Jun 24, 2025Ravie LakshmananCloud Safety / Cryptojacking
Misconfigured Docker situations are the goal of a marketing campaign that employs the Tor anonymity community to stealthily mine cryptocurrency in inclined environments.
“Attackers are exploiting misconfigured Docker APIs to achieve entry to containerized environments, then utilizing Tor to masks their actions whereas deploying crypto miners,” Development Micro researchers Sunil Bharti and Shubham Singh stated in an evaluation printed final week.
In utilizing Tor, the concept is to anonymize their origins in the course of the set up of the miner on compromised techniques. The assaults, per the cybersecurity firm, begin with a request from the IP deal with 198.199.72[.]27 to acquire an inventory of all containers on the machine.
If no containers are current, the attacker proceeds to create a brand new one based mostly on the “alpine” Docker picture and mounts the “/hostroot” listing – i.e., the foundation listing (” of the bodily or digital host machine – as a quantity inside it. This conduct poses safety dangers because it permits the container to entry and modify recordsdata and directories on the host system, leading to a container escape.
The menace actors then execute a rigorously orchestrated sequence of actions that includes working a Base64-encoded shell script to arrange Tor on the container as a part of the creation request and finally fetch and execute a distant script from a .onion area (“wtxqf54djhp5pskv2lfyduub5ievxbyvlzjgjopk6hxge5umombr63ad[.]onion”)
“It displays a standard tactic utilized by attackers to cover command-and-control (C&C) infrastructure, keep away from detection, and ship malware or miners inside compromised cloud or container environments,” the researchers stated. “Moreover, the attacker makes use of ‘socks5h’ to route all site visitors and DNS decision by Tor for enhanced anonymity and evasion.”
As soon as the container is created, the “docker-init.sh” shell script is deployed, which then checks for the “/hostroot” listing mounted earlier and modifies the system’s SSH configuration to arrange distant entry by enabling root login and including an attacker-controlled SSH key into the ~/.ssh/authorized_keys file.
The menace actor has additionally been discovered to put in varied instruments like masscan, libpcap, zstd, and torsocks, beacon to the C&C server particulars concerning the contaminated system, and finally ship a binary that acts as a dropper for the XMRig cryptocurrency miner, together with the mandatory mining configuration, the pockets addresses, and mining pool URLs.
“This strategy helps attackers keep away from detection and simplifies deployment in compromised environments,” Development Micro stated, including it noticed the exercise focusing on expertise firms, monetary providers, and healthcare organizations.
The findings level to an ongoing pattern of cyber assaults that focus on misconfigured or poorly secured cloud environments for cryptojacking functions.
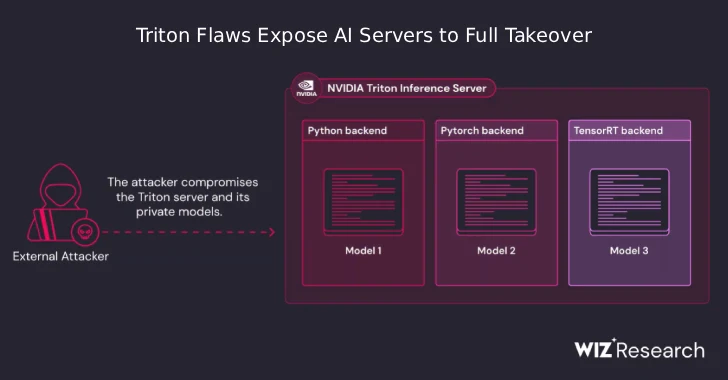
The event comes as Wiz revealed {that a} scan of public code repositories has uncovered a whole lot of validated secrets and techniques in mcp.json, .env, and AI agent configuration recordsdata and Python notebooks (.ipynb), turning them right into a treasure trove for attackers.
The cloud safety agency stated it discovered legitimate secrets and techniques belonging to over 30 firms and startups, together with these belonging to Fortune 100 firms.
“Past simply secrets and techniques, code execution ends in Python notebooks must be usually handled as delicate,” researchers Shay Berkovich and Rami McCarthy stated. “Their content material, if correlated to a developer’s group, can present reconnaissance particulars for malicious actors.”
Discovered this text fascinating? Observe us on Twitter and LinkedIn to learn extra unique content material we publish.