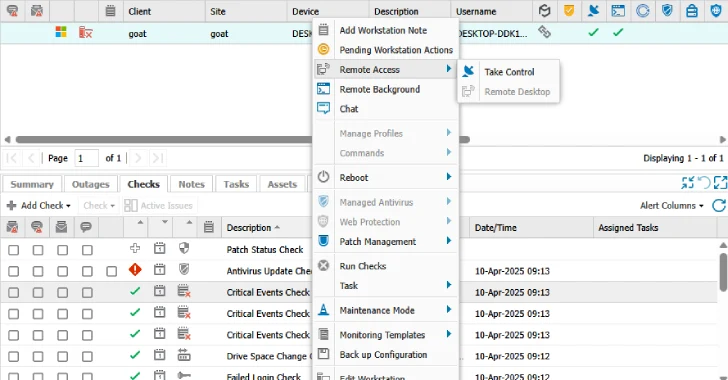
To safeguard towards potential threats, it is suggested to replace their Chrome browser to variations 138.0.7204.96/.97 for Home windows, 138.0.7204.92/.93 for macOS, and 138.0.7204.96 for Linux.For those who’re uncertain whether or not your browser is updated, go to Settings > Assist > About Google Chrome — it ought to set off the most recent replace routinely. For companies and IT groups managing a number of endpoints, enabling computerized patch administration and monitoring browser model compliance is vital.
Customers of different Chromium-based browsers akin to Microsoft Edge, Courageous, Opera, and Vivaldi are additionally suggested to use the fixes as and once they turn out to be out there.
Discovered this text attention-grabbing? Observe us on Twitter and LinkedIn to learn extra unique content material we submit.